Who Governs Government AI? The Challenge of Federal Implementation
Public Trust and the Stakes of Federal AI Regulation
Americans are skeptical that their government can regulate artificial intelligence. A Pew Research Center study from October 2025 found that while large majorities in countries like India (89%), Indonesia (74%), and Israel (72%) trust their governments to regulate AI effectively, only 44% of Americans say the same, and a greater number, 47%, express distrust. Globally, more people trust the European Union (53%) to regulate AI than the United States (37%). Americans will only realize the benefits of AI if they have confidence that these systems are used safely, fairly, and in ways that improve their lives.
Trust is not a soft concern: it is the foundation for the adoption, legitimacy, and long-term success of any technology. When people doubt that AI systems are governed responsibly, they are less likely to accept their use in sensitive domains like healthcare, education, public benefits, or national security. Public skepticism can slow innovation, undermine compliance, and deepen polarization around emerging technologies. Encouragingly, this is not a partisan issue. Republicans and Democrats alike have emphasized that trustworthy AI use is a prerequisite for public adoption and lasting legitimacy. If the U.S. is going all-in on AI, then building and maintaining that trust is therefore not simply a communications challenge; it is a governance imperative.
The federal government plays a starring role in meeting that imperative—not only as a regulator, but also as a model user of AI. It deploys some of the most consequential and high-risk AI systems, including those that shape access to benefits, guide law enforcement priorities, manage immigration processes, and support national security decisions. The federal approach to deploying these systems does more than affect service delivery or cost savings; it sets expectations for industry standards, academic research, and public perception of the technology. In effect, the federal government serves as a societal-level proving ground for AI governance. Because it uses AI in high-risk contexts, it must demonstrate that these systems can be governed effectively through transparency, oversight, accountability, and meaningful safeguards. Failure to do so would not only diminish confidence in AI as an economic and societal asset, but weaken the already tenuous trust the public has in government as a manager of risk and opportunity
Two use cases illustrate this point. One existing high-potential but high-risk application is the Veteran’s Administration’s (VA) REACH VET program, which uses predictive models to identify veterans at elevated suicide risk so clinicians can proactively reach out. Because it draws on health records and includes explicit race coding, one would be concerned about opaque modeling choices and the possibility of inequitable or incorrect flags. The stakes are high. If veterans feel that an algorithm is driving interventions without clear transparency, clinical guardrails, and accountability or if it misses potential intervention needs, trust can erode, not only in REACH VET but in the VA’s broader use of AI, and its mental health screening and treatment programs.
Planned uses of AI in the current administration are also concerning. CMS’s planned Medicare WISeR Model would test whether “enhanced technologies,” including AI, can “expedite the prior authorization processes for select items and services that have been identified as particularly vulnerable to fraud, waste, and abuse, or inappropriate use.” In practice, this could result in automated systems delaying or denying coverage for medically necessary prescriptions or treatments if a model incorrectly flags them as suspicious. The trust risk is immediate: prior authorization already feels like a barrier to care, and adding AI without appropriate guardrails or adjudication can make delays or denials seem more automated, less explainable, and more complicated to challenge, especially for older or medically complex beneficiaries. If people perceive AI as prioritizing cost control over care, it will quickly undermine confidence in Medicare and in government AI more broadly.
These two use cases show how setting parameters around federal AI governance is not an abstract compliance exercise; it directly shapes whether people experience AI as a helpful tool or as an unaccountable gatekeeper in some of the most sensitive and consequential interactions they have with the government. Federal guidance on incorporating elements like risk assessments, inventory documentation, and recourse processes into agency deployment play an outsized role in fomenting trust in government use of AI.
Attempting to meet this challenge, both the Biden and Trump administrations have issued major federal guidance on how agencies should govern their use of AI. In 2024, the Biden administration’s Office of Management and Budget released OMB Memorandum M-24-10: Advancing Governance, Innovation, and Risk Management for Agency Use of Artificial Intelligence as part of their role in establishing how federal agencies operate and implement government-wide regulations. This memorandum set forth a government-wide framework for the responsible use of AI, including requirements for risk assessments, transparency, safeguards for high-impact systems, and clear waiver processes. However, we previously found that the growing body of AI-specific guidance, layered on top of existing procurement rules such as the Federal Acquisition Regulation (FAR), can be difficult for agencies and vendors to navigate, particularly when determining at what stage in the acquisition process risk and impact assessments should occur.
Last year, the Trump Administration’s OMB superseded OMB M-24-10 with new guidance: M-25-21: Accelerating Federal Use of AI through Innovation, Governance, and Public Trust. This memo includes elements similar to the Biden administration guidance but, because of its more flexible, agency-driven model, also makes consistent implementation more challenging. The shift toward greater agency discretion could be explained by the Administration’s emphasis on accelerating AI adoption and reducing centralized compliance requirements that could slow experimentation or deployment. Agencies now shoulder greater responsibility for building their own governance and compliance structures, a task that depends heavily on available resources and technical capacity. Well-funded agencies may be positioned to meet these expectations, while smaller or resource-constrained agencies, including those whose tools have the greatest impact on low-income or marginalized communities, may struggle to develop and implement the same safeguards. The result is a growing risk of fragmented governance across the federal landscape, with uneven protections for the people most affected by AI systems.
With this context in mind, it’s worth examining how each administration has approached the challenge of governing high-risk AI, and what these differences mean for agency accountability and public trust.
From “Rights- and Safety-Impacting” to “High-Impact”: A Change in Orientation
AI Risk Thresholds
OMB Guidance M-24-10, issued under the Biden administration, established a government-wide framework for identifying and managing artificial intelligence systems that pose elevated risks to rights or safety. The memo introduced two formal designations: “rights-impacting AI” and “safety-impacting AI.” Rights-impacting systems are those whose outputs serve as a principal basis for decisions or actions with legally significant effects on individuals’ civil rights, liberties, privacy, or equitable access to services such as housing, education, credit, or employment. Safety-impacting systems are those whose decisions or actions have the potential to significantly affect human life or well-being, the environment, critical infrastructure, or national and strategic assets.
Under the Trump administration, OMB M-25-21 replaced the dual “rights-impacting” and “safety-impacting” categories with a single unified definition of “high-impact AI.” This term covers any AI system whose “output serves as a principal basis for a decision or action that has legal, material, binding, or similarly significant effects on individuals or entities.” Examples still include systems affecting civil rights, access to government programs or resources, health and safety, critical infrastructure, or other vital assets. While the framework remains centered on AI systems that serve as a principal basis for consequential decisions, the new memo consolidates the prior rights- and safety-based categories into a single, more generalized standard.
This shift is not merely semantic. The way OMB defines high-risk or high-impact AI determines which federal agencies must apply heightened safeguards, conduct impact assessments, and implement specific oversight and accountability measures. It also signals to contractors, state and local governments, and private-sector partners the types of AI use that warrant the most stringent governance practices. As discussed below, consolidating the categories may affect the scope, clarity, and structure of minimum risk-mitigation requirements across agencies.
Minimum Risk Management Practices
Reaching a designated risk threshold, whether categorized as “rights- or safety-impacting” under the Biden administration or “high-impact” under the Trump Administration, does not bar an AI system from being used in government. Instead, both administrations require agencies to meet a set of minimum risk management practices before deploying such systems. These requirements, summarized in the table below, establish the baseline safeguards for high-risk AI use.
While there are consistent practices among both guidance documents, including AI impact assessments, ongoing monitoring and evaluation, and workforce training, there are a few elements noticeably absent from the Trump administration’s M-25-21. For example, the new guidance does not have opt-out considerations, has a looser procedure for remedies of high impact systems, and does not go into as much detail on what ongoing risk monitoring should look like. Independent review in the Biden administration formalized the inclusion of the Chief AI Officer (CAIO) or another agency advisory board, while the Trump administration has more flexibility in who can review high-impact use cases.
The Trump administration also differs in including a new element: pilot projects. These pilot AI programs are exempt from full risk-management requirements if they are limited in scale and duration, approved and centrally tracked by the agency’s Chief AI Officer, allow participants to opt in or out with proper notice when possible, and still apply risk-management practices wherever practicable.
Waivers
If, for whatever reason, agencies decide to not undergo the aforementioned minimum practices, both guidance documents offer waivers that give the agency’s CAIO authority to supersede a minimum risk practice. These waivers are centrally tracked and reported to OMB.
Whereas the Biden administration portrayed this as a procedural element, M-25-21 shifts the tone and purpose of these waivers. Under this system, an agency’s CAIO, in coordination with relevant officials, can grant a waiver from one or more of the minimum practices whenever strict compliance would impede mission-critical operations or increase overall risk. The memo explicitly allows waivers when compliance might “create an unacceptable impediment” to agency objectives, a broader, more permissive standard than under Biden.
By introducing a flexible pilot program model and more permissive and vague language risk management practices, the framework places substantial discretion in the hands of agencies and their CAIOs. In practice, agencies will exercise this discretion unevenly because they vary widely in governance maturity, technical capacity, and oversight infrastructure, an issue discussed in more detail below. These disparities are compounded by differences in how CAIO roles are structured across agencies: some CAIOs are career officials with dedicated staff and technical expertise, while others serve in an acting or dual-hatted capacity, combining AI oversight with unrelated portfolios and limited institutional support. The absence of uniform qualification requirements or minimum resource standards further increases the likelihood that implementation will diverge significantly across agencies.
Agency Snapshots: A Disjointed Compliance Landscape
Federal AI governance operates at two distinct levels: (1) centralized policy direction issued by OMB, and (2) agency-level compliance processes that operationalizes those policies. While policy sets uniform expectations, compliance is implemented through agency-specific procedures shaped by capacity, mission, and internal governance maturity. The interaction between these layers determines whether federal AI governance appears coherent or fragmented.
Under Trump’s OMB Memorandum M-25-21, every federal agency is required to publish both an AI Strategy and an AI Compliance Plan outlining how it will govern its high-impact AI systems and manage its waiver processes. The majority of these plans were published in September and October 2025. The following agencies provide a useful snapshot of how different parts of the government are approaching compliance with this guidance.
It is appropriate for agencies to develop risk evaluation approaches that reflect their distinct missions and deployment contexts. Sector-specific risks vary enormously: the harms posed by clinical decision-support tools differ from those associated with benefits administration, law enforcement, or worker-protection considerations. Agencies need the flexibility to evaluate risks within their own operational contexts.
However, differences in the content of sectoral risks and differences in the processes agencies use to manage those risks are not the same thing. Allowing agencies wide latitude in interpreting minimum risk management practices and in designing their waiver procedures creates the possibility of procedural divergence, not just divergence in substantive sector-specific requirements.This is where inconsistency becomes a governance problem, not just a technical one.
Agencies have long struggled to apply their own policies consistently across programs and time. A 2023 study of Biden-era AI governance practices found that fewer than 40 percent of mandated actions under key federal AI authorities were verifiably implemented, and that nearly half of federal agencies failed to publish required AI use-case inventories despite demonstrable use of machine-learning systems. Although the Trump administration may grant more discretion in agency AI governance, we see that the ability to consistently apply guidance is a structural issue that spans administrations. Without a baseline of procedural consistency, OMB may struggle in its mission to oversee these compliance plans.
The Importance of State Capacity
When each agency is left to design its own compliance architecture, implementation will also inevitably diverge according to capacity rather than mission need. This will produce a fragmented governance landscape that closely resembles the “patchwork” often cited as a concern in broader AI regulatory debates. Some agencies have already demonstrated the ability to produce relatively robust internal guidance because they possess deeper technical benches, established governance bodies, and more mature risk assessment processes. As shown in Table 2, for example, DHS has established centralized AI governance structures, published detailed AI inventories and use-case documentation, and built out internal review mechanisms to assess high-risk systems. Similarly, the DoL has developed agency-wide AI plans and formal oversight processes that integrate risk assessment, transparency, and workforce training components. But smaller, under-resourced agencies, such as the Court Services and Offender Supervision Agency (CSOSA) references in Table 1, may struggle even to stand up the foundational processes needed to comply with M-25-21.
At the core of this capacity gap is a workforce challenge. Effective AI governance depends not only on the right guidance but also on sufficient and well-deployed talent. This includes AI talent – staff with expertise in machine learning, data science, and model evaluation, and AI-enabling talent, which includes product managers, procurement specialists, privacy and civil liberties experts, domain specialists, and program managers who can integrate understanding of technical systems into real-world decisions and operations. AI governance bodies, risk assessment frameworks, and waiver adjudication processes cannot function without personnel who understand the technology and the agency’s mission context, and who can manage and adapt agency learning and implementation systems over time. A single brilliant CAIO is a smart first step, but long term effectiveness relies on the agency’s ability to enable a “flywheel” of adaptation, growing AI and AI enabling capacity over time.
The Biden administration had an AI Talent Surge with the explicit focus on bringing in AI and AI-enabling talent into the federal government, and was able to bring at least 200 experts into public service while advising agencies on structure and capacity-building. While M-25-21 prompts agencies to develop and retain AI and AI-enabling talent, it’s unclear how that matches up with the fact that 317,000 federal workers have left the government in 2025. Because many of the Biden-era AI hires were still within their probationary period, therefore vulnerable to layoffs, and because some entire digital teams, such as GSA’s 18F and the DHS’ own AI Corps, were slashed, it is now difficult to determine where federal AI talent resides or how much of that capacity remains in government.
Recent Trump administration moves have recognized some of this gap, but the emphasis on early-career vs. institutional adaptation is limiting. Late last year, the Office of Personnel Management issued a “Building the AI Workforce of the Future” guidance document, with emphasis on the launched TechForce (hiring early-career technologists for limited terms of two years), Project Management and Data Science Fellows programs, and other early-career oriented programs.
Conclusion
The divergence between M-24-10 and M-25-21, coupled with the uneven compliance plans that have followed, reveal a federal AI governance landscape marked by structural fragmentation, one that carries real implications for public trust. Agencies with robust technical resources are positioned to comply with these requirements if they choose to, while others will struggle to keep pace. Compounding this disparity, the dissolution of digital teams and loss of probationary AI hires have obscured the government’s understanding of its AI workforce, weakening its capacity to implement trusted and transparent governance.
Ultimately, M-25-21’s compliance plans will not fulfill their intended purpose unless agencies receive the funding, staffing, and political support required to carry them out. A compliance plan is only as strong as the people and resources behind it. Robust, transparent governance is impossible without investments in the civil service capacity needed to implement it, and without such trust-building capacity, agencies risk forgoing the responsible adoption of AI systems that could improve public services and operational effectiveness.
Igniting Innovation: Progress and a Path Forward for Wildfire Policy
Communities nationwide are experiencing longer wildfire seasons and more intense, destructive wildfires. Hotter and drier weather, decades of fire over-suppression leading to the buildup of flammable materials, and increasing development in and around fire-prone areas have transformed wildfire—once a natural and sustainable part of American landscapes—into a major threat. From California to New Jersey, wildfires are taking a toll—costing the United States up to $424 billion annually and displacing tens of thousands of people.
One year after catastrophic wildfires blazed through southern California, the Environmental and Energy Study Institute (EESI) and the Federation of American Scientists (FAS) held a Congressional briefing on emerging solutions to tackle the wildfire crisis and federal policy strategies for getting these solutions into the field. The briefing was followed by a reception co-hosted by FAS and Megafire Action.

The briefing featured four expert panelists who brought decades of experience building wildfire resilience from space, from sky, from the fireline, and from the law office.
- Kelly Martin (Megafire Action) discussed opportunities and challenges for homeowners and communities to build wildfire resilience, informed by what she saw on the ground in the aftermath of the LA wildfires.
- Annie Schmidt (Alliance for Wildfire Resilience) discussed the impacts of urban conflagrations on communities and explored risk reduction for a variety of impacts, expanding beyond traditional partnerships, and cross-cutting collaboration.
- Sara Clark (Shute, Mihaly & Weinberger) discussed the need for beneficial fire, articulated the difference between cultural burning, and highlighted how we can get more fire on the ground by addressing liability concerns; enabling cultural burning; and cutting “green tape.”
- Dr. Michael Falkowski (Earth Fire Alliance) discussed Earth Fire Alliance’s vision to deliver transformative data from all wildfires on earth and underscored it as an example of a public-private partnership for technology innovation.
The briefing came at a pivotal moment for U.S. wildfire policy. Since FAS started working on wildfire four years ago, we’ve helped to cultivate a growing coalition of partners who have elevated wildfire as an urgent concern in Congress, the White House, governors’ offices, and boardrooms. All of these stakeholders recognize that the wildfire crisis is solvable. FAS is proud to have been an early champion of the Fix Our Forests Act (S.1462), whose provisions would be a critical step in improving how we use science, data, and technology to build wildfire resilience. We’ve also seen the private sector and philanthropic investment supercharge innovation. And we’ve seen stakeholders, from insurance companies to utilities, recognizing the urgent need to act.
In a lively Q&A, panelists answered audience questions about how to act: how to incentivize home hardening, how the federal government can lead wildfire resilience, budget barriers to risk reduction, and more.
What we discussed
- Wildfires become urban conflagrations when homes and infrastructure become the fuel. The disaster in Los Angeles in January 2025 is an example of an urban conflagration that began in the wildland urban interface (WUI) and spread into a community. Some of the most devastating fires in modern history have been urban conflagrations. These kinds of fires are likely to worsen and happen more often if we don’t act.
- Resilience requires solutions in communities and in our environment. To effectively tackle the wildfire crisis, we must invest in risk reduction in both the built environment (e.g., home hardening, infrastructure retrofits) and the natural environment (e.g., prescribed fire and mechanical thinning). Science, data, and technology can support resilience across these domains.
- Solutions must be tailored to the needs of communities at risk and the unique relationships between ecosystems and wildfires. As Kelly Martin summarized, “not all trees are good, and not all fires are bad.”
FAS understands that how we govern science, data, and technology will play a huge role in determining whether we achieve wildfire resilience. We know a future of coexisting safely with beneficial fire is possible if we act with urgency, fidelity to science, and a collaborative spirit. FAS is pushing energetically towards this future and we look forward to continuing to work closely with Congress and with partners to that end.
A pre-mortem on OPM’s HR 2.0 initiative: Imagining failure in order to support success
Large-scale IT modernization projects fail with remarkable regularity. They fail in private companies with strong profit incentives and unified leadership. They fail in state and local governments with narrower missions and simpler constraints. And they fail — often spectacularly — in the federal government. Entire multibillion‑dollar industries exist precisely because implementing large, complex software, including Enterprise Resource Planning (ERP) systems, is hard: technically complex, organizationally disruptive, politically fraught, and culturally destabilizing.
OPM’s new HR 2.0 initiative is therefore entering hostile terrain by default. The initiative aspires to rationalize, consolidate, and modernize a sprawling thicket of federal human resources systems that has grown organically over half a century. It seeks to replace dozens of agency‑specific solutions, hundreds of interfaces, and innumerable manual workarounds with a standardized, interoperable, enterprise‑wide platform capable of supporting modern workforce management.
Those of us who have followed federal HR modernization for years desperately want this effort to succeed. The current HR IT landscape is costly, brittle, opaque, insecure, and increasingly misaligned with how the federal government needs to recruit, manage, pay, and deploy its workforce. As OPM has documented and independent research shows, the federal government likely wastes billions of dollars maintaining hundreds of systems that slow agencies down, force them to duplicate effort, and obfuscate rather than clarify the data required to make business and workforce decisions. Some of these systems are decades old and have been assessed as a high risk to government operations if they should fail. Modernization is no longer optional. It is a prerequisite for addressing mission delivery, workforce planning, and public trust.
But optimism is not a plan, and aspiration is not execution. In our experience, the greatest danger to large federal IT programs is not a lack of good intentions, but rather a failure to fully internalize how hard it is to succeed and avoid the missteps of the past. In that spirit, this paper adopts an intentionally uncomfortable posture: It is a pre‑mortem. Rather than waiting until a future GAO report, Inspector General audit, or congressional hearing explains why this effort underperformed, we imagine that possible failure mode now.
We assume — purely for analytical purposes — that OPM’s HR 2.0 initiative did not achieve its intended outcomes. From that hypothetical vantage, we ask:
- What were the most likely failure modes that doomed the effort?
- What could OPM, OMB, Congress, and agencies have done earlier to materially reduce those risks?
- What questions should OMB and OPM leadership be asking today to avoid that outcome?
OPM, agencies, and OMB have already invested substantial time and energy in planning this effort. This paper is intended to complement — not undermine — that work by surfacing structural vulnerabilities early, when they can still be addressed. This, in turn, can help guide implementation teams’ focus today under the presumption that success, with care and forethought, is possible despite all the barriers.
HR 2.0 is a good idea, but it has risks
At its core, OPM’s initiative is a good one and addresses an often-neglected part of the federal business enterprise that has long needed attention from senior leadership. It is also perhaps the most ambitious attempt ever made to solve this problem once and for all. In fact, OPM has made a series of choices related to how it has structured the program — decisions that demonstrate the administration’s seriousness and commitment, and we mostly agree with the impulse and meaning behind each of them:
- Single award – Currently, several different vendors service the federal government, including Oracle, SAP, and Workday. This creates interoperability and data standards challenges, as upgrades need to be made in each proprietary code-base when policies or directions change. OPM’s approach in HR 2.0 solves this by mandating a move to one, single software company, which can tightly integrate the entire federal enterprise into a standard solution that is easier and cheaper to maintain.
- Direct contracting with software OEM – Historically, when agencies moved to new systems, they contracted with a large system integrator (SI) that served as something of a middleman between the agency and the company that actually built the software. These SIs served as translators between the two groups: business requirements from agency to vendor, technical specifications from vendor to agency. However, this creates additional cost and management complexity as the agency relies on a third party to act in its interests. OPM’s approach in HR 2.0 solves this by establishing a direct contracting relationship between OPM and the eventual software vendor so that OPM can control vendor behavior and changes to the underlying single code-base.
- Recoup costs from agencies – There are a variety of models for funding mandatory government-wide services, including both specific appropriations and also pooling funds from agencies to a central account. For HR 2.0, OPM appears to be electing the latter, which gives agencies “skin in the game” and ownership of the resulting solution: They’re paying for it, so they are true customers rather than simply takers of OPM’s direction.
- Explicit direction to agencies – There are various ways to drive adoption of single solutions. OPM and OMB have elected to pursue a top-down, mandatory, whole-of-government approach that establishes a schedule and mandates adoption. This solves many common collective-action problems across government: No agency wants to go first and everyone would prefer to push the timeline out as far as possible.
However, we also know how hard this is going to be, both because of our own experience working on this topic inside the federal government ,and because the government has failed at this exact exercise before. In fact, it has already failed at this project this decade.
Learning from DoD’s failure
In March of 2025, Secretary of Defense Pete Hegseth released a memo and then a video highlighting an effort to cut wasteful spending and putting several programs on hold. The first program on his list was the Defense Civilian Human Resources Management System, or DCHRMS (pronounced dee-charms in classic defense bureaucracy style).
The program had been “intended to streamline a significant portion of the Department’s legacy Human Resources (HR) information technology stack – an important mission we still need to achieve – but further investment in the DCHRMS project would be throwing more good taxpayer money after bad.” In his telling, the program was “780 percent over budget. We’re not doing that anymore.” It was over — the DoD had tried and spectacularly failed to move to a single HR system for just its own department. This high-profile bust is exactly what we mean when we say this type of HR IT modernization is hard and fails all the time.
The project originally started in 2018 as a $36 million, one-year proof of concept and then morphed into a years-long effort to consolidate at least six separate DoD systems based on Oracle’s E-Business Suite software onto a single, DoD-wide Oracle Cloud HCM platform. The project moved from proof of concept into full execution without a formal acquisition or rigorous planning, leaving the systems integrator that managed the legacy systems also in charge of implementing the new system. The department tried mightily to standardize business processes across DoD services. But people familiar with the project say that middle managers and subject-matter experts across the department added requirements that led to scope creep as the project wore on. As the project timeline began slipping, Oracle introduced new technologies and features that led to further slippage to incorporate them into the program baseline. By the time the program was cancelled, it was not clear what DoD’s measures of success were. That the integrator responsible for deploying the new system was simultaneously profiting from operating the legacy systems also presented an obvious conflict of interest.
The DCHRMS saga maps several pitfalls associated with large-scale enterprise IT modernization programs. The failure to maintain a rigorous convergence baseline and guard against scope creep is one. That seems to have been compounded by a business model and accountability structure that were not well thought through or did not adhere to best practices. And ultimately, by the time it became clear that the program was unable to deliver concrete, measurable outcomes in a reasonable and well-defined timeframe, the state of technology had evolved, rendering the program’s initial targets irrelevant and forcing the program to rebaseline.
These reasons for failure are not unique to DCHRMS, nor are they unforeseeable. In fact, they are some of the most common failure modes that doom complicated, multi\stakeholder technology implementations in complex organizations. Not even the DoD’s generally deferential-to-leadership and can-do culture could overcome them.
Predicting failure modes and mitigating the risks
For OMB and OPM to avoid this fate for HR 2.0, they need to consider the possibility of failure and take the risks of their approach head on. DCHRMS was a good idea, too, but good ideas only get you out of the gate and not over the finish line.
Based on our experience, we’ve imagine what the failure modes might be; suggest mitigations; and, crucially, articulate the questions leaders should be asking today to try to avoid failure in the future.
Failure mode 1: The single-award strategy backfires, or Industry doth protest too much
Scenario: In early 2026, GSA awarded the government-wide contract to implement HR 2.0 to a single vendor after a competitive evaluation,but the project quickly went the way of JEDI. Within weeks, two unsuccessful offerors — gigantic tech companies with deep pockets and nothing to lose — filed protests with GAO, arguing that the evaluation criteria unfairly favored the awardee’s architecture and that OPM had failed to adequately consider total cost of ownership. GAO sustained one protest on narrow technical grounds, requiring a reevaluation. That process took months, during which a third vendor protested, alleging the revised criteria were designed to reverse-engineer the original outcome. By the time the litigation resolved in late 2027, OPM had lost its original program leadership, the vendor’s proposed technical team had largely dispersed to other projects, and three agencies that had been preparing for early implementation had redirected their modernization budgets elsewhere.
The single-award approach isn’t inherently flawed, but it demands unusual discipline in execution and presents significant risks. OPM and GSA must assume protests are coming and prepare accordingly, both legally and programmatically. Their goal should be twofold: make protests less likely to succeed on their merits, and structure the program so that even a sustained protest doesn’t collapse momentum entirely. Here’s how:
- Build legitimacy through transparency. Proactively explain the award decision to appropriators, GAO, industry associations, and agency stakeholders. When policymakers and others understand and accept the rationale, vendors have less political cover for delay tactics. This will set the stage for effective vendor debriefs as well.
- Build innovation incentives directly into task orders. Normally, the federal government drives innovation in its vendor base through competition: Companies compete to offer the mix of capabilities relative to price and are incentivized to lower their work margins. In a single-award model, OPM loses some of this competitive pressure to innovate. As a result, rather than assuming innovation will emerge organically as a result of market forces, OPM should explicitly reward it. This could include incentive fees tied to measurable improvements in usability, automation, or data quality, as well as structured mechanisms for piloting and scaling new capabilities.
- Protect exit options. Require data portability in nonproprietary formats and government ownership of custom code. Real exit options, even if unlikely to be exercised, weaken the “lock-in/lock-out” narrative that makes protests attractive.
- Maintain the ecosystem. A curated marketplace for ancillary solutions (i.e., microsolutions outside the scope of the current contract) keeps competitive pressure alive and gives losing vendors a reason to stay engaged with the federal government rather than litigate over the loss of their entire market share.
Key questions for OPM and OMB leadership to ask: What is our realistic timeline and budget for protest and litigation? And have we structured the program so that a significant delay won’t collapse momentum entirely?
Failure mode 2: An OPM-led, OPM-managed effort becomes a bottleneck or Herding Cats Is too Hard
Scenario: By mid-2027, the program had a governance problem that no one wanted to name. OPM had established an impressive array of boards, councils, and working groups, but decisions that should have taken days were taking months. Agency requests for configuration changes sat in queues. Escalation paths were unclear. When disputes reached senior leadership, they often got sent back for “more analysis.” Agencies, meanwhile, learned that the fastest path to resolution was to route around OPM entirely: calling OMB, complaining to appropriators, or simply delaying participation until someone else went first.
Centralizing authority at OPM makes sense in theory: It’s the government’s HR agency, and fragmented leadership doomed earlier efforts. But centralization only works if OPM has the capacity to actually lead, and if governance structures enable decisions rather than defer them when agencies push back — and they will push back. This requires deliberate investment in both institutional capability and stakeholder engagement:
- Build capacity before you need it. OPM will need staff profiles it hasn’t historically employed at scale: senior IT program executives, enterprise architects, contracting specialists, and financial managers. Borrowing talent through detailees can help initially, but durable capability requires permanent investment and new types of positions.
- Design governance for speed. Establish clear decision rights, escalation paths, and timelines at every tier. Linked governance bodies must cover the full range of strategy, policy, contracting, operations, stakeholder engagement, and performance. They should have authority to resolve issues, not just discuss them. When decisions are kicked up the ladder, there should be a deadline for resolution.
- Develop model interagency agreements (IAAs). Standardized IAAs with explicit service levels, cost allocation, and dispute resolution will reduce the transaction costs that otherwise consume leadership attention.
- Make agencies partners, not passengers. Leverage the Chief Human Capital Officers (CHCO) Council not only as a communication channel, but also as a genuine forum for surfacing concerns and shaping implementation. Agencies need to see that their expertise matters, even when their preferred approaches don’t prevail.
- Treat HR 2.0 as a product, not as a project. HR 2.0’s success relies not simply on the implementation of a new IT system, but on the ongoing evolution of the features and functionalities that will enable the system to respond to and meet the needs of agency users. The private sector, and increasingly parts of the government, have adopted a “product operation model” to manage around these constraints. OPM should leverage the considerable experience its HR Solutions organization has with this model and mindset to adopt many of these management principles for HR 2.0.
Key questions for OPM and OMB leadership to ask: Does OPM have — or can it rapidly build — the programmatic capacity to manage a government-wide implementation? Or will it need to partner more deeply with other organizations to fill critical gaps?
Failure mode 3: Contracting directly with OEMs goes awry, or Integrators were integral after all
Scenario: The idea was novel: contract directly with the software company, make it accountable for delivery, and relegate the big integrators to supporting roles. However, what no one fully appreciated was that the OEM had never run a federal program at this scale. Its government practice was built around licensing, not implementation. When agencies reached out to them directly, staff struggled to handle their dual role as client navigator and enforcer of standards. Meanwhile, the integrator subcontractors had little incentive to go beyond its narrowly defined task orders; It had learned from experience that exceeding scope meant absorbing risk. By 2028, the program had developed a peculiar dysfunction: The OEM nominally owned delivery but lacked the expertise to drive it, while the integrators who had the expertise lacked the authority or incentive to deploy it. Problems that should have been resolved at the working level instead became triangular disputes among OPM, the OEM, and whichever integrator happened to be nearby when something broke.
Contracting directly with the OEM aligns authority with product knowledge, a real advantage when implementation challenges stem from product limitations. But OEMs are product companies, not delivery organizations. Making this model work requires treating the OEM relationship as a partnership to be developed, not a vendor to be managed, and designing governance structures that compensate for predictable gaps. Here’s how:
- Conduct rigorous OEM due diligence. Go beyond product maturity to assess delivery capacity, federal acquisition experience, subcontractor management capability, and organizational culture. How does the OEM handle failure? How does it resolve disputes? What’s its approach to managing agency customers?
- Design governance as a “team of teams.” The OEM should orchestrate, not micromanage. Agencies and their integrator partners need clear roles and enough autonomy to solve problems without constant escalation. Decision rights should be explicit and documented.
- Stress-test capacity assumptions. OEMs may underestimate what federal implementation requires: cleared staff, program management depth, constant stakeholder engagement. Validate their staffing plans and scaling assumptions before award, during early execution, and down the stretch to avoid foreseeable issues.
- Anticipate finger-pointing and design around it. Establish clear responsibility matrices distinguishing product issues from configuration or data issues. Create joint risk registers and escalation paths that prioritize resolution over blame.
- Maintain a curated marketplace for extensions. Even the best core system won’t cover everything. OPM and the OEM should jointly certify integrator-built solutions to ensure they align with enterprise standards without stifling innovation.
Key Questions for OPM and OMB leadership to ask: Has the OEM ever successfully delivered a program of comparable scale and complexity? And if not, what governance structures will compensate for that inexperience?
Failure Mode 4: Configuration management becomes unmanageable, or The Christmas tree collapses under its own weight”
Scenario: No one could point to the moment the baseline stopped being a baseline. It happened gradually, one exception at a time. An agency with a unique pay authority needed a configuration variant; that was legitimate. Another agency’s union agreement required a different leave-tracking workflow; that was unavoidable. A third agency wanted to preserve a legacy-report format that its budget office depended on; that was easier to accommodate than to fight. By 2028, the “standard” system had 17 major configuration branches, 42 approved extensions, and an uncounted number of agency-specific workflows that had been implemented as “temporary” accommodations. The vendor’s upgrade cycle, originally planned for quarterly releases, slipped to annual. Even then, each upgrade required months of regression testing across configuration variants to ensure that push of new commercial code didn’t break these customizations. The government had succeeded in replacing dozens of legacy systems with a single modern platform. Unfortunately, it also had recreated the fragmentation that modernization was supposed to eliminate.
Configuration pressure is inevitable. Federal HR is governed by multiple statutory regimes, and agencies will always have legitimate reasons for divergence. Some amount of tailoring is inevitable, but the major goal OPM should consider is how it might govern the solution so that exceptions remain exceptions rather than becoming the new normal. This requires treating configuration management as a strategic discipline, not an administrative afterthought. Here’s how:
- Define the baseline clearly and defend it. Establish explicit standard processes and hold agencies to them unless divergence is legally required. “We’ve always done it this way” is not a sufficient justification.
- Create a hierarchy of tailoring options. Not all customization is equal. Advanced configuration within the product is preferable to extensions; extensions are preferable to bolt-on integrations; core product modifications should be rare and require executive approval.
- Sequence for simplicity. Start implementation with smaller, less complex agencies to establish guardrails before tackling organizations with intricate labor agreements and statutory exceptions.
- Use funding as a governance lever. Agencies should pay for tailoring beyond the baseline but only after accepting and implementing the standard. This creates natural friction against unnecessary divergence.
- Make configuration decisions transparent. Publish what’s been approved, what’s been denied, and why. Transparency counters the belief, widespread in government, that “everything we do is special.”
- Align with civil service reform. Configuration complexity is downstream of policy complexity. OPM and OMB should work with Congress to explain how statutory exceptions drive cost and discourage future proliferation.
Key Questions for OPM and OMB leadership to ask: Who has the authority to say “no” to an agency’s configuration request> And will those with that authority get backup when politically powerful agencies push back?
Failure mode 5: Funding is insufficient, unreliable, or unsustainable, or The passed hat drops
Scenario: The funding model mapped to a usual format for government: Agencies would pay for their participation, OPM would recover costs through its revolving fund, and the program would be self-sustaining once it reached scale. What the model hadn’t accounted for was the messy reality of federal budgeting. Three agencies requested implementation funding in their FY 2027 submissions; two were denied by their appropriations subcommittees, who saw HR modernization as discretionary against more pressing mission needs. A fourth agency had funds but couldn’t obligate them in time because its IAA with OPM was still being negotiated. By 2028, the program’s wave schedule had been revised four times, each revision eroding vendor confidence that the government was serious. The OEM, facing uncertain volume, quietly raised its per-agency pricing to hedge against lower-than-expected adoption. Agencies that had been on the fence used the chaos as justification to wait. OPM found itself in the worst of all positions: accountable for a government-wide program but dependent on agencies it couldn’t compel and appropriators it couldn’t control.
In the federal government, budgets are political documents as much as they are management ones. The way money flows determines who has authority, who bears risk, and who ultimately decides what gets built. A distributed funding model may be administratively orthodox, but it diffuses accountability in ways that are toxic to enterprise modernization. OPM and OMB should treat the funding architecture as a strategic design decision, not an inherited constraint. Here’s how:
- Seek direct appropriations for implementation. Congress should appropriate funds to OPM specifically for the implementation phase, with a defined transition to a revolving fund model for operations and maintenance. This gives OPM real authority to enforce configuration discipline and control sequencing without having to beg, borrow and steal from across government.
- Partner early with OMB and appropriators. Don’t wait for the budget cycle to explain why traditional funding models are ill-suited to enterprise transformation. Build the case now for why centralized implementation funding produces better outcomes at lower long-term cost, and take advantage of the opportunity to explain how viewing this initiative through a product management lens implies the need for a different funding strategy.
- Impose transparency on revolving fund operations. If agencies will eventually pay through the revolving fund, they need clear visibility into what they’re paying for. Publish cost drivers, configuration decisions, and tradeoff rationales.
- Plan for multi-year commitment. Seek multi-year appropriations where feasible. They reduce annual renegotiation risk and signal to vendors, agencies, and oversight bodies that the government is serious.
- Use funding to enforce sequencing. Agencies that want to delay should understand that funding availability may not wait for them. Early participation should carry advantages; late entry should carry costs.
Key Questions for OPM and OMB leadership to ask: Can this program realistically achieve its objectives through distributed agency funding? Or does success require a level of centralized financial authority that OPM does not currently have, at least at the implementation phase?
Failure Mode 6: Agencies are not ready when their turn comes, or Agencies miss their marks
Scenario: OPM and the OEM did their parts. The contract was awarded, governance was established, and the wave schedule was published 18 months in advance. What no one had fully reckoned with was the state of agency readiness. The first wave included 4agencies, chosen for their manageable size and expressed enthusiasm. Two were genuinely prepared: Their data was clean, processes were documented, and change management was underway. The other two had overestimated their readiness. One discovered during configuration that its position data existed in three different systems that had never been reconciled; cleaning it would take nine months. The other had documented its “as-is” processes, but those documents described how the agency thought things worked rather than how they actually worked, a gap that surfaced only when end users began testing. OPM faced an uncomfortable choice: delay the wave, which would ripple across the entire schedule; lower quality standards, which would embed problems into the baseline; or push forward and absorb the pain.
Agency readiness isn’t just an agency problem, it is also a program problem. OPM can execute flawlessly on procurement, governance, and vendor management and still fail if agencies aren’t prepared when their turn comes. That means readiness requirements need to be specific, measurable, and consequential. Agencies have incentives to obfuscate their readiness until it’s too late if they don’t think you’re serious or don’t understand what you’re asking them to do. OPM needs a clear escalation path if agencies miss their marks. Here’s how:
- Define clear readiness thresholds. Agencies need specific targets—data quality metrics, process documentation standards, and change management milestones—not general encouragement to “prepare.” These thresholds should be published early and tied explicitly to wave eligibility.
- Assess readiness independently. Self-reported readiness is unreliable. OPM should establish assessment mechanisms—whether internal or third-party—to validate agency preparation before committing to implementation dates.
- Make sequencing flexible. Wave schedules should be benchmarked against readiness, with the explicit expectation that agencies can be swapped based on objective criteria. Agencies that are ready should move forward; agencies that aren’t should wait.
- Provide resources for preparation. Readiness work requires investment—staff time, contractor support, leadership attention. OPM should issue detailed preparation guidance immediately upon award and establish contract vehicles for data cleanup, process reengineering, and change management.
- Incentivize early engagement. Agencies with complex needs should be encouraged to participate in early planning, even if they won’t implement in early waves. Early involvement confers influence and builds the expertise that makes later implementation smoother.
Key questions for leadership: How will OPM distinguish among agencies that are genuinely ready and those that merely believe they are? And what happens when an agency in the latter category is scheduled for an early wave?
Failure mode 7: Executive sponsorship wanes over time, or Government takes its eye off the ball
Scenario: For the first two years of the term, the program had everything it needed: White House attention, OMB backing, an OPM Director with the right skills who made modernization a personal priority, and agency heads who understood they were expected to participate. Then, as happens in nearly every term, political appointees began to turn over. New appointees came in after the midterms with different priorities. The career staff who understood the program’s history remained, but their authority to make decisions — and their air cover when those decisions were contested — evaporated. Agency executives who had reluctantly committed to early waves found that their objections now received a more sympathetic hearing. By 2028, the program still existed: contracts were in place, some agencies had implemented, governance bodies still met. But the urgency was gone. Wave schedules slipped. The program had become one of many initiatives rather than the initiative. It would eventually deliver something — but not the enterprise transformation that had been promised.
Executive attention is a wasting asset. It cannot be sustained indefinitely through personal commitment alone: Eventually, leaders move on, priorities shift, and attention migrates to newer challenges. The only way to protect a multi-year, multiadministration program is to convert early momentum into durable structures that don’t depend on any single leader’s continued engagement, and embed support for this program in the career staff who will need to sustain it across agencies far into the future.
- Codify governance beyond individuals. Decision rights, escalation paths, and performance standards should be documented and institutionalized, not dependent on personal relationships or informal understandings.
- Build a permanent career backbone. Political leadership is transient; career leadership is not. Invest in a cadre of SES leaders at OPM and participating agencies who understand the program’s full arc and are empowered to sustain it across transitions.
- Secure bipartisan congressional support. Frame the initiative as state-capacity investment, not an administration priority. Active engagement with authorizers and appropriators across parties is essential; without it, the program becomes vulnerable to being labeled discretionary or ideological.
- Lock in early wins. Move quickly to establish durable artifacts — contracts, standards, migrated agencies — that create facts on the ground. Reversal becomes harder when real implementation has occurred.
- Practice radical transparency. Publish progress, setbacks, costs, and tradeoffs. Transparency builds the credibility that sustains support across leadership transitions and reduces the risk that future leaders view the program as a black box inherited from predecessors.
Key question for OPM and OMB leadership to ask: What specific structures, commitments, and artifacts can be put in place in the next 18 months that would make it difficult for a future administration to abandon or significantly scale back this initiative?
OPM needs to manage the risk without paralyzing the program
All of these failure modes are, in our view, plausible but they are not inevitable. The fact that they’re extremely foreseeable makes them easier to plan around.
The good news is that the risks facing this initiative are not primarily technical. Whomever OPM selects as the vendor will likely be able to deliver some kind of working product. Rather, the risks are mostly governance risks, capacity risks, and incentive-alignment risks. The bad news is that these risks are harder to mitigate, and addressing them requires more than better requirements or more detailed project plans. It requires a conscious effort to design institutions, funding flows, and oversight mechanisms that help the program succeed rather than simply document its shortcomings.
With this in mind, there are some things that OPM and OMB can do to get a better hold on them. In particular, there are programmatic opportunities to rethink the use of independent verification and validation (IV&V) and the role of other actors in the federal ecosystem, such as Congress, GAO, and OMB, who often play their roles as overseers, authorizers, and advisers in the process of transformation. There are also obvious lessons from private sector product management experience that can help reduce the risk of a catastrophic meltdown posed by large-scale waterfall implementations.
Traditional IV&V models often emphasize exhaustive risk identification, which may be appropriate for discrete, bounded systems. However, for a multi-year, enterprise-scale transformation operating in a high-risk environment, a more useful IV&V strategy would be selective, staged, and decision oriented. Rather than attempting to monitor everything at once, IV&V should focus on a small number of high-leverage risk domains aligned with the failure modes identified in this paper, such as configuration governance and convergence discipline, funding adequacy and sustainability, agency readiness and sequencing decisions, and executive sponsorship and institutionalization. Within these domains, IV&V should aim not merely to assess compliance, but to inform real decisions: whether to pause, resequence, simplify, or escalate. Stage gating the implementation based on these factors (rather than just cost, schedule, and performance) can help OPM and OMB course correct when they need to rather than barrel ahead until it is too late.
In conjunction with this, OPM should lean into its relationship with stakeholders such as Congress and GAO. Agencies and program managers often avoid interacting with these officers because such interactions seem to invite scrutiny and criticism. But this program, with its size and ambition, will not avoid scrutiny along the way. And engaging these powerful actors earnestly up front offers OPM the best chance it will have to enlist them as allies and secure longer-term sponsorship for this important effort.
Finally, OPM should consider adopting a product operating model for HR 2.0 rather than managing it as a traditional, time-boxed “waterfall” IT project. As our colleagues have previously argued, the product operating model directly counteracts several of the failure modes identified in this paper. Replacing rigid milestone-based delivery with iterative development cycles reduces the risk of configuration complexity spiraling out of control, because problems surface early and can be corrected before they calcify into permanent accommodations. Embedding dedicated technical product managers within the program and empowering them to resolve ambiguity, manage scope, and make tradeoff decisions addresses the governance bottleneck risk by ensuring that day-to-day decisions don’t require constant escalation to senior leadership. Continuous, outcome-based funding aligned to a product model mitigates the funding fragility by shifting the budgetary conversation from one-time project appropriations to sustained investment in a living service. And because the product model emphasizes organizational alignment with outcomes rather than obstacles, it helps insulate the program against the loss of executive sponsorship: durable team structures, institutionalized feedback loops, and transparent progress metrics create continuity that persists even as political leadership turns over.
In short, the product operating model is an institutional design that would reduce the probability of several of the most dangerous failure scenarios HR 2.0 faces, and in doing so, increase the probability of historic success.
A Final Observation
Federal HR IT modernization is ambitious because it must be. The federal government is one of the largest single employers in the world and it runs on badly outdated and outclassed HR software. The status quo is unsustainable. Fragmentation, duplication, and opacity carry their own costs and risks. The choice, then, is not between risk and safety. It is between managed risk and unmanaged risk. The failure modes outlined in this paper are not predictions — they don’t have to come true — but they are warnings. Each represents a point at which deliberate choices can either compound fragility or build resilience.
The success of this initiative will depend less on technical execution than on leaders willing to confront these choices honestly, early, and repeatedly. That, more than any single procurement or platform decision, will determine whether HR 2.0 becomes a foundation for reform — or another cautionary tale about a federal IT meltdown…
Appendix: A brief history of HR IT modernization and consolidation in the federal government
Early agency‑built HR systems
Federal agencies, like their private sector counterparts, began building enterprise HR and payroll systems in the 1970s. These systems were typically bespoke, homegrown solutions designed to meet the specific needs of individual agencies. They were written in what was then state-of-the-art programming languages such as COBOL and Natural, languages that are now considered archaic, despite the fact that they continue to underpin mission‑critical systems in the banking industry and across government.
At the time, this approach made sense. Commercial HR software barely existed, and the federal government was already one of the largest employers in the world. Computing helped agencies manage complex, routine tasks like payroll and therefore were highly customized. There was little expectation that systems would interoperate across agencies, as the internet did not yet exist in its modern form. Each organization optimized for its own statutory authorities, workforce composition, and operational needs.
Over time, however, these systems accreted complexity. New laws, pay plans, labor agreements, and reporting requirements were layered on top of old code. Documentation decayed. Original developers retired and left little in the way of documentation about what they did. Institutional knowledge became increasingly fragile. What remained were systems that worked — until they didn’t — and that were extraordinarily difficult to modify, integrate, or retire.
The commercial ERP wave
In the 1990s, commercial ERP systems, led by vendors such as SAP and PeopleSoft, rose to prominence in the private sector. Initially focused on manufacturing and finance, these platforms gradually expanded to include HR, payroll, and talent management functionality for almost all large enterprises.
By the late 1990s, federal agencies began adopting commercial HR systems, overwhelmingly selecting PeopleSoft. These implementations promised modernization, vendor support, and alignment with private‑sector best practices. In practice, agencies often customized these systems extensively to replicate legacy processes and accommodate federal‑ and agency-specific requirements inherent in the custom solutions they replaced. While modernization occurred, standardization largely did not.
Payroll consolidation: A rare success
By the early 2000s, the federal government operated more than 20 mostly bespoke payroll systems, each of which did the same basic thing: calculate payroll and send instructions to the Department of the Treasury to process. This level of duplication was expensive and untenable, leading the Bush administration to adopt payroll consolidation as a pillar of its newly minted “e‑Government” agenda and the newly established HR Line of Business.
This effort is notable for both its sponsorship and its execution. The initiative was driven directly by OMB Director Mitch Daniels, with strong leadership from OPM Director Kay Coles James. OPM conducted a formal internal competition among federal payroll providers, resulting in the designation of four agencies — the General Services Administration, the Defense Finance and Acquisition Service (DFAS), the Department of Agriculture’s National Finance Center, and the Department of the Interior’s National (now Interior) Business Center — as payroll shared service providers, responsible for processing not only their own agency’s payroll but also that of several customer agencies. The Department of Agriculture, for example, processes payroll for the Departments of Homeland Security and Justice, while DFAS processes payroll for the Veterans Administration and the Department of Energy, among other arrangements.
Despite early skepticism and schedule slippage, payroll consolidation succeeded for the most part. By 2006–2007, most civilian agencies had migrated payroll operations to one of these providers. OPM later estimated that the effort produced roughly $1 billion in savings and cost avoidance, with continued benefits accruing over time, including better standardization and control over the data supply chain from agency systems to OPM.
Crucially, this payroll consolidation was not explicitly authorized by statute or executive order. It succeeded because senior leaders treated it as a management imperative, and they enforced compliance and sustained attention long enough to overcome institutional resistance.
The long plateau: 2007–2024
After payroll consolidation, OMB sought to extend the shared services model to broader HR functionality. Beginning in 2007, OMB issued a series of memoranda requiring agencies to migrate to approved HR shared service centers when modernizing. This policy trajectory culminated in OMB Memorandum M‑19‑16, which established Quality Service Management Offices for HR, financial management, grants management, and cybersecurity.
Despite these directives, progress was uneven. Some agencies modernized successfully; many did not. Fragmentation persisted. A defining feature of this period was the absence of sustained, senior‑level executive sponsorship comparable to that seen during payroll consolidation. HR IT modernization became a perennial priority — but rarely the top priority.
Gil on the Hill February 2026 – Appropriations: Signed, Sealed… Will It Be Delivered?
Implementation Season
January saw us watching whether the government would fund science. February has been about how that funding will be distributed, regulated, and contested.
Appropriations are (mostly) done. The shutdown clock has (mostly) stopped ticking. Congress, federal agencies, and the states are quietly settling into regular business for the year.
Let’s see what’s been going on.
Appropriations: Signed, Sealed… Will It Be Delivered?
As we’ve been tracking together, on January 23, the President signed into law the Commerce, Justice, Science; Energy and Water Development; and Interior and Environment Appropriations Act (H.R. 6938), locking in funding for core science accounts at the National Science Foundation (NSF), the Department of Energy (DOE), the National Aeronautics and Space Administration (NASA), and related agencies.
One week later, the Senate passed a bipartisan spending package funding most remaining agencies, including Defense, Health and Human Services (HHS), and Education, through September, while providing only a two-week stopgap for the Department of Homeland Security (DHS). That deadline has since come and gone, leaving DHS with lapsed funding and technically a partial government shutdown. With political ire as high as ever around Immigrations and Customs Enforcement (ICE) and high-profile incidents involving the deaths of U.S. citizens, it’s safe to assume we will not reach agreement on that front any time soon.
So, we avoided the shutdown cliff (mostly), but careful scrutiny about how (and how much) federal funding will be spent is the real point of contention now. Congress gives the money and the Administration is supposed to spend it. This has always been a given, but right now anyone with an interest in how federal funding is spent should be paying attention to the receipts coming in from the Administration.
For the science enterprise, a key takeaway is that topline federal funding stability comes bundled with increased reporting, compliance, and political scrutiny, but those measures still need to be tested outside of the confines of bill text and in the real world that Office of Management and Budget Director Russ Vought operates in.
Congress Gets Busy
We saw Congressional science committees active with oversight as well as moving legislation.
NIH Modernization
The Senate HELP Committee held a full committee hearing titled “Modernizing the National Institutes of Health: Faster Discoveries, More Cures.” NIH Director Dr. Jay Bhattacharya testified amid broader institutional transition, including the prospects of delinking NIH research facility support from research projects in an effort to change up the geographic and institutional concentration of NIH funding.
At the same time:
- NIH lost another institute director. Of 27 institutes and centers at NIH, 16 are missing a director.
- Bhattacharya may be tapped to lead CDC.
Research Security Pressure
The House Science, Space and Technology (SST) Committee has been active:
- Leaders requested answers from DOE, EPA, NASA, NOAA, and NSF about foreign-backed “paper mills.”
- The Select Committee on China sent letters to NASA and the FBI regarding CCP-linked research collaboration.
- Science Democrats raised concerns about potential NIST policy changes affecting foreign researchers.
Research security and foreign research collaboration remain central congressional pressure points and continue to see legislative activity.
AI Policy Highlights
- A GAO review of federal and state AI regulations was requested by House SST Committee leadership.
- The House SST Investigations and Oversight Subcommittee held a hearing: “Powering America’s AI Future: Assessing Policy Options to Increase Data Center Infrastructure.”
Bipartisan Bright Spots for Science Bills
Three bipartisan House SST Committee bills passed the House under suspension:
- ACERO Act (H.R. 390) – Directs NASA to improve aerial wildfire response using advanced aircraft and real-time data.
- Small Business Artificial Intelligence Advancement Act (H.R. 3679) – Directs NIST to develop AI resources for small businesses.
- ASCEND Act (H.R. 2600) – Establishes a commercial satellite data acquisition program within NASA’s Science Mission Directorate.
These are pragmatic, application-driven bills that harness science and evidence-based policy to address difficult challenges. We love to celebrate bipartisan collaboration on science over here at FAS.
Exec Branch Watch
Tariffs!
President Trump’s new 10% global tariffs are kicking in as the Supreme Court’s ruling invalidates his most sweeping duties. The president threatened to raise the levy to 15% on certain countries “where appropriate.”
EPA and the GHG Endangerment Finding
The Environmental Protection Agency announced what it described as the largest deregulatory action in U.S. history, eliminating the 2009 Greenhouse Gas Endangerment Finding. Legal challenges are already on the way. FAS happened to launch the Center for Regulatory Ingenuity (the same day) which aims to address systemic regulatory challenges such as this.
NSF Workforce RFI
The National Science Foundation issued an RFI: “Investing in U.S. Workforce Training and Innovation to Advance the President’s Trade Agreements and Ensure America’s Energy Dominance.”
NSF: Quantum and Agriculture
NSF launched a $100M National Quantum and Nanotechnology Research Infrastructure program. It also announced first awards under AI-ENGAGE, modernizing agriculture via AI systems.
OPM Civil Service Rule
The Office of Personnel Management finalized a rule creating Schedule Policy/Career, a new category for certain career federal positions they deem as “policy-influencing.” Read the FAS analysis.
Space, Satellites, and AI Infrastructure
The Federal Communications Commission accepted for filing SpaceX’s application for orbital data centers. There remain concerns in the astronomy community over satellite proliferation impacts.
Ta Ta for Now
“Structural reform” is the theme reverberating throughout Congress, the White House and the S&T ecosystem right now. The relationship between the executive branch and Congress is being tested in unprecedented ways as we all witness the “impoundment” fight play out in real time. Federal agencies are ramping up activities that are questioning longheld assumptions of how science is conducted in America. Science policymakers are thinking big about the future of science and opportunities for good-faith reforms.
If it’s all successful and carefully thought out, then it could be a welcomed and overdue evolution that stands to benefit the public significantly. However, it’s easy to be skeptical. And if it is indeed successful, will the systems we’re building be durable enough to survive the next political turn?
Onward.
Everything You Need to Know (and Ask!) About OPM’s New Schedule Policy/Career Role: Oversight Resource for OPM’s Schedule Policy/Career Rule
In February 2026, the Office of Personnel Management finalized a rule creating Schedule Policy/Career, a new category for certain career federal positions they deem as “policy-influencing.”
When the rule was initially proposed, FAS raised concerns that removing civil servant employment protections could place unnecessary and undesirable political pressure on highly specialized scientific and technical career professionals serving in government. While we appreciate the Administration’s revisions (such as those that clarify competitive service status), important questions remain about how the rule will be implemented in practice, and how it may affect agency operations, workforce motivation, and mission delivery. This is a complex change to a long-standing system, with significant implications for thousands of current and future public servants – with great potential for unintended consequences. Congress has both a responsibility and opportunity to understand the rule’s intent, implementation, and impacts as it works constructively to shape a better federal workforce system that meets the needs of the country.
This resource is designed to help Congressional members and staff (and other oversight bodies) with cross-cutting and agency oversight roles understand what implementation could look like, where discretion lives in implementation, what changes or risks may emerge over time, and what questions may be most useful to ask in oversight activities such as hearings, briefings, letters, commissioned reports, and GAO audits. Potential areas to watch and requests are aimed at specific implementation periods, as part ongoing engagement with individual agencies, or as part of more holistic review, with the goal of supporting practical, evidence-based oversight as agencies put the rule into effect.
Background
Under the rule, Schedule P/C positions remain career, merit-based roles, but employees in Schedule P/C roles:
- Move from the competitive service to the excepted service, with no appeal for such transfers
- Lose Chapter 43 (performance) and Chapter 75 (adverse action) due process protections under Title 5
- No longer have MSPB appeal rights
- Become effectively at-will for purposes of removal
- Retain protections from prohibited personnel practices (PPP) enforced internally instead of the U.S. Office of Special Counsel (OSC)
Importantly, career staff who had competitive status can transfer to a non-Schedule P/C role and regain competitive service protections. Staff who are hired into Schedule P/C roles under the merit system can likewise gain competitive status after 2 years and acquire competitive service protections if they move out of Schedule P/C.
This rule gives agencies significantly more authority over certain career policy roles. Whether that authority improves accountability or creates new risks depends almost entirely on how agencies interrupt and apply it.
If you’re interested in….
What the rule actually changes (and what it doesn’t)
Understand
- Schedule P/C are not political appointees. Under the new regulation, schedule P/C roles are policy influencing roles hired through merit processes and who retain their roles across administrations, vs. political appointments, which are selected through the White House and whose tenure ends when a president leaves office.
- The rule primarily changes protections and removal authority for staff moved to Schedule P/C, not hiring – though overseers should stay aware of hiring practices for these roles.
- Schedule P/C roles remain career, merit-filled positions and P/C employees have or can attain competitive service status (but this is worth continued engagement on)
- However, while in P/C roles, employees lose Ch. 43/75 process due process protections and MSPB appeal rights.
Ask agencies (now)
- How are you explaining this change to managers and staff?
- By what criteria will you decide what agency positions are determined to be “policy influencing” for approval by OPM?
- What written guidance have supervisors received?
Watch
- Confusion in agencies about what this is
- Implementers with different interpretations on breadth of the definitions
- Differential discussion of or treatment of Schedule P/C roles beyond this rulemaking
Why it matters: Early confusion or inconsistency may lead to uneven or overbroad designation of roles, uneven treatment across agencies, or morale challenges due to confusion about goals.
What is policy influencing (and what isn’t)
Understand: Agencies are supposed to identify roles based on whether the duties of the position meet the statutory test for being policy influencing – the role, not the person. Agencies are told to consider: roles that:
- Shape, write, or interpret regulations or policy
- Advise senior leaders on policy choices
- Translate presidential or agency priorities into action
- Direct the work of people doing the above
- Sit in policy offices, regulatory offices, or leadership advisory roles
- Have authority to influence how laws and directives are carried out
Agencies should not be considering:
- Performance
- Seniority
- Political beliefs
- Individual behavior
Ask (after agencies have made determinations):
- What criteria did you use to determine a role was policy-influencing?
- Did you conduct a role-by-role analysis? Are there instances where you designated whole offices?
- Which occupational series and functions were included? Were scientists, attorneys, grants officials, or program managers included?
- How did you treat supervisory roles?
- What written justification exists for each position?
Watch:
- Expansion or changing of definitions over time beyond the initial intent
- Use of office-wide or team-wide designations rather than position-specific analysis
- Application of the definition to roles that are primarily technical, scientific, legal, or delivery-oriented rather than policy-shaping
- Variation in interpretation across components or agencies
Why it matters: Good oversight here is about definitions and consistency.
How positions get put on the schedule
Understand: Agencies identify the roles, OPM vets the justification, and the President makes the final decision to place the positions into Schedule Policy/Career.
Ask (after agencies have made designations)
- What process did agencies use to identify positions? Are all such positions designated Schedule P/C?
- Who approved each designation at agencies?
- What documentation supports each decision at agencies?
- How are employees and job applicants notified about placement into Schedule P/C?
- How is OPM ensuring consistency between agencies?
- Given the volume of positions reviewed, what process exists to revisit or correct designations if needed?
Ask (on a rolling basis, or in a GAO review 1 year after implementation)
- How many positions were added after the initial designation?
- What justifications were used later, and did they change in scope?
- Whether the definition of “policy-influencing” is changing?
Watch
- Whether processes remain consistent and well-documented over time
- Patterns of employee questions or concerns about how decisions were made
Why it matters: Much of the practical discretion in this rule rests in how agencies conduct and document this step. Understanding this process is key to meaningful oversight.
What the loss of Chapter 43 & 75 protections really means
Understand: This removes performance improvement periods (PIPs), MSPB appeal rights, and statutory due process (notice and response) removal processes.
Ask
- How will agencies set standards for managers to meet before removing someone on Schedule P/C?
- What internal review happens before a removal decision is finalized?
Watch
- How frequently this authority is used across agencies
- Whether managers express uncertainty about when or how to use this authority
- Differences in how agencies apply this authority
- Situations where employees raise concerns related to PPP protections
Why it matters: The health of the civil service depends on disciplined, fair, and consistent implementation of workforce policies.
What replaces MSPB and OSC review and whistleblower safeguards
Understand: Schedule P/C employees cannot appeal placement or removal through MSPB or file complaints with the OSC. Instead, the rule requires agencies to create and enforce internal protections against Prohibited Personnel Practices (PPPs), including whistleblower reprisal.
Ask (when agencies have made designations)
- What PPP/whistleblower safeguards have you established for Schedule P/C?
- Who reviews allegations of misuse?
- Are these procedures public to employees?
- If an employee is separated, will they have access to these procedures?
- Will job applicants have access to these procedures?
- How are complaints tracked and reported?
- Will the confidentiality of whistleblowers be protected?
- What training have managers received on PPP risks when using Schedule P/C authority?
- What role do IG and OSC play?
- Are Schedule P/C related PPP complaints being flagged as a category?
Watch
- Whether employees understand where and how to raise concerns
- Whether safeguards are formalized in written procedures
- Whether managers demonstrate understanding of PPP responsibilities
- Patterns in complaint data that may indicate either effective safeguards or lack of awareness
- How seriously agencies operationalize these safeguards in practice
Why it matters: Under the traditional civil service system, MSPB provided an independent judge, formal record, public decisions, visible check on agency action. OSC safeguarded the merit system by protecting federal employees and applicants from prohibited personnel practices and provided a secure channel for federal employees to blow the whistle by disclosing wrongdoing. Under Schedule P/C, legitimacy depends on whether agencies build credible, transparent, and trusted internal safeguards. Visible safeguards are essential for preventing misuse of at-will authority; protecting whistleblowers and dissenters acting in good faith; maintaining workforce trust in policy offices; ensuring accountability does not become perceived politicization. Agencies need to have strong systems before problems arise.
Hiring and merit rules
Understand: Hiring for Schedule P/C roles must still follow merit procedures. New hires in Schedule P/C can gain competitive status in 2 years.
Ask (on a rolling basis)
- Are there any differences between traditional merit hiring and Schedule P/C hiring practices?
- As the rule is implemented, how many new hires have been made into these roles?
- Have any individuals previously serving in political roles been hired into Schedule P/C roles?
Watch
- Whether employees and managers clearly understand how competitive status is gained
- Public hiring announcements and transparency around these roles
Why it matters: Perceptions of politicization may arise here.
Workforce and mission impacts
Understand: These roles will sit in a wide range of functions across agencies. Early concerns about Schedule P/C highlighted risks to sensitive, scientific, technical, or high-demand roles where continuity and ability to “speak truth to power” are valued.
Ask (on a rolling basis)
- Have you seen retention or recruitment impacts in Schedule P/C roles?
- Have employees moved to Schedule P/C declined roles or departed Federal service?
- What Schedule P/C roles are in the national security, scientific, or health fields, or fields engaged in long-term risk work?
- How are agencies addressing concerns that Schedule P/C would stifle dissent or evidence-based policymaking?
- How many employees in Schedule PC roles have transferred or competed for non-Schedule PC roles? How many have sought to?
Watch
- Hollowing out of key policy offices
- Reluctance of experienced staff to serve
Why it matters: Accountability gains should not come at the expense of mission capacity.
Does this address the performance problem it’s meant to solve?
Understand: OPM justifies the rule using MSPB and FEVS data showing managers struggle to remove poor performers; however, the rule does not introduce a more mature performance management standard.
Ask (on a rolling basis, or through GAO review)
- What evidence do you have that those in “policy influencing” roles have performance issues, or that the impact of such performance issues is greater?
- Have you used this authority to remove employees for performance issues? Why could they not be addressed under prior mechanisms?
- Are managers finding it easier to address poor performance? What about to incent strong performance?
- What indicators are you watching for improved overall performance?
- What standards are being applied for performance? Are they consistent within or across agencies?
Watch
- Rule exists on paper but behavior doesn’t change
- Different definitions for poor performance arise from adverse action, conduct and performance as defined in Chapters 43 and 75
- Performance problems persist for other reasons
Why it matters: Congress should know if the remedy matches the diagnosis.
Data Congress should request via GAO for ongoing tracking and comparison
Request from agencies:
- List of all positions designated
- Written justifications
- Counts by grade, office, and occupational series
- Number of removals using this authority
- Number of PPP/whistleblower complaints related to it
- Number of hires into Schedule P/C roles
Why it matters: Early transparency prevents speculation and enables evidence-based oversight.
Biosecurity Modernization and Innovation Act of 2026 is a Major Step for U.S. Biosecurity
There are moments where biosecurity reform moves from thought to action. This week is one of them.
On Wednesday, Senators Tom Cotton (R-AK) and Amy Klobuchar (D-MN) introduced the Biosecurity Modernization and Innovation Act of 2026. Inspired in part by the National Security Commission on Emerging Biotechnology’s recommendation for foundational biosecurity and biosafety oversight reform, this bipartisan effort works to fix a basic problem: the United States still lacks clear, accountable oversight for biological risks.
This bill takes a first practical step. It gives the White House 90 days to assess the state of biosecurity oversight by clarifying roles, measuring effectiveness, listening to practitioners, and identifying gaps in resources and capability. Asking these basic accountability questions is essential to the growth of a strong and secure biotechnology landscape.
This assessment would feed directly into implementation, with executive actions where possible, legislative action where necessary, and structural reforms that could consolidate oversight mechanisms into a central oversight hub on biorisk matters.
Clarity is not just bureaucratic housekeeping. It is the critical foundation for national security, international competitiveness, and public trust in biotechnology. We have known for decades that the system needs modernization. This bill finally begins some of this critical work.
Ninety (90) days is ambitious for running an interagency process at this scale, but the urgency is needed.
For half a century, we’ve patched problems as they arose, building a culture of compliance, not curiosity. As an example, after the early-2000s anthrax attacks and a series of controversial experiments, the government created and tightened rules around select agents and created policies for “dual use” and pandemic research. Yet those policies were rarely evaluated or consistently implemented, and in some cases the measures would not have prevented the very incidents that prompted their creation. While part of the gap is technical, much of it comes from a paradigm that positions biosecurity and biosafety as a hindrance to innovation, and not its enabler.
This misalignment matters. The pace of advance in the last 50 years is dwarfed by the leaps in the last five. Biotechnology today is more diffuse and comes at a lower price point than at any point in history. It is digital, global, and increasingly powered by AI. Tools that once required specialized labs may now run from a laptop or are outsourced across borders.
This is the moment to move from fragmented compliance to modern governance: a system that is proactive, coordinated, and accountable. Senators Tom Cotton and Amy Klobuchar recognize that reality. Their bill creates the space to step back, clarify roles, and design biosecurity oversight on purpose – not by accident or after the next crisis.
By preparing credible, bipartisan options now, before the bill becomes law, we can give the Administration a plan that is ready to implement rather than another study that gathers dust.
At the Federation of American Scientists, this reform agenda builds on work already underway across the biotechnology landscape – from exploring and advancing practical governance approaches for AI-enabled and data-driven biology, strengthening domestic biomanufacturing and scale-up policy, identifying gaps and coordination challenges in federal oversight, and translating technical expertise into actionable options for policymakers.
FAS is expanding its role as a convener and catalyst over the coming months through additional gatherings, publications, and structured dialogues with government, industry, academia, and civil society leaders to help shape the present and future of biorisk policy.
This next phase will focus on foundational, cross-cutting reform. Many of the ideas on the table today are incremental; they target individual risks or technologies in isolation. However, the challenges we face are systemic. We need institutions and oversight tools that evolve alongside the science, and align innovation, economic growth, and security rather than treating them as tradeoffs. That’s the focus of our work. If you would like to engage, please reach out to any of us via email or on LinkedIn. We are actively working with practitioners, policymakers, and researchers to surface practical insights, align incentives, and ensure that oversight frameworks are both grounded in real-world practice and widely supported.
The Aftermath: The Expiration of New START and What It Means For Us All
The last remaining agreement limiting U.S. and Russian nuclear weapons has now expired. For the first time since 1972, there is no treaty-bound cap on strategic nuclear weapons.
On February 5th, Axios reported that following overnight negotiations between the two sides, there remains a possibility for the two countries to continue observing the central limits after the Treaty’s expiry, although it did not state whether such an arrangement would include verification, and also noted that it had not been agreed to by either President.
If the two sides cannot reach an agreement, we face a world of heightened nuclear competition fueled by worst-case planning and nuclear expansion, fewer transparency mechanisms, and deepening mistrust among nations with the world’s most powerful weapons. Addressing these challenges in the new nuclear era will require creative and nontraditional approaches to risk reduction and arms control.
How did we get here?
Even if the two sides manage to negotiate a last-minute band-aid arrangement, the fact that we have no long-term arms control solution ready to take New START’s place is the culmination of years of breakdown in diplomacy and arms control efforts. New START entered into force on February 5th, 2011, with a 10-year duration and the option to extend it for five additional years. Leading up to the treaty’s original expiration date in 2021, there was serious concern that the United States and Russia would not come to an agreement on extension. For the first three years of his first administration, President Donald Trump engaged in few constructive arms control discussions with Russia. Then, in the final months of 2020, he proposed a short-term extension contingent on Russia agreeing to new verification measures and a warhead freeze, which Russia rejected. At the 11th hour, just two weeks after his inauguration, President Joe Biden agreed to a full five-year extension of the treaty with Russian President Vladimir Putin.
The shaky status of New START further deteriorated in early 2023 when Putin announced that Russia was “suspending” its participation in the treaty, stipulating that resumption would require the United States to end its support for Ukraine, and that arms control talks would also have to involve France and the United Kingdom. As part of its suspension, Russia halted its exchanges of data, notifications, and telemetry information, and the United States subsequently followed suit with reciprocal countermeasures.
It is important to note that although the United States found Russia’s actions to constitute noncompliance with the treaty’s requirements, successive State Department reports following Russia’s suspension assessed that “Russia did not engage in any large-scale activity above the Treaty limits.” The 2024 compliance report, however, stated that “Russia was probably close to the deployed warhead limit during much of the year and may have exceeded the deployed warhead limit by a small number during portions of 2024.”
Ultimately, over years of growing tensions and mistrust between the two countries, the United States and Russia have barely managed to see New START through to its expiration, much less engage in talks for a new treaty to take its place. In September 2025, the Kremlin stated that “Russia is prepared to continue observing the treaty’s central quantitative restrictions for one year after February 5, 2026,” without verification. President Trump told a reporter that the proposal “sounds like a good idea to me,” but apparently did not respond to the proposal before the treaty’s deadline expired.
In addition to the worsening U.S.-Russia relationship, funding cuts at the U.S. Department of State, the Defense Nuclear Nonproliferation office at the NNSA, and the Office of the Director of National Intelligence mean less investment in and capacity for executing a follow-on agreement, even if the political environment allowed for it.
What could this mean for nuclear forces?
New START placed limits on the number of strategic nuclear weapons that each country could possess and deploy: each side could deploy up to 1,550 warheads and 700 launchers, and could possess up to 800 deployed and non-deployed launchers. Incorporating a limit on non-deployed launchers was intended to prevent either country from “breaking out” or quickly expanding deployed numbers beyond the treaty limits.
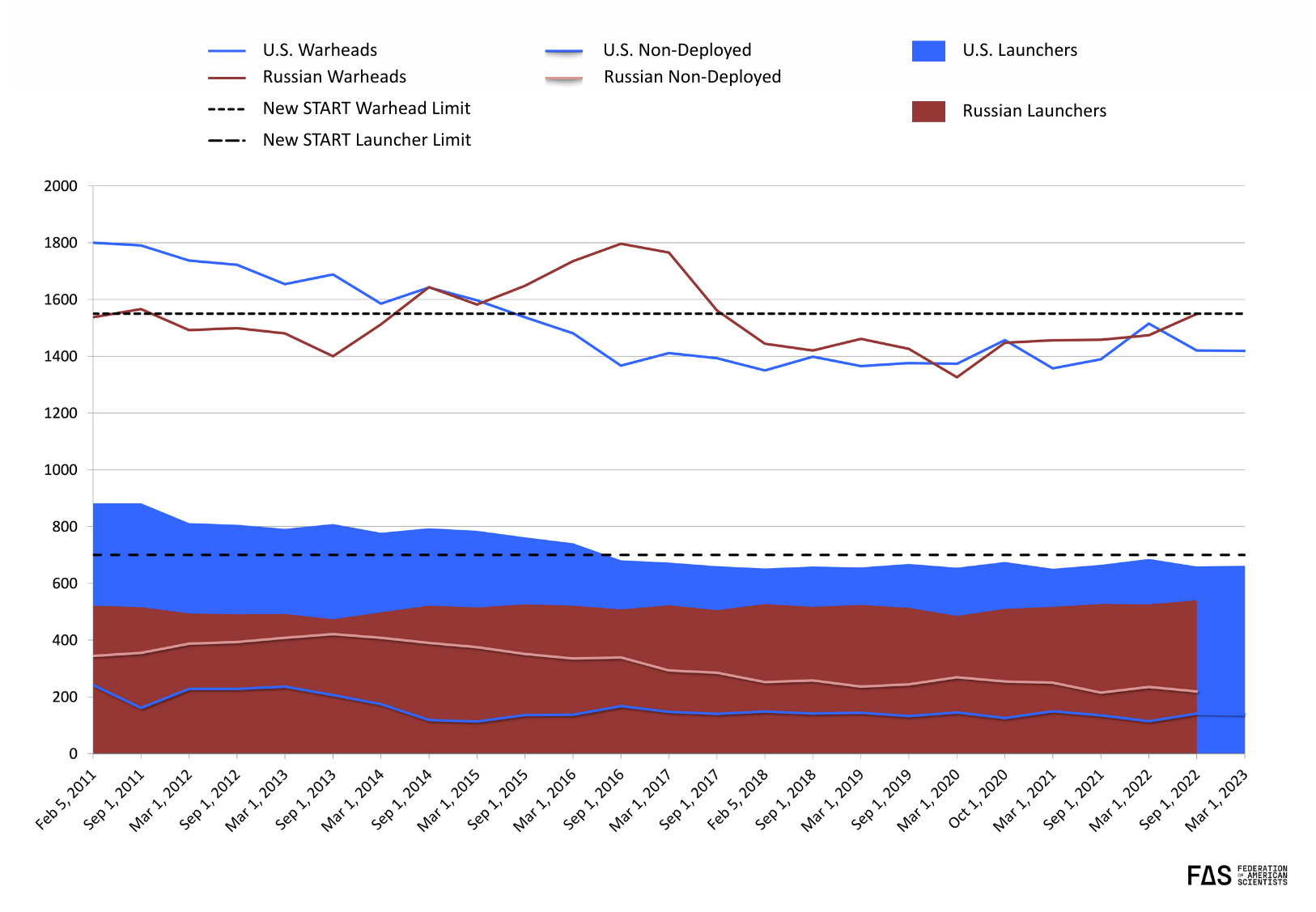
Over the past 15 years, the treaty restraints and respective modernization plans resulted in significant force reductions in Russia and the United States. Both countries have meticulously planned their respective nuclear modernization programs based on the assumption that neither will exceed the force levels currently dictated by New START. In the absence of an official agreement following New START’s expiration, however, both countries will likely default to mutual distrust and worst-case thinking about how their arsenals will grow in the future. This is a serious concern, considering both countries possess significant warhead upload capacity that would allow them to increase their deployed nuclear forces relatively quickly.
This kind of thinking has already been displayed by members of the House Armed Services Committee who, in 2023, called Biden’s agreement to extend New START “naive” and argued that Russia “cannot be trusted,” saying “if these agreements cannot be enforced, then they do nothing to enhance U.S. security, and serve only to undermine it.” Defense hawks in Congress and outside argued instead for upgrades and expansions to the U.S. nuclear force; the bipartisan Congressional Commission on the U.S. Strategic Posture in late-2023 recommended a broad range of options to expand the U.S. nuclear arsenal. The Biden administration also appeared to lay the groundwork for potential options to expand its deployed nuclear force following the end of New START: in June 2024, Pranay Vaddi, Special Assistant to the President and Senior Director for Arms Control, Disarmament, and Nonproliferation at the National Security Council, stated that “Absent a change in the trajectory of adversary arsenals, we may reach a point in the coming years where an increase from current deployed numbers is required. And we need to be fully prepared to execute if the President makes that decision—if he makes that decision.” The Biden administration’s Nuclear Employment Strategy published in 2024, however, did not direct an increase of U.S. deployed nuclear forces, effectively leaving that decision to the Trump administration.
If the United States decided to increase its deployed strategic forces, there are measures it could take to rapidly upload reserve warheads, while other options will take more time. For example, all 400 deployed U.S. ICBMs currently only carry a single warhead, but about half of them use the Mk21A reentry vehicle that could be uploaded to carry three warheads each if necessary. An additional 50 “warm” ICBM silos could also be reloaded with missiles, though this process would likely take several years. With these potential additions in mind, the U.S. ICBM force could possibly double from 400 warheads to up to a maximum of 800 warheads. In any case, executing such an upload across the entirety of the ICBM force would require significant resources, manpower, and time—none of which the United States has in excess, given existing constraints on its already-delayed nuclear modernization program.
Increasing the warhead loading on U.S. ballistic missile submarines could be done faster than uploading the ICBM force. Each missile on the submarines currently carries an average of four or five warheads, a number that can be increased to eight. Doing so could theoretically add 800 to 900 warheads to the submarine force, but loading each missiles with the maximum number of warheads onto each missile (and by extension, each submarine) would dramatically limit the submarine force’s targeting flexibility, as war planners will not want to lock themselves into a situation in which submarine crews would be forced to fire the maximum number of warheads, rather than having a range of more limited options at their disposal. As a result, executing an upload across the submarine force could more realistically result in an increase of approximately 400 to 500 additional warheads. Doing so would take many months, given that each ballistic missile submarine would have to return to port on a rotating schedule in order to load the additional warheads. In addition, the United States has the option to reopen the four launch tubes on each ballistic missile submarine that had been converted to non-nuclear status for New START compliance, and the July 2025 “One Big Beautiful Bill Act” provided $62 million for conversion activities to take place after March 1st, 2026; however, doing so would need to overcome significant internal opposition and would likely take several months, if not years, to complete.
The quickest way for the United States to increase deployed nuclear warheads would be to load nuclear cruise missiles and bombs onto its long-range B-2 and B-52 bombers. The bombers were taken off alert and their nuclear weapons placed in storage in 1992, but hundreds of the weapons are stored at the bomber bases and could be loaded within days or weeks; additional weapons could be brought in from central storage depots. Up to 800 nuclear weapons are estimated to be available for the bombers. Yet loading live nuclear weapons onto bombers would significantly increase the vulnerability of the weapons to accidents and terrorist attacks.
Russia also has a significant warhead upload capacity, particularly for its ICBMs, but is subject to similar constraints as the United States. Several of Russia’s existing ICBMs are thought to have been downloaded to a smaller number of warheads than their maximum capacities in order to meet the New START force limits. As a result, without the limits imposed by New START, Russia’s ICBM force could potentially increase by approximately 400 warheads.
Warheads on missiles onboard some of Russia’s SSBNs are also thought to have been reduced to a lower number to meet New START limits. Without treaty limitations, the number of deployed warheads could potentially be increased by 200-300 warheads, perhaps more in the future, although this number could be tempered by a desire for increased targeting flexibility, in a similar manner to the United States.
While also uncertain, Russian bombers could be loaded relatively quickly with hundreds of nuclear weapons, similarly to the United States.
Ultimately, if both countries chose to upload their delivery systems to accommodate the maximum number of possible warheads, both sets of arsenals could nearly double in size. While a maximum upload is highly unlikely, it is possible we will see immediate measures taken to upload certain systems, followed by gradual increases in other areas over the next few years. While defense hawks in Russia and the United States claim that more nuclear weapons are needed for national security, doing so would inevitably result in each country being targeted by hundreds of additional nuclear weapons.
Moreover, without the transparency and predictability that resulted from the verification regime and regular data exchanges stipulated under New START, nuclear uncertainty—and potentially confusion and misunderstandings—will increase. Russian and U.S. planners will rely more on worst-case scenarios in their nuclear programs, and both countries are likely to invest more in what they perceive will demonstrate resolve and increase their overall security, including nonstrategic nuclear forces, conventional forces, cyber and AI capabilities, and missile defense. These moves could also trigger reactions in other nuclear-armed states, possibly leading to an increase in their nuclear forces and the role they play in their military strategies. China has already decided to increase its nuclear arsenal to better be able to counter what it perceives is a growing threat from other military powers; Beijing rejects numerical limits on its nuclear arsenal and increasing U.S. and Russian nuclear arsenal will make it harder to change its mind.
Re-imagining the future: The end of fully “compartmentalized” arms control?
The future of arms control is certainly not dead, but it is likely entering a new era. For decades, the United States and Russia pursued arms control negotiations in isolation from other security issues, emphasizing that the unique destructiveness of nuclear weapons requires that the topic be segregated. Although such negotiations were never completely disentangled from politics or other geopolitical events—as demonstrated, for example, by the refusal of the U.S. Senate to ratify SALT II after the Soviet invasion of Afghanistan—this approach was largely successful as a framework for arms control during and immediately after the Cold War.
This fully compartmentalized approach, however, is likely no longer an option in a post-New START world. Russia has made it clear through both its actions—particularly its suspension of its treaty obligations primarily due to U.S. support for Ukraine—and its rhetoric that it will no longer engage in arms control negotiations absent a broader reboot of U.S.-Russia relations. And officials in the United States increasingly argue that bilateral nuclear limits on U.S. and Russian nuclear arsenals do not take into account the growing Chinese nuclear arsenal.
On February 3rd, Deputy Foreign Minister Ryabkov stated that in order to engage in strategic stability dialogue, “We need far-reaching shifts, changes for the better in the US approach to relations with us as a whole.” On numerous prior occasions, he had critiqued the United States’ approach to arms control: in 2023, he told TASS that Moscow cannot “discuss arms control issues in the mode of so-called compartmentalization, which means singling out from the whole range of issues some pressing ones which are of interest to the United States, and pushing to oblivion or taking off the table other points that are theoretically as important to Russia as those of interest to the Americans.”
It would appear that China thinks about arms control in a similar way. In 2024, China suspended strategic stability talks with the United States in response to U.S. arms sales to Taiwan and increased trade restrictions on China. A spokesperson from China’s Ministry of Foreign Affairs emphasized that in order to bring China to the table, the United States “must respect China’s core interests and create [the] necessary conditions for dialogue and exchange.” On February 5th, Chinese Foreign Ministry spokesperson Lin Jian reiterated that “China’s nuclear strength is by no means at the same level with that of the U.S. or Russia. Thus, China will not take part in nuclear disarmament negotiations for the time-being.” Even if it were possible to change China’s opposition to numerical limits on nuclear forces and join the arms control process, it is not clear what the United States would actually be willing to limit or give up in return for Chinese concessions. One such possibility would be the more ambitious and fantastical elements of Golden Dome, as a multi-layered, space-based missile shield is fundamentally incompatible with the idea of accepted mutual vulnerability.
Re-imagining the future: verification without on-site inspections?
Traditional nuclear arms control, including New START, relies on the availability of on-site inspections to verify compliance. Absent a significant shift in geopolitical relations, however, it is implausible to imagine some combination of American, Russian, or Chinese inspectors roaming around each other’s territories anytime in the near future. As a result, the next generation of arms control agreements faces a clear challenge: how can countries verify that the other remains in compliance when the political reality prohibits on-site inspections?
Traditionally, countries have used “National Technical Means”—a term used to describe classified means of data collection, such as remote sensing and telemetry intelligence—to verify compliance with arms control agreements. NTMs are used as a complement to other sources of verification, including on-site inspections, data exchanges and notifications, and the exchange of telemetric information. Despite on-site inspections and formal data exchange being preferable, NTMs can be very capable; for example, the U.S. assessment that Russia might briefly have exceeded the New START warhead limit was based on NTMs, not on-site verification.
Given the political implausibility of on-site inspections forming part of a future verification regime, one of the authors has recently co-authored a report with Igor Morić from Princeton’s Science & Global Security Program on the possibility of a future arms control arrangement based around “Cooperative Technical Means.” Under such an arrangement, it could be possible for states to use national or commercial remote sensing tools to monitor each other’s nuclear capabilities, verify the numbers of fixed and mobile ICBM and SLBM launchers, as well as track the number and location of their heavy bombers. For a more detailed explanation, the full report can be accessed here.
What Now?
As Axios’ reporting indicates, everything could change in a day, for better or for worse. Countries could take unilateral measures to either exercise restraint or refuse cooperation. Specifically, it is important that each side refrain from significant increases in its nuclear arsenal regardless of whether a new arrangement is concluded; such steps will almost inevitably increase the competition dynamic that would result in an arms race.
It is also imperative that the United States and Russia commit to engaging in arms control as a means of reducing the risk of nuclear use, whether intentional or by accident or misinterpretation. The United States, in particular, should reinvest in and reprioritize diplomacy and nonproliferation to prepare for and signal an intention to re-engage in arms control dialogues.
While new technology and creative approaches offer potential solutions to issues plaguing past arms control arrangements, progress will still require political will and motivation from both sides.
Here at FAS, we will continue to track the nuclear force status and modernization programs across the nine nuclear-armed states, paying close attention to cost and schedule overruns that relentlessly plague many of these efforts. In an era where nuclear transparency and access to reliable, public information are declining, we believe our work is more critical now than ever before.
Additional work from us on this topic:
- After Seven Years of Implementation, New START Treaty Enters Into Effect
- If Arms Control Collapses, US and Russian Strategic Nuclear Arsenals Could Double In Size
- Inspections Without Inspectors: A Path Forward for Nuclear Arms Control Verification with “Cooperative Technical Means”
- The Long View: Strategic Arms Control After the New START Treaty
- 2025 Russia Nuclear Notebook
- 2025 United States Nuclear Notebook
- For all Nuclear Notebooks, see here
The Nuclear Information Project is currently supported with generous contributions from the Carnegie Corporation of New York, the New-Land Foundation, Ploughshares, the Prospect Hill Foundation, and individual donors.
“Going Back to Cali” for AI Governance Lessons as States Take the Lead on AI Implementation
Imagine you are a state-level technology leader. Recent advancements in artificial intelligence promise to make approving small business licenses faster, or improve K-12 student learning, or even standardize compliance between agencies. All of which promise to improve the experience of your state’s constituents. Eager to deploy this new technology responsibly, you look to peers in other states for guidance. Their answers vary wildly, and in the absence of federal guidance, it quickly becomes clear that there is no standardized playbook. You must chart the path forward on your own, with far more limited resources.
This scenario is becoming increasingly common as AI systems are moving rapidly into consumer-facing services. Without federal action on AI, state government leaders are increasingly shouldering the responsibility for both protecting consumers from potential algorithmic harms and also supporting responsible innovation to improve service delivery to their constituents. States have structural advantages that position them to experiment with regulatory approaches: shorter legislative cycles that allow for quicker course corrections, authority to pilot programs, and the use of sunset provisions that make it easier to revise or retire early-stage governance models. This often places states as the most agile regulators who can swiftly set up guardrails for rapidly evolving AI technologies that impact their residents.
But this regulatory agility must be matched with the necessary government capacity in order to be a success. The current lack of federal action is forcing states not only to pass new AI laws, but also to take on huge implementation challenges, without the AI expertise typically found in federal agencies or major private employers. Building this capacity within state governments will demand resources and technical expertise that most states are only just starting to chart . Without deliberate investment in transparency and talent, even the most well-crafted legislation might not achieve their intended goals. As State legislative cycles start back up for the 2026 year, state policymakers should move forward with proposals that increase transparency, accountability, and bring new technical experts directly into government to meet the scale of need in the current moment.
Increased Transparency to Build Public Trust
One of the most immediate ways that state legislatures can move forward with transparency-improving legislation is with the passage and successful implementation of use-case inventories. A use-case inventory is a public-facing publication of algorithmic tools and their specific uses. They disclose when and where state governments are utilizing algorithmic tools in consumer-facing transactions such as applications for social programs and public assistance benefits. They are typically conducted by governments as a mechanism for transparency and to facilitate third-party auditing of outcomes.
The benefits of public-facing AI use-case inventories are far reaching: they increase government transparency into automated decision-making outcomes, can provide valuable insights to private-sector product vendors, facilitate third-party auditing and bias-testing, and can even increase interagency sharing of best practices when AI tools are effectively used. They are particularly important in high-risk decisions such as those related to government benefits and services. Alternatively, a lack of transparency in expensive acquisitions from private and third party vendors can mean that an agency or entity is unaware of what tools they have acquired and whether or not they are safe to deploy in consumer-facing settings without bias or other inaccuracies.
When increasing numbers of Americans are growing skeptical of the practical uses of AI tools, it is doubly important to design public systems that encourage transparency when algorithmic tools are deployed in the public and private sectors alike.
Despite a lack of federal legislation regulating responsible AI usage, one area where the federal government has led is in the production of regular AI use-case inventories since 2021. First requested via Executive Order 13960 in 2020 during the first Trump administration, and implemented in the Summer of 2021, the federal government provides a relatively transparent accounting of where AI is adopted within the federal enterprise. This policy has had bipartisan appeal, and the Biden administration continued the production of regularly updated inventories for the public. The Trump administration with its recently updated inventory now has the opportunity to use this tool to deliver increased public trust in AI, a clear administration priority.
Case Study: Implementation Challenges in California
While the federal experience demonstrates that AI use-case inventories can work, it also reveals an important limitation: transparency mechanisms rely on technical talent and focused implementation to be successful. California offers a cautionary example. In 2023, the state legislature passed Assembly Bill 302 requesting the State Department of Technology to “conduct a comprehensive inventory of all high-risk automated decision systems [ADS] being used by state agencies and submit a report to the Legislature by January 1, 2025, and annually thereafter.” Importantly, the bill covered systems that are “used to assist or replace human discretionary decisionmaking.” The bill was envisioned as a critical first step in gaining insight into the ways AI was being deployed in consumer-facing interactions by state government agencies. It was also in reaction to public reporting of biased technology being used on those applying for public services and benefits.
However, the initial implementation deadline for the bill passed in early 2025 and the only report provided to the public was a single document stating that there are “no high-risk ADS [tools] being used by State agencies”—a fact that is easily disputed by a simple Google search. For example, the state healthcare exchange uses automated document processing tools to gauge eligibility for affordable health insurance policies, the state unemployment insurance program uses an algorithmic tool developed by a private company to rate applicants on the likelihood of their application being fraudulent, and the state Department of Finance even plans to use generative AI tools as part of fiscal analysis and state budgeting work. These are significant decisions that can have real repercussions for California residents. Rather than creating a transparent use-case inventory that can tell Californians where AI is being used in consumer-facing interactions, we instead have a letter which incorrectly states —based on examples above—that there are no algorithmic tools being used. The table below has additional examples of publicly disclosed automated decision-making system use cases in California state government.
Results like this underscore the urgent need to embed technical talent within state governments to ensure that laws are implemented as designed. When implementing its use case inventories, the federal government provided guidance to reporting agencies and publicly released a final inventory for a majority of agencies. Even with substantial support during the federal government’s collection process, there were still notable implementation challenges faced when creating a federal use-case inventory. Most notably, many agencies initially failed to disclose all use-cases, and a promised template for agencies to use has yet to come to fruition. The State of California, by contrast, instead relied on an ad hoc process, polling state agency officials through two successive emails to conduct its inventory evaluation.
Scaling Government Talent to Bridge the Technical Capacity Gap
California’s experience implementing a use-case inventory is, unfortunately, not unique. Across the country, well-intentioned legislation is often passed into law only to falter during implementation. Once enacted, agency staff are tasked with operationalizing complex policies, often without the necessary technical expertise, staffing capacity, or financial resources to succeed. Without deliberate investment in these areas, the responsibility of properly regulating emerging technologies and protecting consumers from harm is shifted to government employees that are poorly equipped to handle the growing scope and technical complexity of their workloads. That is why, in addition to transparency, states need to find ways to quickly bring in technical talent and expertise in digital technologies to drive forward effective implementation of the coming onslaught of bills.
In the midst of massive layoffs within the federal government and private sector, individual states now have access to historic levels of human capital and can bring forward some of the innovations developed within the federal government in recent years. Methods like skills-based hiring to rapidly bring in technical talent and scale new teams within government have also been developed and thoroughly tested in recent years through entities like the United States Digital Service (USDS) and the Consumer Financial Protection Bureau’s in-house technologists. These initiatives brought skilled workers into government at less than half the recruiting cost of private sector hiring and saved hundreds of millions of dollars through reimbursable agreements with agencies in lieu of costly private sector consultancy contracts.
During periods of financial uncertainty it can be deeply challenging for state leaders to make the investments necessary to hire additional staff and build robust government teams. One other method to bridge the gap between policymakers and those who implement it is through the development of modernized policy fellowships that utilize endowments or other private funds to bring cutting-edge researchers and experts directly into government. California has most recently unveiled a revamped science and technology fellowship that will place additional AI experts within state agencies or the legislature to propel forward-thinking and informed policymaking.
Conclusion
With no federal framework in place, state governments will be the primary drivers of accountability and transparency needed to ensure AI serves the public rather than erodes democratic norms. This presents us with a crucial window for state policymakers to establish both processes that further transparency and robust talent pipelines that can manage responsible deployment in order to restore public trust and prevent harms before AI systems become further entrenched in critical public services. States that build transparent AI use-case inventories and invest in technical expertise will be best positioned to translate lofty regulatory principles into real protections for their citizens—while also fostering a fairer, more trustworthy environment for innovation to thrive.
Gil on the Hill: January 2026
2026’s Roaring Start
We’re back! So much has happened in the first month of 2026. So much. January brought a jolt of game-changing national political events and government funding brinksmanship. If Washington, D.C.’s new year resolution was for less drama in 2026, it’s failed already.
As we reflect on 2025 and head into 2026, the question now is less about whether science and technology will stay rhetorically important (we saw that it will). Rather, it’s whether policymakers are willing to go beyond the platitudinous “China competition” or “AI leadership” talking points and invest in the unglamorous infrastructure that makes scientific and technological progress possible in the first place.
Appropriations and Shutdown Watch
So, what’s happening? Did Congress fund science? Will we shut down? What does it all mean for us? Here is where things stand at the time of writing.
Status. In November, Congress ended the longest government shutdown in history by extending its deadline for a funding deal to January 30th, 2026. That date has fast arrived, and Congress has fully passed 6 of 12 appropriations bills – Agriculture, Military Construction & Veterans Affairs, Legislative Branch, Commerce, Justice, & Science, Energy & Water Development, and Interior & Environment. No one wants a shutdown, least of all the agencies that are forced into a contingency mode that disrupts operations and destabilises long-term planning.
Things Were Going Well for a Minute. After a string of successive compromises on bundles of appropriations bills (“minibuses”) and final passage into law of the minibus for Commerce, Justice, and Science, Energy and Water Development, and Interior and Environment (CJS-E&W-Int), Congress finds their momentum abruptly halted ahead of voting on the remaining 6 bills with urgent calls for more Department of Homeland Security (DHS) oversight in the wake of the killing of Minneapolis ICU nurse Alex Pretti by a U.S. border patrol agent.
75% of Fed Funding Still at Stake. Furor over the Trump Administration’s immigration crackdown which now includes the killings of American citizens and other high-controversy incidents by DHS agents, on top of brewing tensions over the conflict in Venezuela and diplomatic standoffs over Greenland, have threatened an already-strained process that still needs the final passage of the full Congress for six bills which account for more than 75 percent of federal discretionary spending.
Oof, another shutdown…? Probably. There is a serious likelihood of a partial government shutdown as the Senate takes up its next votes on remaining funding bills ahead of the Jan 30th deadline. The House did its part, and 6 funding bills remain for final passage in the Senate – Defense, Labor-Health and Human Services-Education, Transportation-Housing and Urban Development (THUD), Financial Services, Homeland Security, and National Security-State. Republicans will need Democratic votes to pass it, and so far, not enough have indicated they will support it without DHS oversight.
Dems DHS Oversight Demands. DHS Oversight Senate Minority Leader Chuck Schumer wants DHS funding legislation changed, but the other five pending appropriations bills passed in the meantime. Several Democrats who crossed over with Republicans to end the previous shutdown plan to vote against the funding bills without the inclusion of more oversight for Immigration and Customs Enforcement (ICE) and Customs and Border Protection (CBP) in the bill.
Republican Concerns. Senate Republican leadership wants to vote on the six-bill package, including DHS, with no changes, and is pushing back against calls to “defund DHS.” President Trump has entered the negotiations with a push forRepublicans to pass a bill to “END Sanctuary Cities.” Republicans are voicing concerns about DHS actions and calling for an investigation.
Earmarks at Stake. A shutdown will have state and local communities anxiously awaiting the fate of their earmarks, or congressionally directed spending that sends federal funds directly to local projects. Part of the package (agreed to, but not voted on) includes $16 billion worth of earmarks for everything from construction projects to new police equipment to wastewater infrastructure.
Bottom Line. Midnight on Saturday, January 31, may yet see us hit another government shutdown, albeit partial yet substantial.
Science in Approps
There is positive news for the science and tech community as Congress passed and President Trump signed into law a full-year appropriations package that included accounts critical to science and technology at federal agencies. It may not be everything the science community wanted, but considering the Republican-controlled Congress and White House and their pledges to massively cut spending, the modest cuts in the final bill can be received in that context as a reprieve from the worst-case scenarios. It also means that these accounts (such as the National Science Foundation, Department of Energy, etc.) will not be directly impacted by the potential government shutdown. The funding bill, including the Department of Education and its programs, however, is still at risk, as well as countless other programs that touch the scientific enterprise.
Proposed Cuts vs Final in Minibus. In the bill considered most directly important for scientific research, the CJS-E&W-Int minibus rejected the Trump Administration’s cuts for the National Science Foundation by 57%, for the Department of Energy’s (DOE) Office of Science by $1.1 billion, and for NASA’s science budget by 47%. Instead, the package sustains research funding for NSF, provides $160 million more for the DOE Office of Science (which supports critical research being conducted by 22,000 researchers at our 17 national labs and over 300 universities), and provides $7.25 billion for NASA’s science budget.
Funding Oversight. The final CJS-E&W-Int minibus included hundreds of specific policy provisions to accompany the funding that detail how the funding should be spent. This is in response to the misuse of funds by the Trump Administration that many agree amounted to illegal impoundment. We’ll have to wait and see if it has the desired effect…
Indirect Costs. The minibus includes language blocking the imposition of a 15% cap on indirect cost reimbursement at the federal science research agencies funded in the package (NSF, the National Institute of Standards & Technology, NASA, and the Department of Energy’s Office of Science). This is on top of a federal appeals court ruling blocking the NIH from moving forward with a cap on research indirect cost payments. The administration has not announced whether it intends to appeal this ruling.
NDAA and Science
Appropriations is taking up a lot of attention, but it’s not all that Congress is up to. Most importantly, Congress passed the 2026 National Defense Authorization Act (NDAA), which includes important provisions for science, R&D, and national security. Maybe more importantly, it omitted several controversial provisions, too.
Research Security. The NDAA contains some controversial new restrictions on research collaborations with China and other “countries of concern.” It also drops other research security proposals that had drawn objections from the U.S. scientific community, and blocks a unilateral reduction of overhead payments to DOD grantees. Notably, the SAFE Research Act did not pass with the NDAA, and neither did a Senate provision to prohibit any higher education institution conducting research funded by DOD from entering into contracts with a covered nation or foreign entity of concern.
AI. Renewed efforts to restrict state regulation of AI landed flat once again as they did not make it into the final NDAA. It does, however, direct the Secretary of Defense to establish one or more AI research institutes, known as National Security and Defense Artificial Intelligence Institutes, at higher education institutions that conduct DOD-sponsored research.
Indirect Costs. (again!) Similar to language in the CJS-E&W-Int minibus, the NDAA blocks the Secretary of Defense from changing or modifying the indirect cost rates for DOD grants to research institutions until the Secretary certifies that DOD has developed an alternative model in consultation with the extramural research community that reduces the rate for all institutions and allows “adequate transition time” for affected institutions to adjust.
Executive Branch Highlights
Genesis Mission. A recent executive order from the White House establishes a “Genesis Mission” that aims to “mobilize the Department of Energy’s 17 National Laboratories, industry, and academia to build an integrated discovery platform.” According to the DOE press release, the platform will draw on the expertise of roughly 40,000 DOE scientists, engineers, technical staff, and private sector innovators.
NSF Tech Labs. We are thrilled about NSF’s launch of a new “Tech Labs” program that represents a new federal science funding paradigm: team-based, outcome-driven, independent labs, each targeted to receive between $10M and $50M a year. Overall, NSF expects to put up to $1B into this new program.
FAS is particularly excited about this, as it played a central role in introducing this concept in 2020 in the form of a proposal for Focused Research Organizations. Several FAS teammates have spent years evangelizing the concept across research agencies and Congress. Check out what FAS is saying about it:
- Team Science needs Teamwork: Universities should get in on the ground floor in shaping the vision for new NSF Tech Labs (from Erica Goldman)
- NSF Plans to Supercharge FRO-style Independent Labs. We Spoke with the Scientists Who First Proposed the Idea. (from Daniel Correa)
Higher Ed Watch
Universities and higher ed continue to deal with the dynamic state of politics and federal policies, yet a new R&D survey reminds us how valuable they remain to the nation’s research enterprise – $117 billion worth.
Education and Approps. The House passed the Labor-HHS-Education package by a margin of 341-88. Now we await Senate passage of theeducation funding bill that would allot $79 billion in discretionary funding. The legislation would flat-fund the Pell Grant, Federal Supplemental Educational Opportunity Grant (FSEOG), Federal Work-Study (FWS), the federal TRIO, and Gaining Early Awareness and Readiness for Undergraduate Programs (GEAR UP) programs at FY 2025 levels. The legislation also included a provision that would block funding for ED from being transferred to other agencies, unless specified in the appropriations law.
Higher education R&D expenditures reach $117 billion in FY 2024. The smart folks at SSTI have taken an informative look at Higher Ed R&D expenditures.
Higher Education R&D expenditures jumped 8%, or nearly $9 billion, from fiscal year (FY) 2023 to 2024, reaching an all-time high of over $117 billion, according to new Higher Education R&D (HERD) survey data. The funding sources of HERD expenditures remain proportionally unchanged from the prior year, with all sources increasing, and the federal government ($5 billion) and institution funds ($2.5 billion) accounting for the largest dollar increases.
Adjusted for inflation, overall HERD expenditures increased by 5%—the second largest year-over-year increase in the past decade—while all sources of funds except business increased.
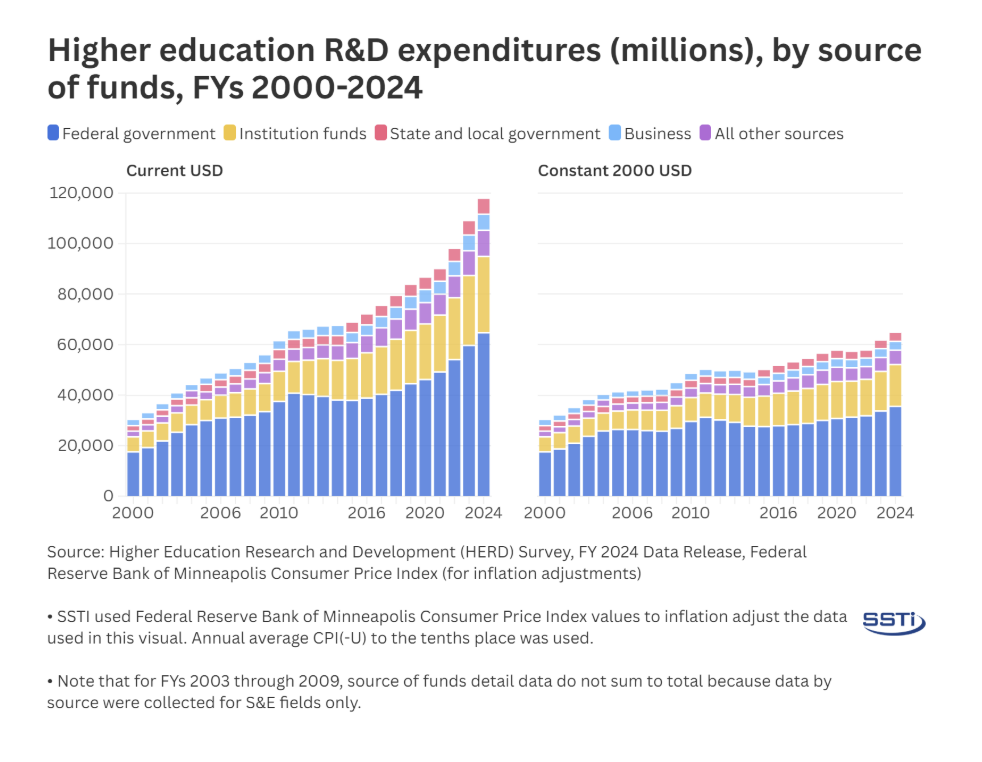
source: Higher Education Research and Development (HERD)
Ta Ta for Now!
2026 will be another landmark year for how we make an affirmative, public-interest case for science amidst turbulent political times. We’re looking forward to making that case together with you.
Right now, the premium is less on splashy tech announcements and more on signals of institutional commitment like stable funding, durable governance, and a willingness to invest in systems that do not produce immediate political wins.
Reach out for any shutdown questions or requests for topics next month! It’s going to be a fun year.
Introducing Digital Service Retros: Back to the (Digital) Future
On January 20, 2025, the U.S. Digital Service, 18F, and much of the Technology Transformation Service were disbanded or fundamentally reshaped. The institutions that once rebooted HealthCare.gov, expanded access to care for millions of Veterans, and launched Direct File were transformed overnight, marking a dramatic shift in how the federal government delivers critical services to the American people.
In parallel—governments at the state and local levels have made landmark investments in digital teams and innovation, which has already generated real results and cost savings.
This is not the first disruption in public-sector digital capacity. But the scale of this moment, colliding with rapid advances in AI, new procurement models, and evolving expectations of government, creates a rare opportunity. It is a moment to look back in order to build for the future. To pause, together, as a community, and ask what we’ve learned—and what comes next.
The Federation of American Scientists, in partnership with Georgetown University’s Beeck Center for Social Impact + Innovation and the Better Government Lab at Georgetown University and the University of Michigan, is launching a national series of digital service retrospectives. These convenings will capture hard-won lessons, surface what truly worked, be clear-eyed about what didn’t, and bring digital service experts together to imagine next-generation models for digital government.
How might we redesign digital service capacity—its operating models, authorities, and talent—based on over a decade of progress in civic technology? What drew you to this work? What accelerated impact, and what slowed it down? What was missing? What was overbuilt? What made partnerships and deployments succeed—or fail?
We are inviting participation from across the U.S. digital government ecosystem: current staff and alumni of USDS, 18F, and TTS, digital teams across federal agencies, states, and cities, and the lawyers, procurement and talent specialists, data leaders, congressional staff, and policy experts who worked alongside them. There are lessons here that must be captured and shared.
Through a series of virtual and in-person workshops, participants will share experiences, ideas, and aspirations. At each session, we will synthesize what we hear, ultimately building toward a public set of insights and recommendations for the future of digital capacity in government. From there, we will take these recommendations to policy makers on the Hill to inform future legislation, executive branch champions, as well as to state and local leaders across the country to see which ideas and concepts they can start piloting now. This is policy entrepreneurship—building innovative ideas and bring them to life with key partners and talent—is what FAS does well and, with Beeck and BGL, we look forward to fighting for your ideas.
We have some great partners: we’re building on work already underway through the Federal Civic Tech Exit Project, run by the Better Government Lab and the Beeck Center, which has already conducted in-depth interviews with nearly 50 former federal digital service professionals. This next phase expands the contributions of the Beeck Center and BGL, drawing on Beeck’s national network of state and local digital service leaders and BGL’s focus on identifying and putting the world’s best research into practice to improve how government functions.
The work begins soon. If you’re interested, please complete this interest form and you’ll hear from us.
Start by expressing your interest in the form. You’ll be able to choose one or more ways to engage:
- Join a virtual workshop on February 10, 12, or 25 (register online)
- Attend an in-person workshop in DC on March 3 or 4 (register online)
- Contribute through an open-ended, anonymous survey
- Refer a colleague or friend who should be part of this conversation
- Follow along for updates, insights, and announcements
This initiative is hosted by the Federation of American Scientists (FAS) and Merici Vinton, with support from the FAS Government Capacity team, led by Loren DeJonge Schulman and Leya Mohsin.
We are launching this work in partnership with Georgetown University’s Beeck Center for Social Impact + Innovation, leveraging its extensive relationships with state and local digital leaders and the 10,000+ practitioners that participate in its Digital Government Network and the Better Government Lab at Georgetown University and the University of Michigan. We are also drawing on a small group of trusted advisors from across the digital government community.
- We will protect your identity. Our goal is to surface and publish the best ideas, not attribute individual comments.
- We intend to synthesize what we learn and share it with federal leaders, congressional staff, state and local digital teams, and future candidates and appointees. Participants who are excited to help shape, champion, or implement next-generation digital service models will have clear opportunities to engage in what comes next.
- Anyone who is or has been part of a government digital service ecosystem, or a close partner to one. This includes:
- Current or former staff of the U.S. Digital Service, 18F, or Technology Transformation Services
- Members of digital teams at federal agencies, states, and cities
- Congressional staff and policy experts who worked alongside these teams
- Partners, champions, and enablers who helped this work succeed
- If you’ve built, supported, funded, or depended on modern digital government, your perspective belongs here.
The Pentagon’s (Slimmed Down) 2025 China Military Power Report
On Tuesday, December 23rd, the Department of Defense released its annual congressionally-mandated report on China’s military developments, also known as the “China Military Power Report,” or “CMPR.” The report is typically a valuable injection of information into the open source landscape, and represents a useful barometer for how the Pentagon assesses both the intentions and capabilities of its nuclear-armed competitor.
This year’s report, and particularly the nuclear section, is noticeably slimmed down relative to previous years; however, this is because the format of the report has changed to focus on newer information, rather than repeating and reaffirming older assessments. As a result, this year’s report includes no mention of China’s ballistic missile submarines and their associated missiles, and includes only cursory mention of China’s air-based nuclear capabilities. It also excludes analyses of several types of land-based missiles entirely. However, this does not reflect changed assessments on the part of the Pentagon, but rather a lack of new information to report. Going forward, this means that analysts will need to read multiple years of CMPR reports in order to ensure that they are accessing the complete range of available information.
In addition, this year’s CMPR did not include any mention of China’s September 2025 Victory Day parade––which featured multiple new weapon systems––as the parade took place too recently; it will very likely be analyzed in next year’s report. The maps of missile base and brigade locations also appear to be out of date: the information is listed as “current as of 04/01/2024.”
While this year’s report did not include any earth-shattering headlines with regards to China’s nuclear forces, it provides additional context and useful perspectives on various events that took place over the past 12 months.
Stockpile growth
The CMPR states that China’s nuclear stockpile “remained in the low 600s through 2024, reflecting a slower rate of production when compared to previous years.” However, it reaffirmed previous years’ assessments that China “remains on track to have over 1,000 warheads by 2030.” China’s nuclear expansion over the past five years is now making this projection increasingly plausible, although even if it came to pass, China would still maintain several thousand warheads fewer than either the United States or Russia. Previous CMPRs had assessed that if China’s modernization pace continued, it would likely field a stockpile of about 1,500 warheads by 2035; however, this assessment has not been included in the CMPR since the 2022 iteration.
The dramatic expansion of China’s stockpile is primarily being prompted by the large-scale development and modernization of China’s next-generation intercontinental ballistic missile (ICBM) forces. In 2021, multiple non-governmental organizations (including our team at the Federation of American Scientists) publicly revealed the existence of three new ICBM silo fields capable of hosting up to 320 launchers for solid-propellant DF-31 class ICBMs. China is also more than doubling its number of silos for its liquid-fuel DF-5 class ICBMs, which the Pentagon assessed in its 2024 CMPR will likely yield about 50 modernized silos. Many of these missile types will be capable of carrying multiple warheads.
While the previous year’s CMPR indicated that China “has loaded at least some ICBMs into these silos,” the 2025 edition offers a valuable update: that China has now “likely loaded more than 100 solid-propellant ICBM missile silos at its three silo fields with DF-31 class ICBMs.” Our team continues to regularly monitor developments at the three silo fields using commercial satellite imagery and has not yet found sufficient evidence to corroborate this assessment; however, it is possible that the Pentagon’s assessment is primarily derived from other sources of intelligence, including human (HUMINT) and/or signals intelligence (SIGINT).
If China plans to continue its nuclear expansion, it will likely require additional fissile material, as China does not currently have the ability to produce large quantities of plutonium. The Pentagon assesses that China’s ongoing construction and planned commissioning of two new CFR-600 sodium-cooled fast breeder reactors at Xiapu “will reestablish China’s ability to produce weapons-grade plutonium.” However, the 2025 CMPR assesses that the first unit “is probably still undergoing testing,” and that “the second reactor unit is still under construction.” It is possible that this information is now out of date, as recent commercial satellite imagery now suggests that the first reactor unit may be operational.
Low-yield warheads
Previous editions of the CMPR had indicated that China was “probably” seeking low-yield warheads for escalation control during periods of small-scale nuclear crisis and/or conflict; however, the 2025 iteration is the first to offer an estimated yield value for such weapons, of “below 10 kilotons.” A recent technical history by Hui Zhang offers highly valuable data points for historical Chinese nuclear weapons tests, and suggests that China likely has the ability to produce smaller, low-yield warheads. Additionally, recent open-source reporting by Renny Babiarz with Open Nuclear Network (ONN) and researchers from the Verification Research Training and Information Center (VERTIC) found that China has been overhauling and expanding its warhead component manufacturing capabilities. Coupled with the expansion of the Lop Nur test site, this could indicate plans to upgrade China’s existing warheads, improve its ability to build more, or both.
The CMPR notes that the DF-26 intermediate-range ballistic missile (IRBM) and the air-launched ballistic missile (ALBM) carried by the H-6N bomber “are both highly precise theater weapons that would be well suited for delivering a low-yield nuclear weapon.” While the DF-26 had previously been identified as a likely carrier for a low-yield warhead, this is the first time that the H-6N’s ALBM has also been listed as a potential carrier.
Missile designations
It is often a complex endeavor to try and match China’s own missile designations to the names that are given to various systems by the Pentagon. This year’s CMPR, however, provides valuable confirmations for some of these missile designations. In particular, it confirms that both the DF-31A and DF-31AG ICBM are known to the Pentagon as CSS-10 Mod 2, which aligns with our understanding that both systems carry the same missile. It also strongly hints at the alignment between the CSS-18 and the DF-26 IRBM, as well as the CSS-10 Mod 3 and the DF-31B ICBM––a missile that was confirmed in the 2025 CMPR as the same missile that was launched from Hainan Island into the Pacific Ocean in September 2024 for the first time since 1980. This was the first mention of the DF-31B in the CMPR since the 2022 edition, and the first time that the missile’s existence under that designation has been confirmed.

The acknowledgement of the DF-31B’s existence coincides with the recent reveal of a likely silo-based version of the same missile during China’s September 2025 military parade. During that event, China unveiled a vehicle carrying a canister with the designation “DF-31BJ;” it is possible that the vehicle was a missile loader and the “J” likely indicates a silo basing mode, as the Chinese character “井” or “jing” means “well” and is used by the PLA to describe silos. We can therefore assume that the DF-31B ICBM has both a mobile and a silo basing mode, with the latter adding the J suffix to its designation.

Doctrinal shifts, arms control, and early warning
Beyond tweaks to China’s force posture and nuclear stockpile, the CMPR also offers some additional details with regards to its assessment of China’s nuclear doctrine. In particular, it expands on its previous assessments of China’s pursuit of an “early warning counterstrike (EWCS) capability,” which it calls “similar to launch on warning (LOW), where warning of a missile strike enables a counterstrike launch before an enemy first strike can detonate.” For the first time, the CMPR offers details into the capabilities of China’s early warning systems, stating that “China’s early warning infrared satellites [Tongxun Jishu Shiyan (TJS), also known as Huoyan-1] can reportedly detect an incoming ICBM within 90 seconds of launch with an early warning alert sent to a command center within three to four minutes.”
It also notes that China’s ground-based, large phased-array radars “probably can corroborate incoming missile alerts first detected by the TJS/Huoyan-1 and provide additional data, with the flow of early warning information probably enabling a command authority to launch a counterstrike before inbound detonation.” If this is accurate, it would appear that China is developing an early warning capability that functions in a similar manner to those of the United States and Russia, which rely on dual phenomenology to confirm the validity of incoming attacks before authorizing retaliatory launches.
The report also notes that “Beijing continues to demonstrate no appetite for pursuing […] more comprehensive arms control discussions,” including those related to a potential US-China bilateral missile launch notification mechanism.
Corruption
The CMPR focuses quite a bit on China’s ongoing measures to combat corruption, which has led to the removal of dozens of senior officials from their posts across the PLA Air Force, Navy, and Rocket Force. The report notes that “[c]orruption in defense procurement has contributed to observed instances of capability shortfalls, such as malfunctioning lids installed on missile silos”––a story which Bloomberg first reported in January 2024. The report notes that “these investigations very likely risk short term disruptions in the operational effectiveness of the PLA.”
Missiles and delivery systems
The 2025 report included a detail that in December 2024, “the PLA launched several ICBMs in quick succession from a training center into Western China.” Contrary to the launch from Hainan Island, there was very little public reporting about this salvo launch.
The CMPR also indicates an estimated growth in China’s ICBM and IRBM launchers by 50 each, although it is unclear whether these numbers include both finished launchers as well as those still under construction.
The following graph indicates the growth of China’s launchers and missiles, as assessed by the Pentagon, over the past 20 years. It is important to note that many of these missiles, including China’s short- and medium-range ballistic missiles and its ground-launched cruise missiles (GLCMs), are not nuclear-capable.
Our 2025 overview of China’s nuclear arsenal can be freely accessed here.
The Nuclear Information Project is currently supported with generous contributions from the Carnegie Corporation of New York, the New-Land Foundation, Ploughshares, the Prospect Hill Foundation, and individual donors.
What’s New for Nukes in the New NDAA?
At the time of publication, the NDAA had passed both chambers of Congress but had not yet been signed by the president. The Act, S. 1071, was signed into law on December 18.
Congress’ new annual defense spending package, passed on December 17, authorizes $8 billion more than the Trump administration requested, for a total of $901 billion. The FY2026 National Defense Authorization Act (NDAA) paints a picture of a Congress that is working to both protect and accelerate nuclear modernization programs while simultaneously lacking trust in the Pentagon and the Department of Energy to execute them. Below is an overview of provisions of note in the new NDAA related to nuclear weapons.
Sentinel / Intercontinental Ballistic Missiles
Every year since fiscal year (FY) 2017, Congress has inserted language into the NDAA prohibiting the Air Force from deploying fewer than 400 ICBMs (an arbitrary requirement put in place by pro-ICBM members of Congress fearful of any reductions in the force). The FY26 NDAA does not break this streak; in fact, it entrenches the requirement deeper into US policy. Rather than repeating the minimum ICBM requirement as a simple provision as previous NDAAs have done, Section 1632 of the new legislation inserts the requirement into Title 10 of the United States Code (the US Code is the official codification by subject matter of the general and permanent federal laws of the United States. Title 10 of the Code is the subset of laws related to the Armed Forces). This change means that Congress will no longer have to agree to and insert the requirement into the NDAA year after year. Instead, the requirement becomes the permanent standard and will require an affirmative change in a future NDAA to undo. Beyond requiring the Air Force to deploy at least 400 ICBMs, the new defense spending act additionally amends Title 10 of US Code to prohibit the Air Force from maintaining fewer than the current number of 450 ICBM launch facilities (essentially meaning that the Air Force cannot decommission any of the 50 extra launch facilities in the US inventory).
This change is indicative of a desire by Congress to bolster its protection of the ICBM program in response to increased scrutiny prompted by the ever-growing budgetary and programmatic failures of the Sentinel ICBM program. Interestingly, a provision in the Senate version of the defense authorization bill that would have established an initial operational capability (IOC) date for the Sentinel program of September 30, 2033, did not make it into the final text, suggesting a lack of confidence in the Air Force’s ability to achieve the milestone. With an original IOC of September 2030, the September 2033 date would have aligned with the Pentagon’s 2024 announcement that the Sentinel program was delayed by at least three years. The omission may thus indicate Congress’ anticipation of potential further delays to Sentinel’s schedule beyond the Air Force’s most recent estimate.
Nuclear Armed Sea-Launched Cruise Missile (SLCM-N)
In addition to protecting the most politically vulnerable nuclear weapons programs, the FY26 NDAA also aims to speed up US nuclear modernization and development, in some cases even beyond the requests of the administration. Despite the fact that the Pentagon’s FY26 budget request requested no discretionary funding for the nuclear-armed, sea-launched cruise missile (SLCM-N), the NDAA authorized $210 million for the program — on top of the $2 billion to the Department of Defense and $400 million to the National Nuclear Security Administration (NNSA) included in the July 2025 reconciliation package to “accelerate the development, procurement, and integration” of the SLCM-N missile and warhead, respectively.
Most notably, the new defense authorization act speeds up the SLCM-N’s deployment timeline by two years. Section 1633 of the act repeats the IOC date of September 30, 2034, established by the FY24 NDAA, but also requires DOD to deliver a certain number of SLCM-N — a number to be determined by the Nuclear Weapons Council — by September 30, 2032, to achieve “limited operational deployment” prior to IOC.
Future nuclear development
In addition to speeding up the deployment timeline for SLCM-N, the FY26 NDAA initiates and accelerates the development of new nuclear weapons by creating a new NNSA program in addition to the stockpile stewardship and stockpile responsiveness programs: the rapid capabilities program. The new program — established by section 3113 of the NDAA via insertion into Title 50 of the US Code (War and National Defense) — is tasked with developing new and/or modified nuclear weapons on an accelerated, five-year timeline (compared to the traditional 10-15 year timeline for new weapons programs) to meet military and deterrence requirements.
Numerous provisions in the new NDAA reflect a lack of trust by Congress in DOD and DOE’s ability to execute and deliver nuclear modernization programs. The creation of stricter and more detailed reporting requirements and action items for making progress on various nuclear weapons related programs constitute an increased effort by Congress to micromanage nuclear modernization programs.
One example of nuclear micromanagement in the act are Sections 150-151 regarding the B–21 bomber. Section 150 mandates the Air Force to submit to Congress:
- An annual report on the new B–21 nuclear bomber including:
- An estimate for the program’s average procurement unit cost, acquisition unit cost, and life-cycle costs,
- “A matrix that identifies, in six-month increments, plans for and progress in achieving key milestones and events, and specific performance metric goals and actuals for the development, production, and sustainment of the B–21 bomber aircraft program” (with detailed requirements for how the matrix should be subdivided and what information it must include),
- A cost matrix (also in six-month increments and including specified subdivisions),
- A semiannual update on the aforementioned matrices.
In addition, the provision requires the US Comptroller General to “review the sufficiency” of the Air Force’s report and submit an assessment to Congress. The following section of the NDAA additionally requires the Air Force to submit to Congress — within 180 days of the act’s enactment — “a comprehensive roadmap detailing the planned force structure, basing, modernization, and transition strategy for the bomber aircraft fleet of the Air Force through fiscal year 2040” (once again, including detailed requirements for what information the roadmap must include).
In a similar fashion, Sections 1641 and 1652 lay out strict reporting and planning requirements for sustaining the Minuteman III ICBM force and developing the Golden Dome ballistic missile defense program, respectively.
Such efforts by Congress to increase its management of US nuclear weapons programs could be in response to repeated and ongoing delays, cost overruns, and setbacks, or could simply reflect Congress’ desire to seize more control over the nuclear enterprise to get what it wants (or, likely, a bit of both). To be clear, Congressional scrutiny into nuclear programs is welcome amidst a trend of over-budget and behind-schedule procurement of unnecessary weapon systems by the Pentagon. Congress can and should play an important role in ensuring that the Departments of Defense and Energy are not handed blank checks for nuclear modernization.
That said, with this legislation, Congress authorized nearly $30 billion in spending for select nuclear weapons programs in FY26 alone. The tables below, developed by the Center for Arms Control and Non-Proliferation, show a breakdown of Congress’ authorizations for these programs:
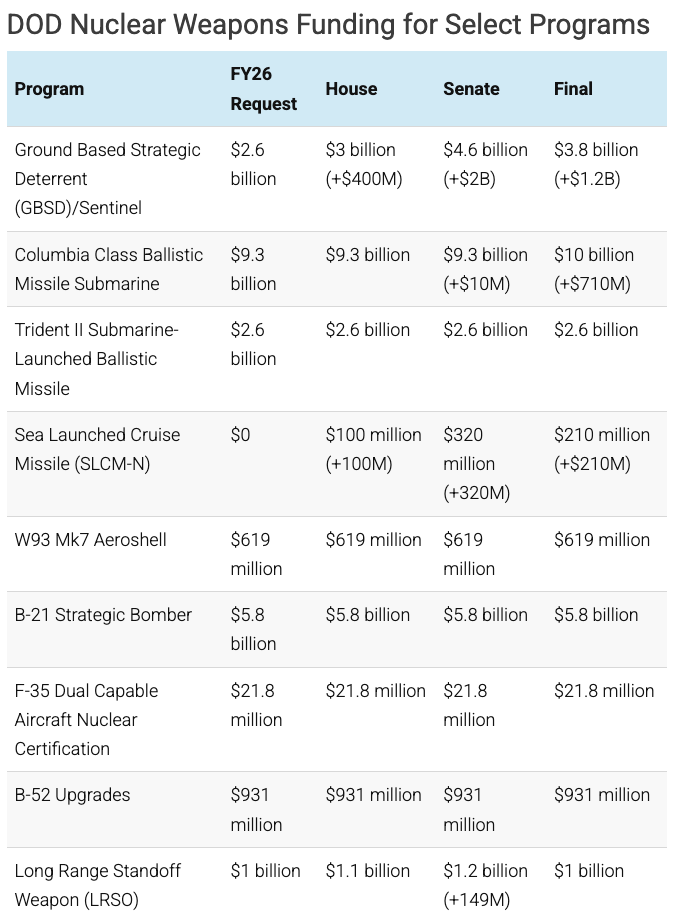
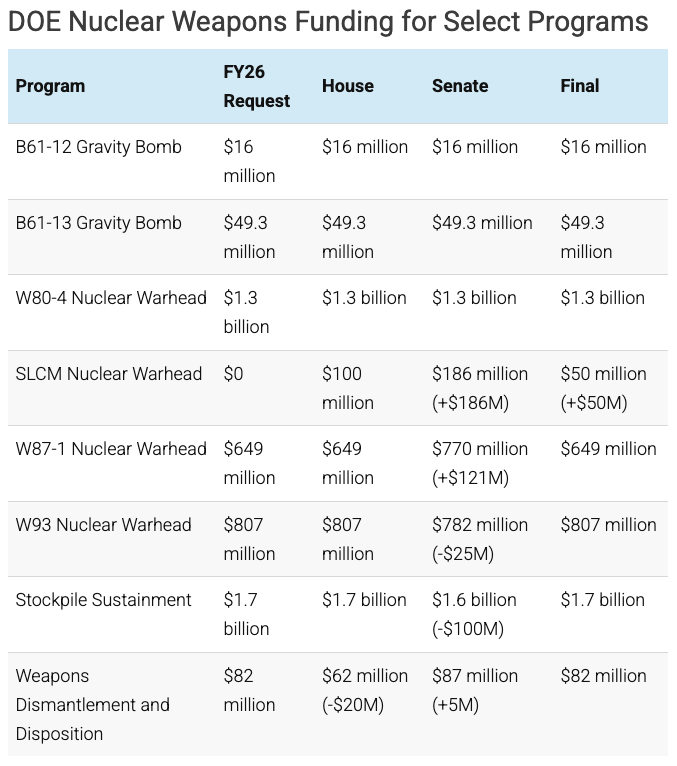
This article was researched and written with generous contributions from the Carnegie Corporation of New York, the New-Land Foundation, Ploughshares, the Prospect Hill Foundation, and individual donors.