Successful Pooled Hiring Starts With Diving the Deep End
The Office of Personnel Management has been busily reversing course on federal workforce reductions with some splashy hiring announcements. In December, it launched Tech Force, a pooled recruitment effort targeting 1,000 early-career technologists to be placed across agencies for two-year stints. In March, it stood up across-government shared certificate for project managers. It launched an Early Career Talent Network spanning five job categories. Two weeks ago, it expanded Tech Force into cybersecurity. OPM Director Scott Kupor has been explicit about his ambition: this is a “model for more centralized, efficient hiring across government.”
I’ll bite: yes, there’s a lot of promise in that! The instinct behind all of these actions builds on years of initiatives meant to create efficiencies out of the hundreds of thousands of hires made federally each here. Pooled hiring, which should include one well-designed announcement, one shared assessment, and many agencies drawing from the same pool of qualified candidates, is exactly the kind of tool the federal government should be using. I saw this up close when I was at OMB and I fully drank this Kool-Aid. The logic is compelling: (typically) the federal government processes over 22 million applications and hires over 350,000 people into public service every year. No private employer operates anywhere near that scale, which I still believe can be an asset, and pooled hiring creates the entry point to get there.
But pooled hiring has a track record (going back several administrations), and it’s uneven. Most recently, the Biden administration championed it most ambitiously during the infrastructure surge, where OPM partnered with seven agencies and hired roughly 5,000 employees, doing things like USDA hiring 39 HR specialists off a single certificate (if this sounds underwhelming to you, trust me when I say it’s mindblowing to your average hiring manager; more explained shortly). But the same period produced plenty of pooled actions that generated duplicative work, agency foot-dragging, and candidates who aged off certificates before anyone made them an offer. FAS and others have been studying these challenges in the context of the permitting workforce surge, and the problems are structural, predictable, and repeating. Also? Solvable.
The concept has promise but implementation has kept breaking in the same places. This piece is about why and about how to get it right, now, while there’s political will and active momentum to use it.
The Design Error at the Center of Everything
First, a quick explainer on how this actually works — because “pooled hiring” gets used loosely and the mechanics matter. A pooled hiring action is a competitive job announcement run either by OPM centrally or by a lead agency on behalf of multiple agencies and intended to fill multiple open positions in multiple agencies. Instead of each agency posting its own announcement, recruiting its own applicants, and running its own assessment, one announcement goes out, one applicant pool forms, and one assessment process screens candidates into a shared certificate of eligibles (government-speak for a ranked list of candidates that agencies can choose from). Agencies that have signed on to participate can then make selections from that certificate without having to run their own action from scratch. OPM-run actions (like the current Tech Force or the project manager cert) work the same way, just with OPM as the lead rather than a single agency. Either way, the cert is the output: a ranked list of candidates who have been assessed as qualified, available to any participating agency to hire from without having to solicit new resumes, review their qualifications, administer assessments, or other tedious parts of the hiring process.
That’s the theory.
The shared certificate is where most implementations stop. Agencies get a screened list and then do their own thing — their own interviews, on their own timelines, with their own offer processes. Or maybe they don’t, even when they said they would! The coordination ends at the cert. Everything downstream remains fully siloed at each agency.
This is far from the ideal that most policymakers have in mind and what many private employers do. A genuine pooled hiring action pools the whole pipeline. Recruitment, assessment, interviewing, and offers — all coordinated, all running in parallel across participating agencies. That doesn’t work for every role, but in surge situations, or for roles where agencies make dozens of hires of the same roles every year, it’s great. Agencies don’t just agree to draw from the same pool. They show up on the same interviewing days. They make offers on the same compressed timeline. Candidates who applied once get considered by many agencies simultaneously with each running its own slow-motion version of the process.
Almost nothing the federal government currently calls “pooled hiring” actually does this. The new OPM actions are no exception. Tech Force is better marketed than previous efforts, and the private-sector partnerships are genuinely new. But the selection and offer stages remain siloed at each agency and I’ll be very curious if they make selections. That’s the design flaw everything else flows from.
What Breaks When You Don’t Fix the Design
When I was at OMB, we saw these failure modes up close, in what were probably deeply frustrating meetings with the valiant program team as we learned where the seams were. Some things we saw:
Pooled hiring worked when it was a clear administration priority and had OPM and OMB supplementation. Early indicators suggest that Tech Force has success because it’s clear that the administration, the OPM director, and OPM staff are both giving it attention and smoothing implementation behind the scenes. That’s good for proof of concept, but it doesn’t show the weaknesses that can emerge when administration accountability doesn’t hold agencies to delivery on innovation hiring methods.
Agencies didn’t trust screening they didn’t run. OPM’s own guidance requires agencies making selections from another agency’s certificate to verify that the original qualification and assessment criteria are appropriate for their position. That verification step becomes a second screening — which defeats the efficiency rationale entirely. Agencies that double and triple-screened candidates created more work than if each had run its own action from scratch. The fix isn’t better guidance, it’s building trust into the design upfront, by ensuring the people trusted with the most relevant subject-matter expertise help design the assessment in the first place.
Demand didn’t stay put. Agencies raised their hands, agencies or OPM ran a resource-intensive recruitment action, and then agencies were slow to hire — or circumstances changed before they did. The August 2024 OMB/OPM hiring memo specifically directed agencies to review available shared certificates before launching new hiring actions — a discipline that, if actually followed, would force better demand alignment upfront. It mostly didn’t happen and, absent the sort of prompting we talk about later, is hard to enforce. Partly this is a culture problem, but it’s also a structural one: agencies that don’t plan for talent surges find that new hiring needs don’t align with their existing workforce plans or their capacity to recruit, assess, and onboard. You can’t opt into a pooled action and then be surprised when the pool fills.
We struggled to tell the right people, and the system didn’t either. There’s a more fundamental problem sitting underneath the demand-alignment failure: hiring managers and HR specialists often don’t hear about pooled hiring announcements at all, and when they do, it’s generally not with enough lead time to actually prepare. Pooled actions get announced through OPM memos and Chief Human Capital Officers (CHCO) Council communications that circulate at the leadership level (and boy howdy did we circulate!), but that information doesn’t reliably travel to the hiring manager who is already three weeks into drafting a job announcement for the exact role sitting in a shared cert. And when it does arrive, it arrives as information: there’s no deadline attached, no checklist triggered, no reason to stop what they’re already doing. As it stands, among the 200K+ hiring managers, most made very few hires a year or in their overall career, so learning a process with barriers to entry was challenging.
Nothing interrupts the default action.The deeper problem is that nothing in the hiring workflow itself cues anyone to look. When a hiring manager initiates a new action in the hiring system, they’re not pushed or incentivized in any systematic way to check for an existing cert. When an HR specialist begins drafting a job announcement, no flag surfaces to say: a shared certificate for this position series already exists, do you want to use it? The system simply lets them proceed. This means that even when an agency or OPM has done the work of running a pooled action and producing a cert, agencies duplicate that effort anyway; less due to indifference, but because the path of least resistance is to do what they’ve always done, and nothing in the process interrupts that default.
The fix here is partly cultural but a lot technical. The Agency Talent Portal and USA Staffing need to surface available shared certificates at the moment a hiring manager or HR specialist initiates a new action for a covered position: as a required check embedded in the workflow itself. If you’re about to post a GS-12 data scientist announcement and there’s an active governmentwide cert for that exact series and grade, the system should tell you, right then, before you proceed. Opt-out, not opt-in. The current design assumes awareness that doesn’t exist and motivation that isn’t reliable.
Pooled actions were expensive for the “owner” and the experts: While cost-saving overall, running pooled actions could be resource and time consuming for the “owner,” and particularly the subject matter experts brought in for assessment, particularly when hires were not ultimately made.
The position description bottleneck. Pooled hiring inherits whatever good and bad planning exists in agencies’ position description (PD) libraries. Even for commonly-hired roles, position descriptions are not always readily accessible and, likewise, standard assessments often don’t exist at every grade level. But it’s a bigger challenge than that: the whole GS system presumes (competencies, job task analyses, and more) that every job is highly specialized, not generalizable for cross-agencies pools. FAS documented this directly: OPM and the Permitting Council collaborated to create a pooled, cross-government announcement for Environmental Protection Specialists — one job announcement producing a candidate list many agencies could use. But the assessment became a bottleneck because standard assessments didn’t exist for each grade level in the announcement, requiring significant additional development time. This isn’t an edge case, it’s a Tuesday. Breaking! OPM Director Kupor just announced a new AI tool to generate PDs! We’ll follow with interest.
Hiring managers couldn’t get access without a permission chain. For a new hiring innovation to be adopted, you’d think that all the barriers, incentives, and opt-in/out dynamics would be aligned. You’d be wrong. Pooled hiring at a “mother may I” architecture: system passwords and access, coordinators, gating processes, intermediaries between hiring managers and shared certificates. It’s a design flaw dressed up as compliance. The same 2024 memo had to explicitly direct agencies to update hiring manager permissions in the Agency Talent Portal. That it needed to be said tells you everything about how poorly the access question had been handled. As FAS and the Niskanen Center jointly documented in their analysis of the current OPM hiring memos, the toughest tasks are also the most crucial: changing the culture around hiring to empower managers, and actually letting line managers be managers.
Talent teams could be a good idea that keeps getting launched without the authority or resources to actually work. Every administration for the past decade has called for empowered agency talent teams — small, specialized units charged with driving hiring innovation, adopting new tools like SME-QA, and coordinating participation in pooled actions. M-24-16 explicitly called for agencies to create and sustain these teams, and the current OPM Merit Hiring Plan has stood one up at the central level as well. The concept has potential but execution has been consistently undercut by the same failure mode: no committed resources, no authority to intervene, no access, and no product mindset. In understaffed agency HR offices that were not empowered to “get to yes”, the function hasn’t meshed well, and moreover, it’s arrived in a system that already lacks strong strategic workforce planning, a key enabler of its potential success.
As FAS and the Niskanen Center documented agency talent teams, OPM communications and education support, and the necessary systems changes all require people, money, and IT investment that hasn’t materialized. Announcing a mandate is not the same as funding its execution.
But underfunding isn’t the only problem. Even well-resourced talent teams have struggled when they lacked the institutional standing to actually change agency behavior. The core failure mode is assuming that having good people in the building is enough — that talent solves problems on its own, without a clear theory of change about authority, access, and how decisions get made. An agency talent team that is advisory in nature, without a direct line to hiring managers and HR decision-makers, without leadership backing when they push back against entrenched process habits, and without metrics that create accountability for adoption, is not going to move the needle on pooled hiring participation. It’s going to produce reports and hold workshops and then watch agencies do what they were already going to do.
Veterans preference created confusion that nobody addressed proactively. Preference applies differently in delegated examining versus merit promotion contexts. When agencies share certificates across those lanes, legal ambiguity creates real hesitation. This is genuinely solvable — but only if OPM issues targeted guidance with each pooled action as a standard part of the launch package. Stepping back, it’s necessary to state that any type of absolute preference is going to make pooled hiring challenging. Clarifying guidance is a Band-Aid.
Small technical barriers compound the problem. One underreported friction point: shared certificate policies can constrain agencies from sharing certs across different geographic locations designated in the original announcement, or across different hire types — temporary versus permanent. An agency running a pooled action for DC-based positions can’t easily extend that cert to field office hires. A cert issued for permanent positions doesn’t smoothly cover term appointments. These are solvable technical problems that OPM and OMB could fix through policy revision but they require someone to actually map the barriers before designing the action.
And when agencies go it alone anyway, the burden multiplies for everyone. This is the part that gets lost in discussions that treat siloed hiring as merely inefficient rather than actively harmful. When agencies that are already understaffed — particularly permitting and HR teams — don’t leverage opportunities to work together, bottlenecks compound. Pooled hiring isn’t just a convenience for well-resourced agencies. For teams that are already stretched, it’s the difference between a manageable workload and an impossible one.
Agency HR leads without the skills or network to work across agencies. Like so much else, pooled hiring depends on relationships. OPM and agencies have not carefully selected the HR managers who not only understand the potential policy barriers to working across agencies but the collaboration skills and networks to solve problems quickly.
The Assessment Question: Use the Right Tool Not the Easy One
If you’ve read this far, you’ve probably heard of things like SME-QA, the greatest acronym in the hiring world. Let’s talk assessments.
The default federal hiring assessment — the self-assessment questionnaire — is effectively worthless for identifying technical talent. As Jennifer Pahlka has put it, the system has been built so that the most important knowledge is how the hiring process works instead of the knowledge needed to do the job. A nationally recognized programmer once applied to the Department of Defense and was initially rejected because their resume described real expertise in language that didn’t match OPM’s classification keywords. Meanwhile, someone who understood the system could mark themselves “expert” across every self-assessment category with no verification at all.
The Subject Matter Expert Qualification Assessment, or SME-QA, was one of the skills based hiring toolkits developed to fix this: real experts screen for real skills, with HR ensuring merit principles hold. SMEs independently review every resume. Candidates who clear the initial bar then go through further steps like structured interviews, coding exercises, or written assessments — administered by other practitioners in the field, not generalist HR staff. For technical roles going into a pooled action — data scientists, cybersecurity professionals, engineers — SME-QA paired with a shared certificate is close to the ideal design. Build the assessment once with governmentwide SME input, share the cert, and every agency draws from a pool that was actually screened by people who know the field.
But any skills based hire practice has a scaling problem that’s been documented since the first USDS pilots. The work is resource intensive for federal agencies not used to dedicating so much SME time to a hiring process. As Niskanen’s recent analysis of the Chance to Compete Act makes clear, new written assessments developed by industrial-organizational psychologists are extremely resource-intensive to produce — likely prohibitively expensive at the scale needed to cover broad swaths of the federal workforce. But there are roles and moments where such dedicated investment makes sense.
The design principle that should govern this: pooled hiring should be an opportunity to concentrate assessment burden at the enterprise level, not multiply it at the agency level. Build the assessment once, or maximize use of SME-QA time, governmentwide, for roles where it genuinely matters. Actually use them consistently rather than rebuilding from scratch at each agency. And as Niskanen argues, transform OPM’s role from compliance monitor to assessment engine: a marketplace of vetted, shared tools agencies can pull from rather than commission independently.
There’s a trust dividend here too. Agencies that contribute subject-matter experts to the assessment design have far more reason to trust the resulting certificate. Skin in the game at the assessment stage translates directly to confidence at the hiring stage.
A Note On Listening
Many successful pooled actions worked because OMB and OPM (or other senior White House offices) gave attention, capacity, authority and accountability to the process, bolstering agencies who were being asked to execute hiring with unusual flexibility and competence.
Overall, however, when agencies told OPM and OMB that pooled hiring was hard for them to execute alone, the response from the center was too often some version of: the guidance is out there, the instructions are online, that’s how the process works. Agencies described a cascade of rigidities that made implementation genuinely difficult, and we weren’t always responsive. We treated compliance problems as communication problems. If agencies weren’t doing it right, they must not have understood it correctly, so the answer was more guidance, clearer FAQs, better webinars.
That’s the wrong diagnosis. What they were telling us was that the process didn’t fit their reality and that the gap between what the policy assumed and what their operations actually looked like was wide enough that no amount of additional instruction was going to close it. When the people responsible for carrying out a policy are consistently telling you it’s hard in specific, consistent ways, the right response is to ask what’s broken in the desig.. The people designing these systems need to hear that feedback as signal instead of as resistance to be overcome.
This is the reason why the recommendations in this piece are about structural changes to how pooled hiring is designed, not about better outreach or clearer communications. Agencies don’t need another memo explaining how shared certificates work. They need a system that works in the conditions they’re actually operating in.
How to Actually Do This Right
The current OPM actions are a real opportunity. Here’s what would make them work, stated as plainly as possible.
Lock in real demand before you launch. Not expressions of interest: actual hiring commitments with funded billets and named positions. The failure mode is OPM building a pool that agencies shop from slowly or not at all. Require agencies to submit hiring forecasts before they’re included in a pooled action, and hold them to those forecasts with visible accountability.
Build assessment infrastructure before the announcement goes up. Standardized PDs, validated assessments, and clear SME selection criteria that agencies trust need to exist before the action launches. Thecentralized position description library called for in M-24-16 is the right vehicle. Critically, assessments need to exist at every grade level included in the announcement.
Build the awareness and the system prompt together. Upgrade communication on pooled hiring announcements directly to hiring managers and HR specialists. But communication alone won’t fix this. The Agency Talent Portal and USA Staffing need to surface available shared certificates at the moment a hiring manager or HR specialist initiates a new action for a covered position series and grade. This should be a required check embedded in the workflow itself — before they proceed with drafting a new announcement. If you’re about to post a GS-12 data scientist announcement and an active government-wide cert exists for that series and grade, the system should tell you right then. The current design assumes awareness that doesn’t exist and motivation that isn’t reliable.
Pool the interviewing, not just the screening. Coordinated interviewing days. Same-day or 48-hour offer authority for hiring managers. Agencies competing for the same candidates simultaneously, not sequentially. Cross-agency onboarding cohorts that start together and build peer networks from day one. This is what actually compresses time-to-hire.
Fund and empower talent teams as implementation infrastructure. Every idea in this piece requires someone inside each major agency whose job it is to make that happen. That’s what a talent team is for. But talent teams need three things that they rarely get: a dedicated budget line, direct access to the hiring managers and HR leadership they’re supposed to influence, and metrics that hold them accountable for adoption rates and actual hiring outcomes rather than process activity. A talent team of one person with a shared budget and no senior sponsor is not an implementation strategy.
Give hiring managers direct access. Update the Agency Talent Portal permissions. Eliminate the intermediary layers between a hiring manager and a cert they’re authorized to use. Hold managers accountable for whether they hire. Culture change here is real but it follows structural change: when managers have direct access and clear authority, behavior shifts.
Make follow-through a metric with teeth. Agencies that opt in and don’t hire should have to explain why, publicly, to the President’s Management Council.The voluntary participation problem doesn’t get solved with please-and-thank-you memos.
Run continuous pooled actions for common roles. HR specialists, contracting officers, environmental specialists, IT managers — these aren’t surge needs, they’re permanent ones. A cert that’s always open, with agencies drawing from it as needs emerge, is far more useful than a prestige program that runs once a year and then goes quiet.
The Bigger Lens
(with thanks to Gabe Menchaca and Peter Bonner for making the stronger argument)
Pooled hiring is a microcosm of a question the federal government seesaws on constantly: what does it mean to govern as an enterprise rather than as several hundred agencies that happen to share a payroll source?
This requires admitting something those of us who have worked in the center don’t always say plainly: agencies and their leaders are protecting their turf for understandable reasons. They are accountable for their missions, their budgets, and their outcomes. When a pooled hiring action asks them to trust a cert they didn’t design, coordinate interviews around a shared calendar, and accept that they won’t get every single thing they want, and that’s a big ask! The trade may be worth making, but it doesn’t happen automatically, and the center has not historically done a good job making the case for why, or building the conditions under which agencies can actually say yes.
That’s a collective action problem, and it’s harder than it looks. It requires genuine leadership alignment across all the agencies involved, and a center that has made the benefit of cooperation concrete and visible rather than just asserting it in guidance. Too often the response to non-participation has been more documentation rather than an honest look at what the actual barrier was. That’s compounded by a structural problem worth naming: agencies are accountable for their HR outcomes but OPM holds much of the compliance authority over how hiring gets done. Accountability without authority produces exactly the behavior you’d expect.
The federal government has demonstrated it can operate differently. The BIL surge, the data scientist certs, USDA’s HR specialists (and maybe Tech Force) worked because the conditions were right: shared design, locked-in demand, leadership alignment, enough urgency to overcome the default toward agency autonomy. The question is whether we can build those conditions deliberately rather than stumbling into them during a crisis. That requires a solid theory of change about how cross-agency infrastructure actually gets adopted: one that takes agency self-interest seriously as a design constraint rather than an obstacle to be overcome by memo. Get that right, and pooled hiring becomes a model for how the federal government decides what to do together and what to do apart. That’s a bigger prize than faster hiring. It’s a more functional government.
Strengthening the Federal Cycle of Learning and Adaptation by Closing the Loops
The federal government has a feedback-loop problem.
Regularly generated information, including evidence, performance information, and qualitative insights from implementation, too often fails to shape decisions. Evidence may be reviewed without changing priorities; performance data may be tracked without clarifying what it informs, and implementation feedback may reach leadership without surfacing what works for whom and why, or suggesting next steps. The components of a cyclical learning system linking priorities, questions, evidence, decisions, and implementation information exist in theory and on paper, but the connective tissue that turns all of these components into a functioning cycle of learning and adjustment is lacking. Information and artifacts alone don’t necessarily facilitate learning and adaptation; strengthening federal feedback loops requires embedding translation and use into decision-making from the start.
This memo is not a case for new infrastructure. The Evidence Act, learning agendas, evaluation plans, performance frameworks, and customer experience authorities already exist; what they do not yet add up to is a learning system. The translation this memo proposes is turning the infrastructure we have into the learning system we need, and it’s addressed to federal program leaders, policy officials, evaluation and evidence staff, performance officers, and strategic planning teams who already sit inside it and are best positioned to make it function as intended.
Challenge and Opportunity
The federal government already operates within a broad cycle of goal-setting, evidence generation, performance review, implementation, and reporting. On paper and in principle, this cycle should allow for learning, adjustment, and improvement to federal programs over time. In practice, however, agencies vary in how consistently they translate such information into planning, decision-making, or course-correction. Federal agencies have made progress in building and using evidence, but translating that information into timely operational or policy revisions remains uneven.
The core problem isn’t production; it’s translation, and the translation failure shows up as “so what” gaps on both sides of the information pipeline. On the input side, receivers of information are often left asking what they’re supposed to do, and on the output side, a second question appears – “is it my job to act on this, and if so, how?”. Research findings are often too slow, too caveated, or too disconnected from immediate policy and management questions. Performance data may show quantitative changes in outputs, costs, or enrollment without revealing the mechanisms behind them or the practical implications for implementation, or cueing the design apparatus that could apply these insights. Feedback from frontline service providers and affected users might reach leadership mainly through quantitative indicators, dashboards, or status updates, which don’t always capture lived experience, causal explanation, or informed suggestions for course correction. Without named owners and defined next steps, even the most actionable information tends to circulate rather than convert.
Three gaps sit behind this pattern. First; a context gap – decision-makers often lack the full picture, because qualitative indicators and customer experience research arrive separately, or later than quantitative evidence, leaving them with only a partial view of what’s working well or driving implementation problems. Second, an action gap; even with a complete view of the picture, it’s not always obvious which lever applies, on what timeline, or with what tradeoff. Third, an ownership gap; it’s often unclear who is responsible for translating any given signal into a decision, and this ambiguity means that insights can be observed without being acted on. Together, these three gaps leave evidence and feedback insufficiently integrated into decision-making routines.
The problem is also structural; decision-makers face turnover, competing priorities, time limits, and management pressures, and thus, evidence needs a more robust pathway. Devoid of clear translation, trusted messengers, and defined or mandated use points, even the most relevant information can be too late, too ill-timed, or too jargon-heavy to influence decisions, resulting in missed adaptation opportunities.
The federal government doesn’t need an entirely new learning architecture. It needs to make the one it already has more usable. Agencies can do this in a few ways. First, by building stronger translation functions by creating space for “knowledge brokers” (people or teams whose core function is to translate evidence into decision-relevant language and maintain the required relationships that make the translation trusted). Second, by incorporating the use of evidence, performance, and implementation feedback into policy and program work from the start. Third, by creating better pathways for implementation and lived-experience feedback to reach leadership in ways that resonate with them and support action.
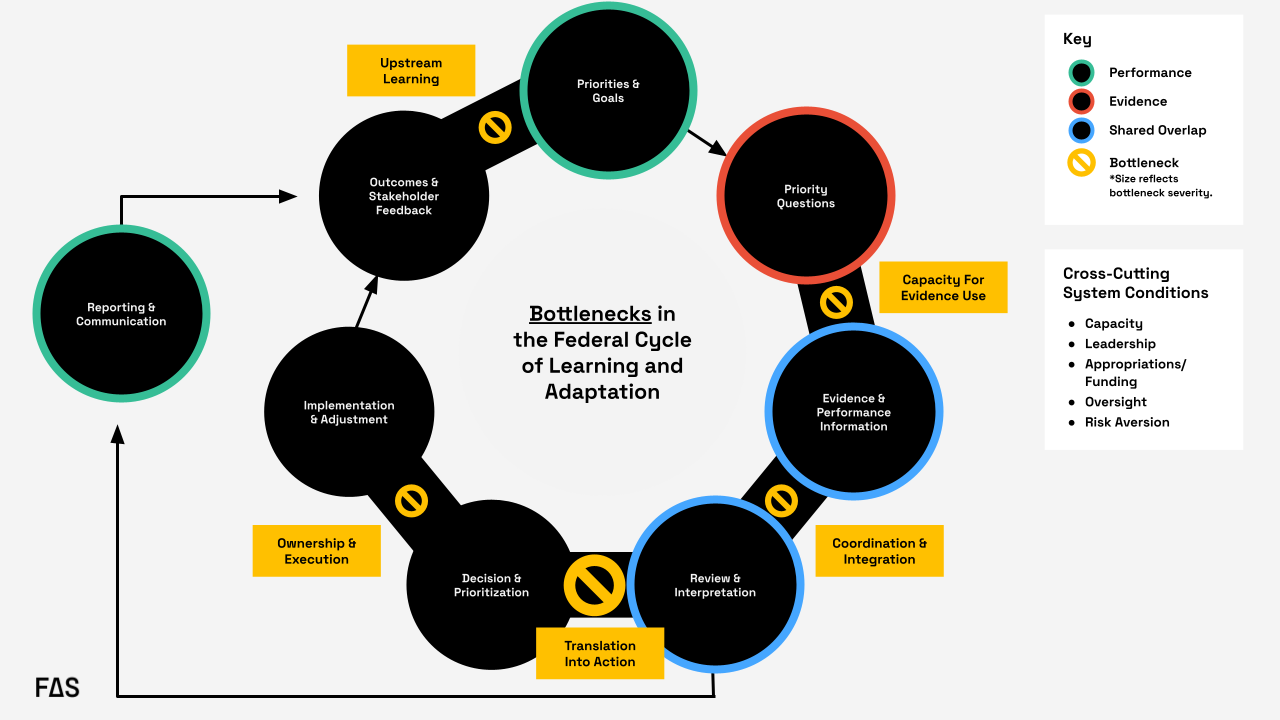
Formal federal guidance envisions a closed “loop” linking goals, priority questions, evidence, and performance information, along with review, decision-making, implementation, reporting, and feedback. In practice, the loop often degrades at key handoffs: evidence-use capacity, coordination and integration, translation into action, ownership and execution, and upstream learning from outcomes. The most significant recurring bottleneck occurs during the transition from review and interpretation to decision and prioritization, where information is generated and reviewed but does not reliably translate into action.
Plan of Action
We need to shift from a system that collects information to a system that uses it.
Agencies should create or strengthen embedded translation functions that connect evidence, performance information, implementation experience, and policy levers at the moment decisions are being made. The key is to move from a dissemination model to a utilization model. Instead of “produce, disseminate, and hope for uptake”, agencies should do the following:
Recommendation 1. Designate a knowledge broker to facilitate regular decision briefs…
or routines that create structured opportunities to clarify what’s known, what’s uncertain, and what actions are available – beginning with a defined set of high priority issues rather than every single decision the agency needs to make.
This recommendation targets the translation into action bottleneck in Figure 1; the handoff from review and interpretation to decision and prioritization, which can be considered the most significant recurring point of failure in the federal cycle of learning and adaptation. In practice, this means assigning this function to a role or small team housed in an existing performance, evaluation, strategy, or program office and requiring that group to support recurring decision points with short decision briefs. Those briefs should identify the decision, synthesize relevant evidence, performance trends, and implementation feedback, and specify available actions, tradeoffs, and owners.
For example, in the rollout of the FAFSA Simplification Act, a knowledge broker tied specifically to this initiative could have translated readiness indicators, beneficiary feedback, and information from financial aid administrators into decision-ready synthesis for the officials with decision authority who were attempting to course correct in real time. Instead, significant delays turned the rollout into a high-profile implementation issue.
Crucially, this function should start narrow. Rather than positioning a knowledge broker as an all-purpose translator for an agency’s full decision load, the initial portfolio could be scoped to a small set of priority issues. Starting narrow lets the broker establish credibility and relationships that make translation trusted and refine what the routine and explicit outputs are before it scales – the portfolio can scale later. This gives agencies a defined mechanism for turning reviewed information into decisions rather than leaving that handoff informal. Within the federal government, the Office of Evaluation Sciences has modeled how an embedded team of evidence translators can work alongside program offices rather than from a silo.
Recommendation 2. Start policy initiatives and evaluation planning with a real question…
or decision, identify the user, specify the lever, and clarify – in advance – what different findings would imply. Incorporating this thinking upstream changes the role of evidence from a retrospective input to an operational tool.
This recommendation mainly addresses the translation into action bottleneck, and secondarily, the evidence-use capacity bottleneck. Agencies can operationalize this by building decision framing into existing learning agenda and evaluation planning processes, both of which are already required under the Evidence Act. Before an evidence product is commissioned or a performance indicator is selected, program offices can be required to answer four questions on the record: What decision is this for? Who will use it? What lever would change as a result? What finding would lead to what action?
In a hypothetical example, say that USDA’s Food and Nutrition Service (FNS) wants to commission a new evaluation or analysis regarding SNAP redetermination churn (the pattern of households losing SNAP benefits at recertification and then re-enrolling, often for procedural reasons rather than eligibility). The four questions noted above can be answered on the record before the work begins. The decision is whether to issue new guidance to state agencies on recertification practices and what that guidance should encourage. The user is the FNS administrator and the relevant policy office, with state level SNAP directors as the implementing audience. The lever is subregulatory guidance. The early thinking regarding mapping findings to actions would specify, in advance, which patterns or insights would trigger which associated response. This way, when the findings arrive, USDA wouldn’t be starting from scratch with the “what do we do with this” question; the decision architecture would already be in place.
Pre-specifying these conditions in a short decision-framing memo that travels with the work turns evidence from a retrospective deliverable into a tool scoped to a specific decision or policy window. The same logic extends to decision memo templates themselves, which can include standing prompts such as “what evidence informed this decision?” and “how will we learn about this in real time?”, so that utilization is built in.
Recommendation 3. Create pathways for easier access to mixed methods evidence and insights from lived experience.
Recommendation 3 targets the coordination and integration, and upstream learning bottlenecks; the gap where evaluation, performance, administrative, qualitative, and customer experience data move at different speeds, live in different places, and reach decision-makers as parallel streams. Insights from lived experience – what programs actually look and feel like to the people using them – are particularly likely to be separated from information that reaches leadership, arriving as anecdotes, if they arrive at all. Because these problems are distinct; the recommendations can be broken down and addressed at the agency level.
Recommendation 4. Standardize decision-ready formats that consolidate quantitative and qualitative evidence.
Agencies should build standardized decision templates and briefs that present quantitative indicator-level data alongside narrative summaries of lived experience and implementation conditions, so decision-makers aren’t expected to synthesize across disparate sources on their own timelines. The resulting artifacts should be tied to recurring decision moments (budgeting, guidance revisions, program reauthorization) so that they can be used in real time.
In the FAFSA Simplification Act rollout, the Department of Education leadership faced this problem: application data, technical readiness indicators, information from financial aid administrators, and user feedback existed separately, and moved at different speeds. A standardized decision-ready format could have pulled those streams together; pairing completion trend data with brief narratives or exemplary quotes regarding what applicants and financial aid offices were actually encountering, rather than leaving leaders alone to assemble the picture in real time
Recommendation 5. Actively use existing general clearance mechanisms for rapid qualitative and user experience research.
Agencies should make use of standing generic clearance mechanisms that allow them to fast-track small qualitative and user experience studies (for example, up to 100 respondents, completed within a fixed time window) when unexpected findings need rapid explanation. This would allow for the ability to run a tightly scoped evaluation in weeks rather than months, which is the operational timescale at which decisions frequently move. Without it, the qualitative evidence needed to explain any type of performance anomaly often arrives after the decision or policy window has closed.
For SNAP redetermination churn, this would let FNS turn around a short, scoped evaluation of why participants are dropping off at a specific step in the recertification cycle in weeks rather than months. The insights could then inform the next round of guidance rather than coming in after the fact.
Recommendation 6. Build customer-first indicators built into existing federal reporting requirements.
Beneficiary and frontline experience should become part of the evidence base by default rather than by exception. Most federal programs already have reporting infrastructure, and layering in a modest set of customer-first indicators that use the existing infrastructure rather than building new information collection requirements ensures that user perspectives are consistently available as routine inputs.
Within the federal government, the customer experience and life experience work coordinated through OMB and performance.gov has demonstrated that lived experience can be collected and used at scale within existing authorities, which can be considered a foundation to build from rather than reinvent. At the state level,Minnesota’s Story Collective, housed within Minnesota Management and Budget (MN MMB), pairs administrative and performance data with qualitative, lived-experience narratives to give decision-makers a richer view of what their programs are actually producing.
These recommendations also address a common weakness in the federal system: evidence and performance information sit within the same broad ecosystem but move at different speeds, use different tools, and often reach different audiences. This is all the more reason to create a translation layer that can synthesize across them. Agencies need staff and routines that can connect evaluation, administrative data, performance indicators, qualitative input, and implementation realities into decision-relevant guidance. Without that connective tissue, agencies are left with parallel streams of information that don’t consistently converge at the point where action occurs.
Conclusion
The federal government already generates a great deal of information about what it’s doing and how it’s performing, but information isn’t the same as learning, and learning isn’t the same as adaptation. The gap between them is where the “so what” goes unanswered, and where the federal feedback loop breaks down.
Closing these loops doesn’t require new infrastructure or authority. It requires three shifts in how the existing system is used: designating knowledge brokers to carry translation across the handoff from review to decision-making, building decision framing into policy and evaluation work from the start so that evidence is scoped to the decisions it’s meant to inform, and creating pathways that move mixed-methods and lived experience into decision-makers’ hands in formats and timeframes that match how decisions actually happen in the federal environment. Whether the question is about USDA responding to SNAP redetermination churn or the Department of Education learning from an application rollout in real time, the underlying pattern is the same: the signals exist, but the translation that turns signals into actionable insights doesn’t reliably happen.
If the government wants a system of learning and adaptation that improves results in real time, it has to treat translation, utilization, and adaptation as core functions of governance rather than as afterthoughts.
Outcome-Based Contracting Reorients Government IT Acquisition Around Public Value and Mission Results
The effectiveness of federal programs is increasingly determined by the technology that powers them. Yet decades of oversight and research have documented persistent challenges in large-scale IT modernization. The Government Accountability Office has repeatedly designated federal IT management as high risk, citing cost overruns, schedule delays, weak requirements management, and inadequate oversight. Bent Flyvbjerg’s research shows that large public-sector technology and infrastructure programs are especially prone to failure due to scope creep and cumulative risk. The Defense Innovation Board similarly concluded in Software Is Never Done that long development cycles and early requirement lock-in expose missions to unacceptable risk.
Across these analyses, the pattern is consistent: requirements are defined too early and too rigidly; performance is measured too late; incentives reward milestone completion rather than operational outcomes; and risk accumulates until deployment. These failures reflect several structural challenges—fragmented funding, leadership turnover, legacy system complexity, and acquisition models that delay validation and limit adaptation.
Traditional acquisition approaches assume stable requirements and predictable environments. Software-intensive systems do not behave this way. Requirements evolve, dependencies emerge during implementation, and technology ecosystems shift over the life of the contract. In this context, specification-driven models can increase risk by delaying feedback and limiting course correction.
This paper examines Outcome-Based Contracting (OBC) as a model for aligning acquisition with the realities of modern IT delivery. OBC reframes procurement around the staged achievement of measurable mission outcomes rather than the delivery of predefined technical artifacts. OBC ties funding, evaluation, and continuation decisions to mission outcomes and pairs naturally with iterative delivery practices that surface and reduce risk early.
Outcome-Based Contracting
Federal acquisition models have evolved over time in response to changing technologies and risks. Early approaches emphasized detailed specification and cost control, with contracts structured around defined requirements and reimbursement of inputs (e.g., cost-plus and fixed-price models). As systems grew more complex, performance-based contracting emerged to shift focus from activities to measurable outputs and service levels. However, in complex and dynamic environments, even performance-based models often remain tied to predefined deliverables and intermediate metrics, limiting their ability to adapt as conditions, requirements, and understanding evolve over time.
Outcome-based contracting (OBC) represents a further evolution. It structures the government–contractor relationship around shared accountability for mission results rather than delivery of predefined outputs. Its defining feature is not a pricing model, but the alignment of incentives, governance, and performance measurement around measurable mission outcomes.
As Allan Burman notes, building on performance-based contracting, OBC shifts accountability from activities and milestones to mission outcomes. In practice, it establishes a structured process in which government and contractor jointly deliver measurable results, with contracts defining decision rights, evaluation mechanisms, and adaptive processes.
Key features include:
- Shared accountability: success is defined in operational terms, not artifact delivery
- Collaborative outcome definition: the government defines the problem to be solved, contractors propose and refine approaches as evidence emerges
- Adaptive performance management: metrics guide decisions, not just compliance
- Joint problem solving: governance supports rapid adjustment when performance diverges
A useful way to understand outcome-based contracting is as a managed performance relationship rather than a one-time procurement transaction. As research from the IBM Center for The Business of Government emphasizes, effective outcome-based models require clearly defined desired results, measurable indicators of success, and ongoing performance management processes that allow both parties to assess progress and adjust course. This includes establishing baseline performance, continuously monitoring results, and linking financial incentives, contract options, and governance decisions to demonstrated improvement. Critically, these models depend on sustained collaboration and transparency: agencies must be able to interpret performance data and engage in joint problem-solving with vendors, rather than relying solely on compliance reviews. In this sense, OBC is not simply a different way to write requirements—it is a different way to manage delivery, in which measurement, incentives, and decision-making are continuously aligned to achieving mission outcomes.
Applying Outcome-Based Contracting to IT Modernization
Applying OBC to IT modernization requires three shifts: defining measurable outcomes, structuring decision rights, and organizing contracts around incremental delivery.
Defining outcomes
Mission objectives must be translated into measurable operational indicators—such as transaction completion rates, time to resolution, system availability, or error reduction. These indicators must be precise enough for evaluation while reflecting real-world service performance.
Effective models distinguish between:
- Mission-level outcomes (stable): e.g., reducing time to receive benefits
- Implementation metrics (adaptive): e.g., response times or interim system thresholds
For example, a call center contract might set a mission outcome of reducing resolution time by 30 percent, supported by metrics such as speed of answer, first-contact resolution, and callback completion time.
A central design question is how outcomes are embedded in the contract. Outcomes can function as binding accountability anchors, linked to evaluation, incentives, and option decisions, but not as rigid end-states. This approach is only effective when supported by governance structures that allow agencies to interpret performance and adjust delivery.
Critically, outcomes and the underlying problem definition must be treated as testable and subject to refinement. Initial problem framing is often incomplete in complex systems. Contracts and governance models should therefore include regular check-ins, using data, user research, and operational feedback to assess whether the problem is being solved as intended. Where necessary, agencies and vendors must be jointly empowered to restate or refine the problem to ensure continued alignment with mission needs.
Structuring decision rights
OBC requires clear decision making authority over priorities and tradeoffs. In software delivery, this centers on a strong government Product Owner (PO) role. The PO is responsible for backlog prioritization, acceptance criteria, and aligning delivery with mission outcomes. The PO must be empowered to continuously adjust priorities based on user needs and performance data without requiring contract modifications. Contractors are accountable for delivering measurable progress, but do not control mission priorities.
Governance must reflect agency maturity, and also the nature of the initiative. More mature organizations can rely on PO-driven execution and adaptive metrics, using contract outcomes as high-level anchors. Even in less mature agencies, OBC principles can be applied in targeted ways—particularly in user-facing systems or components where outcomes can be clearly measured. In some cases, especially large enterprise system implementations, hybrid approaches may be required. These may combine clearly defined objectives and outcome metrics with more structured implementation phases for core platform rollout. The key is not strict adherence to a single methodology, but aligning decision rights, outcomes, and delivery approach to the realities of the system being implemented.
Structuring incremental delivery
Contracts must support incremental, evidence-based delivery. Large, multi-year programs defer risk discovery until late in the lifecycle. Iterative delivery reduces this risk by shortening feedback loops: capabilities are deployed incrementally, evaluated under real conditions, and adjusted early. Incremental delivery provides disciplined mechanisms for iteratively paying down risk.
OBC complements this model by tying funding and continuation decisions to demonstrated performance. Agile practices surface risk; OBC aligns accountability and resources to its mitigation.
This has direct implications for funding models. Effective OBC implementations require upfront decisions about how much funding is allocated to a product or service, with mechanisms to adjust that funding over time based on performance. Budgeting should support iterative scaling—expanding or contracting investment based on whether outcomes are being achieved. This, in turn, requires financial flexibility, such as capability-based budgeting, and the ability to reallocate funds or leverage working capital-like mechanisms.
In practice, appropriations constraints can limit this flexibility. For example, agencies operating under single-year appropriations may struggle to dynamically adjust funding in response to performance signals. Addressing this requires coordination between acquisition, product, and financial management functions to ensure that funding structures align with the adaptive nature of outcome-based delivery.
Outcome-Based Contracting In Practice
Outcomes-oriented approaches are not new but remain underutilized in IT acquisition. Existing models demonstrate the value of aligning funding to measurable performance.
Within government, the Department of the Navy’s World Class Alignment Metrics (WAM) evaluates IT investments based on outcomes such as resilience, customer satisfaction, and cost per user. Similarly, Department of Defense Performance-Based Logistics ties compensation to readiness outcomes, and NASA’s Commercial Crew program links payments to demonstrated capability.
These examples share a core principle: funding follows validated performance rather than predefined inputs. Applied to IT modernization, this requires pairing mission outcomes with iterative delivery, clear decision rights, and sustained technical engagement. Without these elements, outcomes risk becoming abstract goals rather than operational tools.
Despite its advantages, outcome-based contracting is not the default in federal IT acquisition. In practice, existing incentives continue to favor specification-driven models: funding structures are rigid, oversight emphasizes compliance with predefined requirements, and procurement processes reward detailed up-front definition over adaptive execution. The following case illustrates how these dynamics shape real-world outcomes—and how leadership, governance, and delivery choices ultimately determine whether programs succeed or fail.
Case Study: SSA Call Center Modernization
The Social Security Administration (SSA) operates one of the largest public-facing service platforms in the federal government, serving approximately 70 million Americans through its national 800-number network and field offices, processing high volumes of calls. In 2017, the SSA faced growing problems with its aging, complex telephone infrastructure and rising wait times for the tens of millions of Americans who rely on the agency’s national 800-number for assistance with benefits, Social Security numbers, and other services. To address these issues, SSA launched the Next Generation Telephony Project (NGTP), a large IT modernization effort intended to replace legacy telephone systems and unify call handling across the agency.
NGTP emerged from a traditional acquisition model: a detailed, waterfall-style specification, a large systems-integrator contract, and milestone-based progress tied to predefined technical requirements. In February 2020 SSA awarded an IDIQ contract to Verizon to design, implement, test, transition, operate, and maintain the new telephony platform, including procurement of hardware, software, and services. Implementation faced challenges from the beginning: Verizon’s win was contested, delaying the start of work. SSA’s team didn’t realize the solution Verizon proposed, reinforced by SSA’s own contract requirements, was based on architectural components that were a generation behind leading contact center systems. NGTP’s 10-year planning horizon meant any solution would likely be obsolete before full deployment.
By 2020, with the project still in early development, the COVID-19 pandemic forced SSA call center agents to work remotely — a capability the existing legacy system lacked. Verizon scrambled to assemble a custom stopgap solution, but this was plagued with issues. From May 2021 to December 2022, over 40 service disruptions caused dropped calls, long wait times, and outages. At times, more than half of calls went unanswered as the team capped incoming calls to maintain system stability.
Meanwhile, NGTP suffered further delays and technical hurdles. SSA executives were frustrated but assumed they were contractually stuck. The system finally launched in December 2023 for the 800-number only, delivering just part of the promised functionality. But the system experienced ongoing performance issues, including increased wait times and disconnected or unanswered calls that hindered the agency’s ability to serve the public. On August 22, 2024, after only about 10 months of operation, SSA transitioned the 800-Number Network off the NGTP platform and moved to a different telephony solution. The NGTP project cost SSA over $160 million and was abandoned within a year of deployment, with the agency reverting to an alternative telephony platform.
The failure was not attributable to a single cause. Interviews and oversight findings point instead to a combination of over-specification, missing mission outcomes, weak accountability mechanisms, long planning horizons, and an acquisition structure that made adaptation difficult.
It is also important to recognize the scale and complexity of SSA’s operating environment. The agency’s service delivery depends on hundreds of interdependent systems, many of which encode decades of policy and operational logic. Modernization efforts must contend not only with outdated technology, but with deeply embedded business rules and integration dependencies that are not always fully visible at the outset. These conditions increase the difficulty of both specification and implementation, regardless of acquisition approach.
Specificity Did Not Produce Control
A central lesson of NGTP is that specificity in requirements does not necessarily translate into control over outcomes. The solicitation and technical requirements were extensive and highly prescriptive. They incorporated staff input but lacked sustained user-centered validation and focused heavily on defining technical components rather than the operational outcomes the system was intended to achieve. In several cases, the contract mandated architectural approaches that constrained flexibility and effectively locked the program into solutions already lagging prevailing commercial practice.
The NGTP contract required the development of significant custom telephony capabilities in a market where mature commercial Contact-Center-as-a-Service (CCaaS) platforms already existed. Custom software and hardware development inherently carries greater risk than configuring established commercial platforms: the first buyer bears the cost of defects, scaling problems, and design errors that mature products have already identified and resolved. As a result, the program assumed substantial technical risk without clear evidence that SSA’s mission required a bespoke system.
The decision to pursue a custom telephony architecture also introduced structural technical risks. The system was intended to function as a “single enterprise contact center” capable of routing calls across SSA’s national network. In practice, however, the implemented solution consisted of six separate contact centers operating as independent queues rather than a unified system. According to the SSA Office of Inspector General, this configuration prevented calls from being dynamically rerouted between queues, limited agents to answering calls from a single queue, and could disconnect calls when agents logged out of one queue even if capacity existed elsewhere in the system. These limitations increased wait times and created operational inefficiencies. Efforts to resolve the architectural mismatch led to the development of a custom routing “brain” intended to connect the six queues—effectively reinventing load-balancing technologies that have been widely used and commercially mature for decades. The need to retrofit this architecture required multiple contract modifications and created ongoing operational challenges. As one SSA leader later observed, “Some people on the project might have known that load balancers had been mature for 30 years, but managers weren’t listening to them.”
The contract’s prescriptive structure also undermined the flexibility typically associated with its contract vehicle. Although NGTP was structured as an IDIQ, the narrowly defined solution space meant that many necessary adjustments required formal work orders or contract modifications. In practice, the program combined the administrative rigidity of traditional contracting with the technical risk of custom system development.
The detailed specifications locked the implementation into many types of outdated architectural assumptions. For example, certain components were required to be compatible with an old, yet unspecified, version of Internet Explorer, a browser Microsoft formally retired in 2022 in favor of Microsoft Edge. Rapidly evolving technology environments can render highly specific requirements obsolete before systems are delivered. At the same time, the extensive technical detail did not fully address practical operational considerations, such as ensuring that existing SSA call center staff could easily access and use the system in their day-to-day workflows.
Missing Mission Outcomes
The NGTP case also illustrates the limits of operator-focused metrics. SSA understandably focused on call volume and the ability of the system to handle surges in demand. Previous infrastructure could “top out” during predictable spikes, such as cost-of-living adjustment periods. Capacity therefore became a central concern.
But throughput alone is not the same as service performance. For beneficiaries, the meaningful outcomes include how long it takes to reach a representative, whether the issue is resolved on the first contact, how many interactions are required, and how long it takes to complete a request. Those mission outcomes were not adequately embedded in the contract’s performance framework.
Metrics such as average speed of answer did not fully capture the user experience, particularly when calls were dropped, or handled initially by automated systems, or callbacks were counted in ways that reduced reported wait times without necessarily reducing the time required for beneficiaries to obtain help.
The deeper problem was architectural as well as contractual. SSA’s call center is best understood as a front-end interface to a much larger, deeply complex service delivery system involving eligibility determination, identity verification, claims processing, and payments. Yet the contract largely treated telephony modernization as a standalone technical problem rather than as part of an integrated operating model. This narrow framing also limited foresight into how the capability could evolve over time, adopting future emerging technologies or adding integrations with other agency systems to support an omnichannel service model. Defined primarily within a technical infrastructure context, the effort optimized for telephony components rather than positioning customer service as a strategic, cross-agency capability.
Accountability Was Weak Where It Mattered Most
Federal acquisition frameworks already provide multiple mechanisms for vendor accountability, including service level agreements (SLAs), financial incentives and penalties, option periods tied to demonstrated progress, and formal performance reviews. In the private sector, large IT and service contracts routinely embed such operational standards like uptime guarantees, response-time thresholds, incident-resolution timelines, and financial penalties for failure to meet them to ensure that vendors remain accountable for system performance under real operating conditions. In the NGTP case, however, these mechanisms were not sufficiently embedded in the contract structure or tied to mission outcomes and enforceable operational standards.
The SSA Office of Inspector General found that the NGTP contract lacked sufficient performance-based quality standards and incentives to ensure accountability for resolving system-performance issues. The practical result was limited leverage for the government even when the system failed to meet technical and operational needs.
The most striking example came at termination. When SSA stopped work on the NGTP effort, the agency still paid the vendor the remaining portion of the full $125M contract amount. Whatever the legal and operational considerations behind that decision, the message to the market was problematic: poor performance did not produce a proportionate financial consequence.
SSA’s Course Correction
SSA’s response illustrates an alternative approach. Rather than pursuing another large, fully specified replacement effort, the agency adopted a more incremental approach using cloud-native technology and more flexible contract mechanisms. A proof-of-concept deployment of Amazon Connect at a Pennsylvania call center allowed SSA to test the platform in live operating conditions before scaling further.
This approach introduced several disciplines that had been missing from NGTP. It reduced dependence on bespoke infrastructure, created an opportunity to measure performance under real conditions, and allowed the agency to collect operational evidence before broader rollout. Critically, assumptions were tested incrementally rather than embedded upfront. The agency also adopted Product Operating Model best practices: they stood up a cross-functional product team with a product manager, technical lead, design lead, and an SME lead who was responsible for state specific launches, training, and key metrics.
Early results suggested improvement. SSA’s Office of Inspector General reported that the agency’s telephone service handled substantially more callers in fiscal year 2025 and that reported average speed of answer improved. The subsequent administration leveraged the scalable platform to expand deployment across all field offices. At the same time, oversight and public reporting also highlighted the importance of careful metric design. Some reported gains did not fully reflect the total time beneficiaries waited for callbacks or to resolve their issues. That distinction is key: better performance frameworks depend not simply on more metrics, but on the right metrics.
Lessons for Outcome-Based Acquisition
The SSA case highlights several lessons:
- Complex systems cannot be fully specified in advance. Over-specification increases risk, and can lock programs into the wrong solution.
- Iterative delivery is a risk management tool. It surfaces integration, usability, security, and performance problems early enough to address them.
- Accountability must be tied to mission outcomes. Operational and customer experience results matter more than intermediate artifacts.
Governance matters as much as contract structure. Strong product ownership and leadership are essential. Critical to the successful turnaround was having a cross-functional “product quad” of product management, engineering, design, and domain expertise. In the NGTP case, requirements were largely defined within an infrastructure-oriented telecommunications function, leading to a solution optimized for technical components rather than end-to-end service outcomes. This organizational starting point constrained problem framing and limited the program’s ability to align delivery with user needs and mission performance.
An outcome-based model would have defined mission metrics such as first-contact resolution and total time to complete transactions, incorporated discovery phases, and tied continuation decisions to demonstrated performance. It also would have created a precedent for early adoption of critical monitoring tools used by leaders in the course correction, like integrating real-time customer experience telemetry into daily operations, which enabled continuous monitoring of user outcomes and rapid reprioritization of features to address emerging issues as they occur.
Finally, contract structure alone is not sufficient. Successful implementation depends on sustained leadership, technical judgment, and the institutional willingness to act on evidence. Several interviewees noted that meaningful progress accelerated only after leadership with prior agile and product delivery experience assumed responsibility for the effort. Acquisition structure can enable better outcomes, but it cannot substitute for leadership capable of making informed technical and operational decisions in complex environments.
Conclusion
Large-scale IT modernization is central to federal mission delivery. Traditional acquisition models remain effective in stable, well-defined environments but are poorly matched to software-intensive systems characterized by uncertainty, interdependence, and continuous change.
Outcome-based contracting provides a more effective framework for these conditions. It strengthens accountability by tying funding and continuation decisions to measurable performance, improves risk management through iterative delivery, and reorients acquisition toward public value. Rather than asking whether a contractor delivered what was specified, it asks whether the government achieved the mission results it needed.
Realizing this shift requires more than changes to contract structure. The authorities to pursue outcome-based approaches largely already exist, but incentives, funding constraints, and workforce capabilities continue to reinforce specification-driven models. Appropriations structures limit flexibility, oversight mechanisms emphasize compliance over performance, and many agencies lack the product management and data capabilities needed to define and act on outcome metrics. Addressing these constraints will require coordinated changes across budgeting, oversight, acquisition practice, and workforce development.
In the near term, IT modernization progress should be visible in concrete ways: contracts that tie option decisions and incentives to mission outcomes; programs operating with empowered Product Owners and real-time performance data; and evaluation frameworks that prioritize whether services are improving, not just whether requirements were met. Over time, this would mark a broader shift from managing compliance with plans to managing performance against outcomes.For technology and IT modernization efforts, the success of outcome-based contracting depends on alignment with product operating model practices, technical expertise, and sustained leadership. The central proposition of OBC is not less discipline, but better discipline—organized around measurable outcomes, empirical evidence, and the continuous identification and reduction of technical and operational risk.
Who Governs Government AI? The Challenge of Federal Implementation
Public Trust and the Stakes of Federal AI Regulation
Americans are skeptical that their government can regulate artificial intelligence. A Pew Research Center study from October 2025 found that while large majorities in countries like India (89%), Indonesia (74%), and Israel (72%) trust their governments to regulate AI effectively, only 44% of Americans say the same, and a greater number, 47%, express distrust. Globally, more people trust the European Union (53%) to regulate AI than the United States (37%). Americans will only realize the benefits of AI if they have confidence that these systems are used safely, fairly, and in ways that improve their lives.
Trust is not a soft concern: it is the foundation for the adoption, legitimacy, and long-term success of any technology. When people doubt that AI systems are governed responsibly, they are less likely to accept their use in sensitive domains like healthcare, education, public benefits, or national security. Public skepticism can slow innovation, undermine compliance, and deepen polarization around emerging technologies. Encouragingly, this is not a partisan issue. Republicans and Democrats alike have emphasized that trustworthy AI use is a prerequisite for public adoption and lasting legitimacy. If the U.S. is going all-in on AI, then building and maintaining that trust is therefore not simply a communications challenge; it is a governance imperative.
The federal government plays a starring role in meeting that imperative—not only as a regulator, but also as a model user of AI. It deploys some of the most consequential and high-risk AI systems, including those that shape access to benefits, guide law enforcement priorities, manage immigration processes, and support national security decisions. The federal approach to deploying these systems does more than affect service delivery or cost savings; it sets expectations for industry standards, academic research, and public perception of the technology. In effect, the federal government serves as a societal-level proving ground for AI governance. Because it uses AI in high-risk contexts, it must demonstrate that these systems can be governed effectively through transparency, oversight, accountability, and meaningful safeguards. Failure to do so would not only diminish confidence in AI as an economic and societal asset, but weaken the already tenuous trust the public has in government as a manager of risk and opportunity
Two use cases illustrate this point. One existing high-potential but high-risk application is the Veteran’s Administration’s (VA) REACH VET program, which uses predictive models to identify veterans at elevated suicide risk so clinicians can proactively reach out. Because it draws on health records and includes explicit race coding, one would be concerned about opaque modeling choices and the possibility of inequitable or incorrect flags. The stakes are high. If veterans feel that an algorithm is driving interventions without clear transparency, clinical guardrails, and accountability or if it misses potential intervention needs, trust can erode, not only in REACH VET but in the VA’s broader use of AI, and its mental health screening and treatment programs.
Planned uses of AI in the current administration are also concerning. CMS’s planned Medicare WISeR Model would test whether “enhanced technologies,” including AI, can “expedite the prior authorization processes for select items and services that have been identified as particularly vulnerable to fraud, waste, and abuse, or inappropriate use.” In practice, this could result in automated systems delaying or denying coverage for medically necessary prescriptions or treatments if a model incorrectly flags them as suspicious. The trust risk is immediate: prior authorization already feels like a barrier to care, and adding AI without appropriate guardrails or adjudication can make delays or denials seem more automated, less explainable, and more complicated to challenge, especially for older or medically complex beneficiaries. If people perceive AI as prioritizing cost control over care, it will quickly undermine confidence in Medicare and in government AI more broadly.
These two use cases show how setting parameters around federal AI governance is not an abstract compliance exercise; it directly shapes whether people experience AI as a helpful tool or as an unaccountable gatekeeper in some of the most sensitive and consequential interactions they have with the government. Federal guidance on incorporating elements like risk assessments, inventory documentation, and recourse processes into agency deployment play an outsized role in fomenting trust in government use of AI.
Attempting to meet this challenge, both the Biden and Trump administrations have issued major federal guidance on how agencies should govern their use of AI. In 2024, the Biden administration’s Office of Management and Budget released OMB Memorandum M-24-10: Advancing Governance, Innovation, and Risk Management for Agency Use of Artificial Intelligence as part of their role in establishing how federal agencies operate and implement government-wide regulations. This memorandum set forth a government-wide framework for the responsible use of AI, including requirements for risk assessments, transparency, safeguards for high-impact systems, and clear waiver processes. However, we previously found that the growing body of AI-specific guidance, layered on top of existing procurement rules such as the Federal Acquisition Regulation (FAR), can be difficult for agencies and vendors to navigate, particularly when determining at what stage in the acquisition process risk and impact assessments should occur.
Last year, the Trump Administration’s OMB superseded OMB M-24-10 with new guidance: M-25-21: Accelerating Federal Use of AI through Innovation, Governance, and Public Trust. This memo includes elements similar to the Biden administration guidance but, because of its more flexible, agency-driven model, also makes consistent implementation more challenging. The shift toward greater agency discretion could be explained by the Administration’s emphasis on accelerating AI adoption and reducing centralized compliance requirements that could slow experimentation or deployment. Agencies now shoulder greater responsibility for building their own governance and compliance structures, a task that depends heavily on available resources and technical capacity. Well-funded agencies may be positioned to meet these expectations, while smaller or resource-constrained agencies, including those whose tools have the greatest impact on low-income or marginalized communities, may struggle to develop and implement the same safeguards. The result is a growing risk of fragmented governance across the federal landscape, with uneven protections for the people most affected by AI systems.
With this context in mind, it’s worth examining how each administration has approached the challenge of governing high-risk AI, and what these differences mean for agency accountability and public trust.
From “Rights- and Safety-Impacting” to “High-Impact”: A Change in Orientation
AI Risk Thresholds
OMB Guidance M-24-10, issued under the Biden administration, established a government-wide framework for identifying and managing artificial intelligence systems that pose elevated risks to rights or safety. The memo introduced two formal designations: “rights-impacting AI” and “safety-impacting AI.” Rights-impacting systems are those whose outputs serve as a principal basis for decisions or actions with legally significant effects on individuals’ civil rights, liberties, privacy, or equitable access to services such as housing, education, credit, or employment. Safety-impacting systems are those whose decisions or actions have the potential to significantly affect human life or well-being, the environment, critical infrastructure, or national and strategic assets.
Under the Trump administration, OMB M-25-21 replaced the dual “rights-impacting” and “safety-impacting” categories with a single unified definition of “high-impact AI.” This term covers any AI system whose “output serves as a principal basis for a decision or action that has legal, material, binding, or similarly significant effects on individuals or entities.” Examples still include systems affecting civil rights, access to government programs or resources, health and safety, critical infrastructure, or other vital assets. While the framework remains centered on AI systems that serve as a principal basis for consequential decisions, the new memo consolidates the prior rights- and safety-based categories into a single, more generalized standard.
This shift is not merely semantic. The way OMB defines high-risk or high-impact AI determines which federal agencies must apply heightened safeguards, conduct impact assessments, and implement specific oversight and accountability measures. It also signals to contractors, state and local governments, and private-sector partners the types of AI use that warrant the most stringent governance practices. As discussed below, consolidating the categories may affect the scope, clarity, and structure of minimum risk-mitigation requirements across agencies.
Minimum Risk Management Practices
Reaching a designated risk threshold, whether categorized as “rights- or safety-impacting” under the Biden administration or “high-impact” under the Trump Administration, does not bar an AI system from being used in government. Instead, both administrations require agencies to meet a set of minimum risk management practices before deploying such systems. These requirements, summarized in the table below, establish the baseline safeguards for high-risk AI use.
While there are consistent practices among both guidance documents, including AI impact assessments, ongoing monitoring and evaluation, and workforce training, there are a few elements noticeably absent from the Trump administration’s M-25-21. For example, the new guidance does not have opt-out considerations, has a looser procedure for remedies of high impact systems, and does not go into as much detail on what ongoing risk monitoring should look like. Independent review in the Biden administration formalized the inclusion of the Chief AI Officer (CAIO) or another agency advisory board, while the Trump administration has more flexibility in who can review high-impact use cases.
The Trump administration also differs in including a new element: pilot projects. These pilot AI programs are exempt from full risk-management requirements if they are limited in scale and duration, approved and centrally tracked by the agency’s Chief AI Officer, allow participants to opt in or out with proper notice when possible, and still apply risk-management practices wherever practicable.
Waivers
If, for whatever reason, agencies decide to not undergo the aforementioned minimum practices, both guidance documents offer waivers that give the agency’s CAIO authority to supersede a minimum risk practice. These waivers are centrally tracked and reported to OMB.
Whereas the Biden administration portrayed this as a procedural element, M-25-21 shifts the tone and purpose of these waivers. Under this system, an agency’s CAIO, in coordination with relevant officials, can grant a waiver from one or more of the minimum practices whenever strict compliance would impede mission-critical operations or increase overall risk. The memo explicitly allows waivers when compliance might “create an unacceptable impediment” to agency objectives, a broader, more permissive standard than under Biden.
By introducing a flexible pilot program model and more permissive and vague language risk management practices, the framework places substantial discretion in the hands of agencies and their CAIOs. In practice, agencies will exercise this discretion unevenly because they vary widely in governance maturity, technical capacity, and oversight infrastructure, an issue discussed in more detail below. These disparities are compounded by differences in how CAIO roles are structured across agencies: some CAIOs are career officials with dedicated staff and technical expertise, while others serve in an acting or dual-hatted capacity, combining AI oversight with unrelated portfolios and limited institutional support. The absence of uniform qualification requirements or minimum resource standards further increases the likelihood that implementation will diverge significantly across agencies.
Agency Snapshots: A Disjointed Compliance Landscape
Federal AI governance operates at two distinct levels: (1) centralized policy direction issued by OMB, and (2) agency-level compliance processes that operationalizes those policies. While policy sets uniform expectations, compliance is implemented through agency-specific procedures shaped by capacity, mission, and internal governance maturity. The interaction between these layers determines whether federal AI governance appears coherent or fragmented.
Under Trump’s OMB Memorandum M-25-21, every federal agency is required to publish both an AI Strategy and an AI Compliance Plan outlining how it will govern its high-impact AI systems and manage its waiver processes. The majority of these plans were published in September and October 2025. The following agencies provide a useful snapshot of how different parts of the government are approaching compliance with this guidance.
It is appropriate for agencies to develop risk evaluation approaches that reflect their distinct missions and deployment contexts. Sector-specific risks vary enormously: the harms posed by clinical decision-support tools differ from those associated with benefits administration, law enforcement, or worker-protection considerations. Agencies need the flexibility to evaluate risks within their own operational contexts.
However, differences in the content of sectoral risks and differences in the processes agencies use to manage those risks are not the same thing. Allowing agencies wide latitude in interpreting minimum risk management practices and in designing their waiver procedures creates the possibility of procedural divergence, not just divergence in substantive sector-specific requirements.This is where inconsistency becomes a governance problem, not just a technical one.
Agencies have long struggled to apply their own policies consistently across programs and time. A 2023 study of Biden-era AI governance practices found that fewer than 40 percent of mandated actions under key federal AI authorities were verifiably implemented, and that nearly half of federal agencies failed to publish required AI use-case inventories despite demonstrable use of machine-learning systems. Although the Trump administration may grant more discretion in agency AI governance, we see that the ability to consistently apply guidance is a structural issue that spans administrations. Without a baseline of procedural consistency, OMB may struggle in its mission to oversee these compliance plans.
The Importance of State Capacity
When each agency is left to design its own compliance architecture, implementation will also inevitably diverge according to capacity rather than mission need. This will produce a fragmented governance landscape that closely resembles the “patchwork” often cited as a concern in broader AI regulatory debates. Some agencies have already demonstrated the ability to produce relatively robust internal guidance because they possess deeper technical benches, established governance bodies, and more mature risk assessment processes. As shown in Table 2, for example, DHS has established centralized AI governance structures, published detailed AI inventories and use-case documentation, and built out internal review mechanisms to assess high-risk systems. Similarly, the DoL has developed agency-wide AI plans and formal oversight processes that integrate risk assessment, transparency, and workforce training components. But smaller, under-resourced agencies, such as the Court Services and Offender Supervision Agency (CSOSA) references in Table 1, may struggle even to stand up the foundational processes needed to comply with M-25-21.
At the core of this capacity gap is a workforce challenge. Effective AI governance depends not only on the right guidance but also on sufficient and well-deployed talent. This includes AI talent – staff with expertise in machine learning, data science, and model evaluation, and AI-enabling talent, which includes product managers, procurement specialists, privacy and civil liberties experts, domain specialists, and program managers who can integrate understanding of technical systems into real-world decisions and operations. AI governance bodies, risk assessment frameworks, and waiver adjudication processes cannot function without personnel who understand the technology and the agency’s mission context, and who can manage and adapt agency learning and implementation systems over time. A single brilliant CAIO is a smart first step, but long term effectiveness relies on the agency’s ability to enable a “flywheel” of adaptation, growing AI and AI enabling capacity over time.
The Biden administration had an AI Talent Surge with the explicit focus on bringing in AI and AI-enabling talent into the federal government, and was able to bring at least 200 experts into public service while advising agencies on structure and capacity-building. While M-25-21 prompts agencies to develop and retain AI and AI-enabling talent, it’s unclear how that matches up with the fact that 317,000 federal workers have left the government in 2025. Because many of the Biden-era AI hires were still within their probationary period, therefore vulnerable to layoffs, and because some entire digital teams, such as GSA’s 18F and the DHS’ own AI Corps, were slashed, it is now difficult to determine where federal AI talent resides or how much of that capacity remains in government.
Recent Trump administration moves have recognized some of this gap, but the emphasis on early-career vs. institutional adaptation is limiting. Late last year, the Office of Personnel Management issued a “Building the AI Workforce of the Future” guidance document, with emphasis on the launched TechForce (hiring early-career technologists for limited terms of two years), Project Management and Data Science Fellows programs, and other early-career oriented programs.
Conclusion
The divergence between M-24-10 and M-25-21, coupled with the uneven compliance plans that have followed, reveal a federal AI governance landscape marked by structural fragmentation, one that carries real implications for public trust. Agencies with robust technical resources are positioned to comply with these requirements if they choose to, while others will struggle to keep pace. Compounding this disparity, the dissolution of digital teams and loss of probationary AI hires have obscured the government’s understanding of its AI workforce, weakening its capacity to implement trusted and transparent governance.
Ultimately, M-25-21’s compliance plans will not fulfill their intended purpose unless agencies receive the funding, staffing, and political support required to carry them out. A compliance plan is only as strong as the people and resources behind it. Robust, transparent governance is impossible without investments in the civil service capacity needed to implement it, and without such trust-building capacity, agencies risk forgoing the responsible adoption of AI systems that could improve public services and operational effectiveness.
A pre-mortem on OPM’s HR 2.0 initiative: Imagining failure in order to support success
[Editor’s note: full examination here (pdf)]
Large-scale IT modernization projects fail with remarkable regularity. They fail in private companies with strong profit incentives and unified leadership. They fail in state and local governments with narrower missions and simpler constraints. And they fail — often spectacularly — in the federal government. Entire multibillion‑dollar industries exist precisely because implementing large, complex software, including Enterprise Resource Planning (ERP) systems, is hard: technically complex, organizationally disruptive, politically fraught, and culturally destabilizing.
OPM’s new HR 2.0 initiative is therefore entering hostile terrain by default. The initiative aspires to rationalize, consolidate, and modernize a sprawling thicket of federal human resources systems that has grown organically over half a century. It seeks to replace dozens of agency‑specific solutions, hundreds of interfaces, and innumerable manual workarounds with a standardized, interoperable, enterprise‑wide platform capable of supporting modern workforce management.
Those of us who have followed federal HR modernization for years desperately want this effort to succeed. The current HR IT landscape is costly, brittle, opaque, insecure, and increasingly misaligned with how the federal government needs to recruit, manage, pay, and deploy its workforce. As OPM has documented and independent research shows, the federal government likely wastes billions of dollars maintaining hundreds of systems that slow agencies down, force them to duplicate effort, and obfuscate rather than clarify the data required to make business and workforce decisions. Some of these systems are decades old and have been assessed as a high risk to government operations if they should fail. Modernization is no longer optional. It is a prerequisite for addressing mission delivery, workforce planning, and public trust.
But optimism is not a plan, and aspiration is not execution. In our experience, the greatest danger to large federal IT programs is not a lack of good intentions, but rather a failure to fully internalize how hard it is to succeed and avoid the missteps of the past. In that spirit, this paper adopts an intentionally uncomfortable posture: It is a pre‑mortem. Rather than waiting until a future GAO report, Inspector General audit, or congressional hearing explains why this effort underperformed, we imagine that possible failure mode now.
We assume — purely for analytical purposes — that OPM’s HR 2.0 initiative did not achieve its intended outcomes. From that hypothetical vantage, we ask:
- What were the most likely failure modes that doomed the effort?
- What could OPM, OMB, Congress, and agencies have done earlier to materially reduce those risks?
- What questions should OMB and OPM leadership be asking today to avoid that outcome?
OPM, agencies, and OMB have already invested substantial time and energy in planning this effort. This paper is intended to complement — not undermine — that work by surfacing structural vulnerabilities early, when they can still be addressed. This, in turn, can help guide implementation teams’ focus today under the presumption that success, with care and forethought, is possible despite all the barriers.
HR 2.0 is a good idea, but it has risks
At its core, OPM’s initiative is a good one and addresses an often-neglected part of the federal business enterprise that has long needed attention from senior leadership. It is also perhaps the most ambitious attempt ever made to solve this problem once and for all. In fact, OPM has made a series of choices related to how it has structured the program — decisions that demonstrate the administration’s seriousness and commitment, and we mostly agree with the impulse and meaning behind each of them:
- Single award – Currently, several different vendors service the federal government, including Oracle, SAP, and Workday. This creates interoperability and data standards challenges, as upgrades need to be made in each proprietary code-base when policies or directions change. OPM’s approach in HR 2.0 solves this by mandating a move to one, single software company, which can tightly integrate the entire federal enterprise into a standard solution that is easier and cheaper to maintain.
- Direct contracting with software OEM – Historically, when agencies moved to new systems, they contracted with a large system integrator (SI) that served as something of a middleman between the agency and the company that actually built the software. These SIs served as translators between the two groups: business requirements from agency to vendor, technical specifications from vendor to agency. However, this creates additional cost and management complexity as the agency relies on a third party to act in its interests. OPM’s approach in HR 2.0 solves this by establishing a direct contracting relationship between OPM and the eventual software vendor so that OPM can control vendor behavior and changes to the underlying single code-base.
- Recoup costs from agencies – There are a variety of models for funding mandatory government-wide services, including both specific appropriations and also pooling funds from agencies to a central account. For HR 2.0, OPM appears to be electing the latter, which gives agencies “skin in the game” and ownership of the resulting solution: They’re paying for it, so they are true customers rather than simply takers of OPM’s direction.
- Explicit direction to agencies – There are various ways to drive adoption of single solutions. OPM and OMB have elected to pursue a top-down, mandatory, whole-of-government approach that establishes a schedule and mandates adoption. This solves many common collective-action problems across government: No agency wants to go first and everyone would prefer to push the timeline out as far as possible.
However, we also know how hard this is going to be, both because of our own experience working on this topic inside the federal government ,and because the government has failed at this exact exercise before. In fact, it has already failed at this project this decade.
Learning from DoD’s failure
In March of 2025, Secretary of Defense Pete Hegseth released a memo and then a video highlighting an effort to cut wasteful spending and putting several programs on hold. The first program on his list was the Defense Civilian Human Resources Management System, or DCHRMS (pronounced dee-charms in classic defense bureaucracy style).
The program had been “intended to streamline a significant portion of the Department’s legacy Human Resources (HR) information technology stack – an important mission we still need to achieve – but further investment in the DCHRMS project would be throwing more good taxpayer money after bad.” In his telling, the program was “780 percent over budget. We’re not doing that anymore.” It was over — the DoD had tried and spectacularly failed to move to a single HR system for just its own department. This high-profile bust is exactly what we mean when we say this type of HR IT modernization is hard and fails all the time.
The project originally started in 2018 as a $36 million, one-year proof of concept and then morphed into a years-long effort to consolidate at least six separate DoD systems based on Oracle’s E-Business Suite software onto a single, DoD-wide Oracle Cloud HCM platform. The project moved from proof of concept into full execution without a formal acquisition or rigorous planning, leaving the systems integrator that managed the legacy systems also in charge of implementing the new system. The department tried mightily to standardize business processes across DoD services. But people familiar with the project say that middle managers and subject-matter experts across the department added requirements that led to scope creep as the project wore on. As the project timeline began slipping, Oracle introduced new technologies and features that led to further slippage to incorporate them into the program baseline. By the time the program was cancelled, it was not clear what DoD’s measures of success were. That the integrator responsible for deploying the new system was simultaneously profiting from operating the legacy systems also presented an obvious conflict of interest.
The DCHRMS saga maps several pitfalls associated with large-scale enterprise IT modernization programs. The failure to maintain a rigorous convergence baseline and guard against scope creep is one. That seems to have been compounded by a business model and accountability structure that were not well thought through or did not adhere to best practices. And ultimately, by the time it became clear that the program was unable to deliver concrete, measurable outcomes in a reasonable and well-defined timeframe, the state of technology had evolved, rendering the program’s initial targets irrelevant and forcing the program to rebaseline.
These reasons for failure are not unique to DCHRMS, nor are they unforeseeable. In fact, they are some of the most common failure modes that doom complicated, multi\stakeholder technology implementations in complex organizations. Not even the DoD’s generally deferential-to-leadership and can-do culture could overcome them.
Predicting failure modes and mitigating the risks
For OMB and OPM to avoid this fate for HR 2.0, they need to consider the possibility of failure and take the risks of their approach head on. DCHRMS was a good idea, too, but good ideas only get you out of the gate and not over the finish line.
Based on our experience, we’ve imagine what the failure modes might be; suggest mitigations; and, crucially, articulate the questions leaders should be asking today to try to avoid failure in the future.
Failure mode 1: The single-award strategy backfires, or Industry doth protest too much
Scenario: In early 2026, GSA awarded the government-wide contract to implement HR 2.0 to a single vendor after a competitive evaluation,but the project quickly went the way of JEDI. Within weeks, two unsuccessful offerors — gigantic tech companies with deep pockets and nothing to lose — filed protests with GAO, arguing that the evaluation criteria unfairly favored the awardee’s architecture and that OPM had failed to adequately consider total cost of ownership. GAO sustained one protest on narrow technical grounds, requiring a reevaluation. That process took months, during which a third vendor protested, alleging the revised criteria were designed to reverse-engineer the original outcome. By the time the litigation resolved in late 2027, OPM had lost its original program leadership, the vendor’s proposed technical team had largely dispersed to other projects, and three agencies that had been preparing for early implementation had redirected their modernization budgets elsewhere.
The single-award approach isn’t inherently flawed, but it demands unusual discipline in execution and presents significant risks. OPM and GSA must assume protests are coming and prepare accordingly, both legally and programmatically. Their goal should be twofold: make protests less likely to succeed on their merits, and structure the program so that even a sustained protest doesn’t collapse momentum entirely. Here’s how:
- Build legitimacy through transparency. Proactively explain the award decision to appropriators, GAO, industry associations, and agency stakeholders. When policymakers and others understand and accept the rationale, vendors have less political cover for delay tactics. This will set the stage for effective vendor debriefs as well.
- Build innovation incentives directly into task orders. Normally, the federal government drives innovation in its vendor base through competition: Companies compete to offer the mix of capabilities relative to price and are incentivized to lower their work margins. In a single-award model, OPM loses some of this competitive pressure to innovate. As a result, rather than assuming innovation will emerge organically as a result of market forces, OPM should explicitly reward it. This could include incentive fees tied to measurable improvements in usability, automation, or data quality, as well as structured mechanisms for piloting and scaling new capabilities.
- Protect exit options. Require data portability in nonproprietary formats and government ownership of custom code. Real exit options, even if unlikely to be exercised, weaken the “lock-in/lock-out” narrative that makes protests attractive.
- Maintain the ecosystem. A curated marketplace for ancillary solutions (i.e., microsolutions outside the scope of the current contract) keeps competitive pressure alive and gives losing vendors a reason to stay engaged with the federal government rather than litigate over the loss of their entire market share.
Key questions for OPM and OMB leadership to ask: What is our realistic timeline and budget for protest and litigation? And have we structured the program so that a significant delay won’t collapse momentum entirely?
Failure mode 2: An OPM-led, OPM-managed effort becomes a bottleneck or Herding Cats Is too Hard
Scenario: By mid-2027, the program had a governance problem that no one wanted to name. OPM had established an impressive array of boards, councils, and working groups, but decisions that should have taken days were taking months. Agency requests for configuration changes sat in queues. Escalation paths were unclear. When disputes reached senior leadership, they often got sent back for “more analysis.” Agencies, meanwhile, learned that the fastest path to resolution was to route around OPM entirely: calling OMB, complaining to appropriators, or simply delaying participation until someone else went first.
Centralizing authority at OPM makes sense in theory: It’s the government’s HR agency, and fragmented leadership doomed earlier efforts. But centralization only works if OPM has the capacity to actually lead, and if governance structures enable decisions rather than defer them when agencies push back — and they will push back. This requires deliberate investment in both institutional capability and stakeholder engagement:
- Build capacity before you need it. OPM will need staff profiles it hasn’t historically employed at scale: senior IT program executives, enterprise architects, contracting specialists, and financial managers. Borrowing talent through detailees can help initially, but durable capability requires permanent investment and new types of positions.
- Design governance for speed. Establish clear decision rights, escalation paths, and timelines at every tier. Linked governance bodies must cover the full range of strategy, policy, contracting, operations, stakeholder engagement, and performance. They should have authority to resolve issues, not just discuss them. When decisions are kicked up the ladder, there should be a deadline for resolution.
- Develop model interagency agreements (IAAs). Standardized IAAs with explicit service levels, cost allocation, and dispute resolution will reduce the transaction costs that otherwise consume leadership attention.
- Make agencies partners, not passengers. Leverage the Chief Human Capital Officers (CHCO) Council not only as a communication channel, but also as a genuine forum for surfacing concerns and shaping implementation. Agencies need to see that their expertise matters, even when their preferred approaches don’t prevail.
- Treat HR 2.0 as a product, not as a project. HR 2.0’s success relies not simply on the implementation of a new IT system, but on the ongoing evolution of the features and functionalities that will enable the system to respond to and meet the needs of agency users. The private sector, and increasingly parts of the government, have adopted a “product operation model” to manage around these constraints. OPM should leverage the considerable experience its HR Solutions organization has with this model and mindset to adopt many of these management principles for HR 2.0.
Key questions for OPM and OMB leadership to ask: Does OPM have — or can it rapidly build — the programmatic capacity to manage a government-wide implementation? Or will it need to partner more deeply with other organizations to fill critical gaps?
Failure mode 3: Contracting directly with OEMs goes awry, or Integrators were integral after all
Scenario: The idea was novel: contract directly with the software company, make it accountable for delivery, and relegate the big integrators to supporting roles. However, what no one fully appreciated was that the OEM had never run a federal program at this scale. Its government practice was built around licensing, not implementation. When agencies reached out to them directly, staff struggled to handle their dual role as client navigator and enforcer of standards. Meanwhile, the integrator subcontractors had little incentive to go beyond its narrowly defined task orders; It had learned from experience that exceeding scope meant absorbing risk. By 2028, the program had developed a peculiar dysfunction: The OEM nominally owned delivery but lacked the expertise to drive it, while the integrators who had the expertise lacked the authority or incentive to deploy it. Problems that should have been resolved at the working level instead became triangular disputes among OPM, the OEM, and whichever integrator happened to be nearby when something broke.
Contracting directly with the OEM aligns authority with product knowledge, a real advantage when implementation challenges stem from product limitations. But OEMs are product companies, not delivery organizations. Making this model work requires treating the OEM relationship as a partnership to be developed, not a vendor to be managed, and designing governance structures that compensate for predictable gaps. Here’s how:
- Conduct rigorous OEM due diligence. Go beyond product maturity to assess delivery capacity, federal acquisition experience, subcontractor management capability, and organizational culture. How does the OEM handle failure? How does it resolve disputes? What’s its approach to managing agency customers?
- Design governance as a “team of teams.” The OEM should orchestrate, not micromanage. Agencies and their integrator partners need clear roles and enough autonomy to solve problems without constant escalation. Decision rights should be explicit and documented.
- Stress-test capacity assumptions. OEMs may underestimate what federal implementation requires: cleared staff, program management depth, constant stakeholder engagement. Validate their staffing plans and scaling assumptions before award, during early execution, and down the stretch to avoid foreseeable issues.
- Anticipate finger-pointing and design around it. Establish clear responsibility matrices distinguishing product issues from configuration or data issues. Create joint risk registers and escalation paths that prioritize resolution over blame.
- Maintain a curated marketplace for extensions. Even the best core system won’t cover everything. OPM and the OEM should jointly certify integrator-built solutions to ensure they align with enterprise standards without stifling innovation.
Key Questions for OPM and OMB leadership to ask: Has the OEM ever successfully delivered a program of comparable scale and complexity? And if not, what governance structures will compensate for that inexperience?
Failure Mode 4: Configuration management becomes unmanageable, or The Christmas tree collapses under its own weight”
Scenario: No one could point to the moment the baseline stopped being a baseline. It happened gradually, one exception at a time. An agency with a unique pay authority needed a configuration variant; that was legitimate. Another agency’s union agreement required a different leave-tracking workflow; that was unavoidable. A third agency wanted to preserve a legacy-report format that its budget office depended on; that was easier to accommodate than to fight. By 2028, the “standard” system had 17 major configuration branches, 42 approved extensions, and an uncounted number of agency-specific workflows that had been implemented as “temporary” accommodations. The vendor’s upgrade cycle, originally planned for quarterly releases, slipped to annual. Even then, each upgrade required months of regression testing across configuration variants to ensure that push of new commercial code didn’t break these customizations. The government had succeeded in replacing dozens of legacy systems with a single modern platform. Unfortunately, it also had recreated the fragmentation that modernization was supposed to eliminate.
Configuration pressure is inevitable. Federal HR is governed by multiple statutory regimes, and agencies will always have legitimate reasons for divergence. Some amount of tailoring is inevitable, but the major goal OPM should consider is how it might govern the solution so that exceptions remain exceptions rather than becoming the new normal. This requires treating configuration management as a strategic discipline, not an administrative afterthought. Here’s how:
- Define the baseline clearly and defend it. Establish explicit standard processes and hold agencies to them unless divergence is legally required. “We’ve always done it this way” is not a sufficient justification.
- Create a hierarchy of tailoring options. Not all customization is equal. Advanced configuration within the product is preferable to extensions; extensions are preferable to bolt-on integrations; core product modifications should be rare and require executive approval.
- Sequence for simplicity. Start implementation with smaller, less complex agencies to establish guardrails before tackling organizations with intricate labor agreements and statutory exceptions.
- Use funding as a governance lever. Agencies should pay for tailoring beyond the baseline but only after accepting and implementing the standard. This creates natural friction against unnecessary divergence.
- Make configuration decisions transparent. Publish what’s been approved, what’s been denied, and why. Transparency counters the belief, widespread in government, that “everything we do is special.”
- Align with civil service reform. Configuration complexity is downstream of policy complexity. OPM and OMB should work with Congress to explain how statutory exceptions drive cost and discourage future proliferation.
Key Questions for OPM and OMB leadership to ask: Who has the authority to say “no” to an agency’s configuration request> And will those with that authority get backup when politically powerful agencies push back?
Failure mode 5: Funding is insufficient, unreliable, or unsustainable, or The passed hat drops
Scenario: The funding model mapped to a usual format for government: Agencies would pay for their participation, OPM would recover costs through its revolving fund, and the program would be self-sustaining once it reached scale. What the model hadn’t accounted for was the messy reality of federal budgeting. Three agencies requested implementation funding in their FY 2027 submissions; two were denied by their appropriations subcommittees, who saw HR modernization as discretionary against more pressing mission needs. A fourth agency had funds but couldn’t obligate them in time because its IAA with OPM was still being negotiated. By 2028, the program’s wave schedule had been revised four times, each revision eroding vendor confidence that the government was serious. The OEM, facing uncertain volume, quietly raised its per-agency pricing to hedge against lower-than-expected adoption. Agencies that had been on the fence used the chaos as justification to wait. OPM found itself in the worst of all positions: accountable for a government-wide program but dependent on agencies it couldn’t compel and appropriators it couldn’t control.
In the federal government, budgets are political documents as much as they are management ones. The way money flows determines who has authority, who bears risk, and who ultimately decides what gets built. A distributed funding model may be administratively orthodox, but it diffuses accountability in ways that are toxic to enterprise modernization. OPM and OMB should treat the funding architecture as a strategic design decision, not an inherited constraint. Here’s how:
- Seek direct appropriations for implementation. Congress should appropriate funds to OPM specifically for the implementation phase, with a defined transition to a revolving fund model for operations and maintenance. This gives OPM real authority to enforce configuration discipline and control sequencing without having to beg, borrow and steal from across government.
- Partner early with OMB and appropriators. Don’t wait for the budget cycle to explain why traditional funding models are ill-suited to enterprise transformation. Build the case now for why centralized implementation funding produces better outcomes at lower long-term cost, and take advantage of the opportunity to explain how viewing this initiative through a product management lens implies the need for a different funding strategy.
- Impose transparency on revolving fund operations. If agencies will eventually pay through the revolving fund, they need clear visibility into what they’re paying for. Publish cost drivers, configuration decisions, and tradeoff rationales.
- Plan for multi-year commitment. Seek multi-year appropriations where feasible. They reduce annual renegotiation risk and signal to vendors, agencies, and oversight bodies that the government is serious.
- Use funding to enforce sequencing. Agencies that want to delay should understand that funding availability may not wait for them. Early participation should carry advantages; late entry should carry costs.
Key Questions for OPM and OMB leadership to ask: Can this program realistically achieve its objectives through distributed agency funding? Or does success require a level of centralized financial authority that OPM does not currently have, at least at the implementation phase?
Failure Mode 6: Agencies are not ready when their turn comes, or Agencies miss their marks
Scenario: OPM and the OEM did their parts. The contract was awarded, governance was established, and the wave schedule was published 18 months in advance. What no one had fully reckoned with was the state of agency readiness. The first wave included 4agencies, chosen for their manageable size and expressed enthusiasm. Two were genuinely prepared: Their data was clean, processes were documented, and change management was underway. The other two had overestimated their readiness. One discovered during configuration that its position data existed in three different systems that had never been reconciled; cleaning it would take nine months. The other had documented its “as-is” processes, but those documents described how the agency thought things worked rather than how they actually worked, a gap that surfaced only when end users began testing. OPM faced an uncomfortable choice: delay the wave, which would ripple across the entire schedule; lower quality standards, which would embed problems into the baseline; or push forward and absorb the pain.
Agency readiness isn’t just an agency problem, it is also a program problem. OPM can execute flawlessly on procurement, governance, and vendor management and still fail if agencies aren’t prepared when their turn comes. That means readiness requirements need to be specific, measurable, and consequential. Agencies have incentives to obfuscate their readiness until it’s too late if they don’t think you’re serious or don’t understand what you’re asking them to do. OPM needs a clear escalation path if agencies miss their marks. Here’s how:
- Define clear readiness thresholds. Agencies need specific targets—data quality metrics, process documentation standards, and change management milestones—not general encouragement to “prepare.” These thresholds should be published early and tied explicitly to wave eligibility.
- Assess readiness independently. Self-reported readiness is unreliable. OPM should establish assessment mechanisms—whether internal or third-party—to validate agency preparation before committing to implementation dates.
- Make sequencing flexible. Wave schedules should be benchmarked against readiness, with the explicit expectation that agencies can be swapped based on objective criteria. Agencies that are ready should move forward; agencies that aren’t should wait.
- Provide resources for preparation. Readiness work requires investment—staff time, contractor support, leadership attention. OPM should issue detailed preparation guidance immediately upon award and establish contract vehicles for data cleanup, process reengineering, and change management.
- Incentivize early engagement. Agencies with complex needs should be encouraged to participate in early planning, even if they won’t implement in early waves. Early involvement confers influence and builds the expertise that makes later implementation smoother.
Key questions for leadership: How will OPM distinguish among agencies that are genuinely ready and those that merely believe they are? And what happens when an agency in the latter category is scheduled for an early wave?
Failure mode 7: Executive sponsorship wanes over time, or Government takes its eye off the ball
Scenario: For the first two years of the term, the program had everything it needed: White House attention, OMB backing, an OPM Director with the right skills who made modernization a personal priority, and agency heads who understood they were expected to participate. Then, as happens in nearly every term, political appointees began to turn over. New appointees came in after the midterms with different priorities. The career staff who understood the program’s history remained, but their authority to make decisions — and their air cover when those decisions were contested — evaporated. Agency executives who had reluctantly committed to early waves found that their objections now received a more sympathetic hearing. By 2028, the program still existed: contracts were in place, some agencies had implemented, governance bodies still met. But the urgency was gone. Wave schedules slipped. The program had become one of many initiatives rather than the initiative. It would eventually deliver something — but not the enterprise transformation that had been promised.
Executive attention is a wasting asset. It cannot be sustained indefinitely through personal commitment alone: Eventually, leaders move on, priorities shift, and attention migrates to newer challenges. The only way to protect a multi-year, multiadministration program is to convert early momentum into durable structures that don’t depend on any single leader’s continued engagement, and embed support for this program in the career staff who will need to sustain it across agencies far into the future.
- Codify governance beyond individuals. Decision rights, escalation paths, and performance standards should be documented and institutionalized, not dependent on personal relationships or informal understandings.
- Build a permanent career backbone. Political leadership is transient; career leadership is not. Invest in a cadre of SES leaders at OPM and participating agencies who understand the program’s full arc and are empowered to sustain it across transitions.
- Secure bipartisan congressional support. Frame the initiative as state-capacity investment, not an administration priority. Active engagement with authorizers and appropriators across parties is essential; without it, the program becomes vulnerable to being labeled discretionary or ideological.
- Lock in early wins. Move quickly to establish durable artifacts — contracts, standards, migrated agencies — that create facts on the ground. Reversal becomes harder when real implementation has occurred.
- Practice radical transparency. Publish progress, setbacks, costs, and tradeoffs. Transparency builds the credibility that sustains support across leadership transitions and reduces the risk that future leaders view the program as a black box inherited from predecessors.
Key question for OPM and OMB leadership to ask: What specific structures, commitments, and artifacts can be put in place in the next 18 months that would make it difficult for a future administration to abandon or significantly scale back this initiative?
OPM needs to manage the risk without paralyzing the program
All of these failure modes are, in our view, plausible but they are not inevitable. The fact that they’re extremely foreseeable makes them easier to plan around.
The good news is that the risks facing this initiative are not primarily technical. Whomever OPM selects as the vendor will likely be able to deliver some kind of working product. Rather, the risks are mostly governance risks, capacity risks, and incentive-alignment risks. The bad news is that these risks are harder to mitigate, and addressing them requires more than better requirements or more detailed project plans. It requires a conscious effort to design institutions, funding flows, and oversight mechanisms that help the program succeed rather than simply document its shortcomings.
With this in mind, there are some things that OPM and OMB can do to get a better hold on them. In particular, there are programmatic opportunities to rethink the use of independent verification and validation (IV&V) and the role of other actors in the federal ecosystem, such as Congress, GAO, and OMB, who often play their roles as overseers, authorizers, and advisers in the process of transformation. There are also obvious lessons from private sector product management experience that can help reduce the risk of a catastrophic meltdown posed by large-scale waterfall implementations.
Traditional IV&V models often emphasize exhaustive risk identification, which may be appropriate for discrete, bounded systems. However, for a multi-year, enterprise-scale transformation operating in a high-risk environment, a more useful IV&V strategy would be selective, staged, and decision oriented. Rather than attempting to monitor everything at once, IV&V should focus on a small number of high-leverage risk domains aligned with the failure modes identified in this paper, such as configuration governance and convergence discipline, funding adequacy and sustainability, agency readiness and sequencing decisions, and executive sponsorship and institutionalization. Within these domains, IV&V should aim not merely to assess compliance, but to inform real decisions: whether to pause, resequence, simplify, or escalate. Stage gating the implementation based on these factors (rather than just cost, schedule, and performance) can help OPM and OMB course correct when they need to rather than barrel ahead until it is too late.
In conjunction with this, OPM should lean into its relationship with stakeholders such as Congress and GAO. Agencies and program managers often avoid interacting with these officers because such interactions seem to invite scrutiny and criticism. But this program, with its size and ambition, will not avoid scrutiny along the way. And engaging these powerful actors earnestly up front offers OPM the best chance it will have to enlist them as allies and secure longer-term sponsorship for this important effort.
Finally, OPM should consider adopting a product operating model for HR 2.0 rather than managing it as a traditional, time-boxed “waterfall” IT project. As our colleagues have previously argued, the product operating model directly counteracts several of the failure modes identified in this paper. Replacing rigid milestone-based delivery with iterative development cycles reduces the risk of configuration complexity spiraling out of control, because problems surface early and can be corrected before they calcify into permanent accommodations. Embedding dedicated technical product managers within the program and empowering them to resolve ambiguity, manage scope, and make tradeoff decisions addresses the governance bottleneck risk by ensuring that day-to-day decisions don’t require constant escalation to senior leadership. Continuous, outcome-based funding aligned to a product model mitigates the funding fragility by shifting the budgetary conversation from one-time project appropriations to sustained investment in a living service. And because the product model emphasizes organizational alignment with outcomes rather than obstacles, it helps insulate the program against the loss of executive sponsorship: durable team structures, institutionalized feedback loops, and transparent progress metrics create continuity that persists even as political leadership turns over.
In short, the product operating model is an institutional design that would reduce the probability of several of the most dangerous failure scenarios HR 2.0 faces, and in doing so, increase the probability of historic success.
A Final Observation
Federal HR IT modernization is ambitious because it must be. The federal government is one of the largest single employers in the world and it runs on badly outdated and outclassed HR software. The status quo is unsustainable. Fragmentation, duplication, and opacity carry their own costs and risks. The choice, then, is not between risk and safety. It is between managed risk and unmanaged risk. The failure modes outlined in this paper are not predictions — they don’t have to come true — but they are warnings. Each represents a point at which deliberate choices can either compound fragility or build resilience.
The success of this initiative will depend less on technical execution than on leaders willing to confront these choices honestly, early, and repeatedly. That, more than any single procurement or platform decision, will determine whether HR 2.0 becomes a foundation for reform — or another cautionary tale about a federal IT meltdown…
For a more detailed examination of these ideas, please download the full report (pdf) here.
Appendix: A brief history of HR IT modernization and consolidation in the federal government
Early agency‑built HR systems
Federal agencies, like their private sector counterparts, began building enterprise HR and payroll systems in the 1970s. These systems were typically bespoke, homegrown solutions designed to meet the specific needs of individual agencies. They were written in what was then state-of-the-art programming languages such as COBOL and Natural, languages that are now considered archaic, despite the fact that they continue to underpin mission‑critical systems in the banking industry and across government.
At the time, this approach made sense. Commercial HR software barely existed, and the federal government was already one of the largest employers in the world. Computing helped agencies manage complex, routine tasks like payroll and therefore were highly customized. There was little expectation that systems would interoperate across agencies, as the internet did not yet exist in its modern form. Each organization optimized for its own statutory authorities, workforce composition, and operational needs.
Over time, however, these systems accreted complexity. New laws, pay plans, labor agreements, and reporting requirements were layered on top of old code. Documentation decayed. Original developers retired and left little in the way of documentation about what they did. Institutional knowledge became increasingly fragile. What remained were systems that worked — until they didn’t — and that were extraordinarily difficult to modify, integrate, or retire.
The commercial ERP wave
In the 1990s, commercial ERP systems, led by vendors such as SAP and PeopleSoft, rose to prominence in the private sector. Initially focused on manufacturing and finance, these platforms gradually expanded to include HR, payroll, and talent management functionality for almost all large enterprises.
By the late 1990s, federal agencies began adopting commercial HR systems, overwhelmingly selecting PeopleSoft. These implementations promised modernization, vendor support, and alignment with private‑sector best practices. In practice, agencies often customized these systems extensively to replicate legacy processes and accommodate federal‑ and agency-specific requirements inherent in the custom solutions they replaced. While modernization occurred, standardization largely did not.
Payroll consolidation: A rare success
By the early 2000s, the federal government operated more than 20 mostly bespoke payroll systems, each of which did the same basic thing: calculate payroll and send instructions to the Department of the Treasury to process. This level of duplication was expensive and untenable, leading the Bush administration to adopt payroll consolidation as a pillar of its newly minted “e‑Government” agenda and the newly established HR Line of Business.
This effort is notable for both its sponsorship and its execution. The initiative was driven directly by OMB Director Mitch Daniels, with strong leadership from OPM Director Kay Coles James. OPM conducted a formal internal competition among federal payroll providers, resulting in the designation of four agencies — the General Services Administration, the Defense Finance and Acquisition Service (DFAS), the Department of Agriculture’s National Finance Center, and the Department of the Interior’s National (now Interior) Business Center — as payroll shared service providers, responsible for processing not only their own agency’s payroll but also that of several customer agencies. The Department of Agriculture, for example, processes payroll for the Departments of Homeland Security and Justice, while DFAS processes payroll for the Veterans Administration and the Department of Energy, among other arrangements.
Despite early skepticism and schedule slippage, payroll consolidation succeeded for the most part. By 2006–2007, most civilian agencies had migrated payroll operations to one of these providers. OPM later estimated that the effort produced roughly $1 billion in savings and cost avoidance, with continued benefits accruing over time, including better standardization and control over the data supply chain from agency systems to OPM.
Crucially, this payroll consolidation was not explicitly authorized by statute or executive order. It succeeded because senior leaders treated it as a management imperative, and they enforced compliance and sustained attention long enough to overcome institutional resistance.
The long plateau: 2007–2024
After payroll consolidation, OMB sought to extend the shared services model to broader HR functionality. Beginning in 2007, OMB issued a series of memoranda requiring agencies to migrate to approved HR shared service centers when modernizing. This policy trajectory culminated in OMB Memorandum M‑19‑16, which established Quality Service Management Offices for HR, financial management, grants management, and cybersecurity.
Despite these directives, progress was uneven. Some agencies modernized successfully; many did not. Fragmentation persisted. A defining feature of this period was the absence of sustained, senior‑level executive sponsorship comparable to that seen during payroll consolidation. HR IT modernization became a perennial priority — but rarely the top priority.
Everything You Need to Know (and Ask!) About OPM’s New Schedule Policy/Career Role: Oversight Resource for OPM’s Schedule Policy/Career Rule
In February 2026, the Office of Personnel Management finalized a rule creating Schedule Policy/Career, a new category for certain career federal positions they deem as “policy-influencing.”
When the rule was initially proposed, FAS raised concerns that removing civil servant employment protections could place unnecessary and undesirable political pressure on highly specialized scientific and technical career professionals serving in government. While we appreciate the Administration’s revisions (such as those that clarify competitive service status), important questions remain about how the rule will be implemented in practice, and how it may affect agency operations, workforce motivation, and mission delivery. This is a complex change to a long-standing system, with significant implications for thousands of current and future public servants – with great potential for unintended consequences. Congress has both a responsibility and opportunity to understand the rule’s intent, implementation, and impacts as it works constructively to shape a better federal workforce system that meets the needs of the country.
This resource is designed to help Congressional members and staff (and other oversight bodies) with cross-cutting and agency oversight roles understand what implementation could look like, where discretion lives in implementation, what changes or risks may emerge over time, and what questions may be most useful to ask in oversight activities such as hearings, briefings, letters, commissioned reports, and GAO audits. Potential areas to watch and requests are aimed at specific implementation periods, as part ongoing engagement with individual agencies, or as part of more holistic review, with the goal of supporting practical, evidence-based oversight as agencies put the rule into effect.
Background
Under the rule, Schedule P/C positions remain career, merit-based roles, but employees in Schedule P/C roles:
- Move from the competitive service to the excepted service, with no appeal for such transfers
- Lose Chapter 43 (performance) and Chapter 75 (adverse action) due process protections under Title 5
- No longer have MSPB appeal rights
- Become effectively at-will for purposes of removal
- Retain protections from prohibited personnel practices (PPP) enforced internally instead of the U.S. Office of Special Counsel (OSC)
Importantly, career staff who had competitive status can transfer to a non-Schedule P/C role and regain competitive service protections. Staff who are hired into Schedule P/C roles under the merit system can likewise gain competitive status after 2 years and acquire competitive service protections if they move out of Schedule P/C.
This rule gives agencies significantly more authority over certain career policy roles. Whether that authority improves accountability or creates new risks depends almost entirely on how agencies interrupt and apply it.
If you’re interested in….
What the rule actually changes (and what it doesn’t)
Understand
- Schedule P/C are not political appointees. Under the new regulation, schedule P/C roles are policy influencing roles hired through merit processes and who retain their roles across administrations, vs. political appointments, which are selected through the White House and whose tenure ends when a president leaves office.
- The rule primarily changes protections and removal authority for staff moved to Schedule P/C, not hiring – though overseers should stay aware of hiring practices for these roles.
- Schedule P/C roles remain career, merit-filled positions and P/C employees have or can attain competitive service status (but this is worth continued engagement on)
- However, while in P/C roles, employees lose Ch. 43/75 process due process protections and MSPB appeal rights.
Ask agencies (now)
- How are you explaining this change to managers and staff?
- By what criteria will you decide what agency positions are determined to be “policy influencing” for approval by OPM?
- What written guidance have supervisors received?
Watch
- Confusion in agencies about what this is
- Implementers with different interpretations on breadth of the definitions
- Differential discussion of or treatment of Schedule P/C roles beyond this rulemaking
Why it matters: Early confusion or inconsistency may lead to uneven or overbroad designation of roles, uneven treatment across agencies, or morale challenges due to confusion about goals.
What is policy influencing (and what isn’t)
Understand: Agencies are supposed to identify roles based on whether the duties of the position meet the statutory test for being policy influencing – the role, not the person. Agencies are told to consider: roles that:
- Shape, write, or interpret regulations or policy
- Advise senior leaders on policy choices
- Translate presidential or agency priorities into action
- Direct the work of people doing the above
- Sit in policy offices, regulatory offices, or leadership advisory roles
- Have authority to influence how laws and directives are carried out
Agencies should not be considering:
- Performance
- Seniority
- Political beliefs
- Individual behavior
Ask (after agencies have made determinations):
- What criteria did you use to determine a role was policy-influencing?
- Did you conduct a role-by-role analysis? Are there instances where you designated whole offices?
- Which occupational series and functions were included? Were scientists, attorneys, grants officials, or program managers included?
- How did you treat supervisory roles?
- What written justification exists for each position?
Watch:
- Expansion or changing of definitions over time beyond the initial intent
- Use of office-wide or team-wide designations rather than position-specific analysis
- Application of the definition to roles that are primarily technical, scientific, legal, or delivery-oriented rather than policy-shaping
- Variation in interpretation across components or agencies
Why it matters: Good oversight here is about definitions and consistency.
How positions get put on the schedule
Understand: Agencies identify the roles, OPM vets the justification, and the President makes the final decision to place the positions into Schedule Policy/Career.
Ask (after agencies have made designations)
- What process did agencies use to identify positions? Are all such positions designated Schedule P/C?
- Who approved each designation at agencies?
- What documentation supports each decision at agencies?
- How are employees and job applicants notified about placement into Schedule P/C?
- How is OPM ensuring consistency between agencies?
- Given the volume of positions reviewed, what process exists to revisit or correct designations if needed?
Ask (on a rolling basis, or in a GAO review 1 year after implementation)
- How many positions were added after the initial designation?
- What justifications were used later, and did they change in scope?
- Whether the definition of “policy-influencing” is changing?
Watch
- Whether processes remain consistent and well-documented over time
- Patterns of employee questions or concerns about how decisions were made
Why it matters: Much of the practical discretion in this rule rests in how agencies conduct and document this step. Understanding this process is key to meaningful oversight.
What the loss of Chapter 43 & 75 protections really means
Understand: This removes performance improvement periods (PIPs), MSPB appeal rights, and statutory due process (notice and response) removal processes.
Ask
- How will agencies set standards for managers to meet before removing someone on Schedule P/C?
- What internal review happens before a removal decision is finalized?
Watch
- How frequently this authority is used across agencies
- Whether managers express uncertainty about when or how to use this authority
- Differences in how agencies apply this authority
- Situations where employees raise concerns related to PPP protections
Why it matters: The health of the civil service depends on disciplined, fair, and consistent implementation of workforce policies.
What replaces MSPB and OSC review and whistleblower safeguards
Understand: Schedule P/C employees cannot appeal placement or removal through MSPB or file complaints with the OSC. Instead, the rule requires agencies to create and enforce internal protections against Prohibited Personnel Practices (PPPs), including whistleblower reprisal.
Ask (when agencies have made designations)
- What PPP/whistleblower safeguards have you established for Schedule P/C?
- Who reviews allegations of misuse?
- Are these procedures public to employees?
- If an employee is separated, will they have access to these procedures?
- Will job applicants have access to these procedures?
- How are complaints tracked and reported?
- Will the confidentiality of whistleblowers be protected?
- What training have managers received on PPP risks when using Schedule P/C authority?
- What role do IG and OSC play?
- Are Schedule P/C related PPP complaints being flagged as a category?
Watch
- Whether employees understand where and how to raise concerns
- Whether safeguards are formalized in written procedures
- Whether managers demonstrate understanding of PPP responsibilities
- Patterns in complaint data that may indicate either effective safeguards or lack of awareness
- How seriously agencies operationalize these safeguards in practice
Why it matters: Under the traditional civil service system, MSPB provided an independent judge, formal record, public decisions, visible check on agency action. OSC safeguarded the merit system by protecting federal employees and applicants from prohibited personnel practices and provided a secure channel for federal employees to blow the whistle by disclosing wrongdoing. Under Schedule P/C, legitimacy depends on whether agencies build credible, transparent, and trusted internal safeguards. Visible safeguards are essential for preventing misuse of at-will authority; protecting whistleblowers and dissenters acting in good faith; maintaining workforce trust in policy offices; ensuring accountability does not become perceived politicization. Agencies need to have strong systems before problems arise.
Hiring and merit rules
Understand: Hiring for Schedule P/C roles must still follow merit procedures. New hires in Schedule P/C can gain competitive status in 2 years.
Ask (on a rolling basis)
- Are there any differences between traditional merit hiring and Schedule P/C hiring practices?
- As the rule is implemented, how many new hires have been made into these roles?
- Have any individuals previously serving in political roles been hired into Schedule P/C roles?
Watch
- Whether employees and managers clearly understand how competitive status is gained
- Public hiring announcements and transparency around these roles
Why it matters: Perceptions of politicization may arise here.
Workforce and mission impacts
Understand: These roles will sit in a wide range of functions across agencies. Early concerns about Schedule P/C highlighted risks to sensitive, scientific, technical, or high-demand roles where continuity and ability to “speak truth to power” are valued.
Ask (on a rolling basis)
- Have you seen retention or recruitment impacts in Schedule P/C roles?
- Have employees moved to Schedule P/C declined roles or departed Federal service?
- What Schedule P/C roles are in the national security, scientific, or health fields, or fields engaged in long-term risk work?
- How are agencies addressing concerns that Schedule P/C would stifle dissent or evidence-based policymaking?
- How many employees in Schedule PC roles have transferred or competed for non-Schedule PC roles? How many have sought to?
Watch
- Hollowing out of key policy offices
- Reluctance of experienced staff to serve
Why it matters: Accountability gains should not come at the expense of mission capacity.
Does this address the performance problem it’s meant to solve?
Understand: OPM justifies the rule using MSPB and FEVS data showing managers struggle to remove poor performers; however, the rule does not introduce a more mature performance management standard.
Ask (on a rolling basis, or through GAO review)
- What evidence do you have that those in “policy influencing” roles have performance issues, or that the impact of such performance issues is greater?
- Have you used this authority to remove employees for performance issues? Why could they not be addressed under prior mechanisms?
- Are managers finding it easier to address poor performance? What about to incent strong performance?
- What indicators are you watching for improved overall performance?
- What standards are being applied for performance? Are they consistent within or across agencies?
Watch
- Rule exists on paper but behavior doesn’t change
- Different definitions for poor performance arise from adverse action, conduct and performance as defined in Chapters 43 and 75
- Performance problems persist for other reasons
Why it matters: Congress should know if the remedy matches the diagnosis.
Data Congress should request via GAO for ongoing tracking and comparison
Request from agencies:
- List of all positions designated
- Written justifications
- Counts by grade, office, and occupational series
- Number of removals using this authority
- Number of PPP/whistleblower complaints related to it
- Number of hires into Schedule P/C roles
Why it matters: Early transparency prevents speculation and enables evidence-based oversight.
Costs Come First in a Reset Climate Agenda
Building Blocks to Make Solutions Stick
Durable and legitimate climate action requires a government capable of clearly weighting, explaining, and managing cost tradeoffs to the widest away of audiences, which in turn requires strong technocratic competency.
Democratic governance needs
- Clear articulation of tradeoffs in policy design, including who pays, who benefits (and when), and why.
- Think bigger and wider in building durable coalitions for climate action, mobilizing dispersed beneficiaries and taking advantage of policy Overton windows that cut across partisan lines.
State Capacity needs
- Intergovernmental delivery muscle and partnering capacity to enable state and local actors.
- Invest in technocratic state capacity where the big wins live, like permitting and siting, interconnection and transmission, or power-market governance, and implementation capacity to limit bottleneck-driven policy failures.
- Institutionalize rigorous ex ante and regular cost benefit analysis to guide design and mid-course corrections.
Key Takeaways
- The costs of climate policy influence whether reforms benefit society, as well as their likelihood of passage and durability. Four ways to categorize climate policy costs are: negative-cost policies (pro-growth policies with climate co-benefits); low-cost policies (costs below domestic climate benefits); medium-cost policies (costs below global climate benefits); and high-cost policies (costs above global climate benefits). Cross-partisan alignment is most evident among pro-abundance progressives and pro-market conservatives.
- Negative- and low-cost policies align with domestic self-interest and comprise a growing share of the abatement curve. For example, market liberalization in permitting, siting, electricity regulation, and certain transportation applications lower energy costs and have profound emissions benefits. A prominent low-cost policy is emissions transparency. Negative- and low-cost policies hold the most potential for durable reforms and are often technocratic in nature.
- Chronic underconsideration of costs has induced an overselection of high-cost policies and underpursuit of low- and negative-cost policies. Legislative policies, such as subsidies and fuel mandates or bans, often receive no ex ante cost-benefit analysis before adoption. Interventions receiving cost-benefit analysis, especially regulation, tend to underestimate costs.
- Innovation policy – namely public support for research, development, and early-stage deployment – can align with domestic self-interest and address legitimate market deficiencies. By contrast, industrial policy for mature technology carries high costs, often erodes social welfare, and is not politically durable. Notably, public support for mature technologies in the Inflation Reduction Act was not durable, but support remained for nascent industry.
- We recommend that a reset climate agenda focus on abatement results over symbolic outcomes, prioritize state capacity for technocratic institutions, and emphasize cost considerations in policy formulation and maintenance. Negative cost policies warrant prioritization, with an emphasis on mobilizing beneficiaries like consumer, non-incumbent supplier, and taxpayer groups to overcome the lobbying clout of entrenched interests. Robust benefit-cost analysis should precede any cost-additive policies and be periodically reconducted to guide adjustments.
Introduction
Public policy involves tradeoffs. The primary tradeoff for climate change mitigation is economic cost. Secondary tradeoffs include commercial freedom, consumer choice, and the quality or reliability of goods and services. Political movements seeking to address a collective action problem, such as climate change, are prone to overlook the consequences of tradeoffs on other parties, like consumers and taxpayers. This paper posits that the cost tradeoffs of climate change mitigation have been underappreciated in the formation of public policy. This has resulted in an overselection of high cost policies that are not politically durable and may erode social welfare. It also results in overlooking low or negative-cost policies that are durable and hold deep abatement potential. These policies can have broad political appeal because they align with the self-interest of the United States, however they typically require dispersed beneficiaries to overcome the concentrated lobby of entrenched interests.
A core, normative objective of public policy is to improve social welfare, which “encourages broadminded attentiveness to all positive and negative effects of policy choices”. Environmental economics determines the welfare effects of climate change mitigation policy by the net of its abatement benefits less the costs. The conventional technique to determine abatement benefits is the social cost of carbon (SCC). The barometer for whether climate policy benefits society is to determine whether abatement benefits exceed costs. Accounting for full social welfare effects requires consideration of co-benefits as well, granted these tend to be conventional air emissions with existing mitigation mechanisms covered under the Clean Air Act. Nevertheless, accounting for costs is essential to ensure climate policy benefits society.
Abatement costs also have a discernable bearing on the likelihood and durability of policy reforms. Climate policies exhibit patterns of passage, mid-course adjustments, and political resilience across election cycles based on the constituency support levels linked to benefit-allocation and cost imposition. This paper develops four policy classifications as a function of their abatement benefit-cost profile, and uses this framework to examine the political economy, abatement effectiveness, and economic performance of select past and potential policy instruments.
Political Economy and Policy Taxonomy
The translation of climate policy concepts into legitimate policy options in the eyes of policymakers can be viewed through the Overton Window. That is, politicians tend to support policies when they do not unduly risk their electoral support. The Overton Window for climate policy is constantly shifting within and across political movements with the foremost factor being cost.
In a 2024 survey of voters, the most valued characteristics of energy consumption were 37% for energy cost, 36% for power availability, 19% for climate effect, 6% for U.S. energy security effect, and 1% for something else. Democrats slightly valued energy cost and power availability more than climate effects. Independents and Republicans heavily valued energy cost and power availability more than climate effect.
Progressives have long exhibited greater prioritization of climate change policy, but cost concerns are driving an overhaul of the progressive Overton Window on climate change. In California, which contains perhaps the most climate-concerned electorate in the U.S., progressives have begun a “climate retreat” to recalibrate policy as “[e]lected officials are warning that ambitious laws and mandates are driving up the state’s onerous cost of living”. Nationally, a new progressive thought leadership think tank is encouraging Democrats to downplay climate change for electoral benefit. Importantly, they find that 61% of battleground voters acknowledge that “climate change is at least a very serious problem,” but that “it is far less important than issues like affordability.”
Similarly, veteran progressive thought leaders, such as the Progressive Policy Institute, now stress that “energy costs come first” in a new approach to environmental justice. While emphasising the continued importance of GHG emissions reductions, those policy leaders are making energy affordability the top priority, amid a broader Democratic messaging pivot from climate to the “cheap energy” agenda. The rise of cost-conscious progressives is particularly notable because the progressive electorate has expressed a higher willingness to pay to mitigate climate change than moderate and conservative electoral segments.
Economic tradeoffs, namely costs and more government control, has long been the central concern on climate policy for the conservative movement. The conventional climate movement messaged on fear and the need for economic sacrifice, which is the antithesis of the conservative electoral mantra: economic opportunity. Yet the conservative climate Overton Window emerged with a series of state and federal policy reforms when climate change mitigation aligned with expanded economic opportunity. However, pro-climate conservative thought leaders remain opposed to high cost policies, such as calling to phase out Inflation Reduction Act (IRA) subsidies for mature technologies.
Many leading conservative thought leaders continue to challenge the climate agenda writ large because of its association with high cost policies. For example, President Trump’s 2025 Climate Working Group report was expressly motivated by concerns over “access to reliable, affordable energy” while acknowledging that climate change is a real challenge. Similarly, a 2025 American Enterprise Institute report finds that the public is most interested in energy cost and reliability and unwilling to sacrifice much financially to address climate change. Meanwhile, climate-conscious conservative thought leaders like the Conservative Coalition for Climate Solutions and the R Street Institute continue to emphasize a market-driven, innovation-focused policy agenda that prioritizes American economic interests and drives a cleaner, more prosperous future. Altogether, it indicates a conservative Overton Window on negative and low-cost climate change mitigation.
While cost is driving the Overton Window within each political movement, it also buoys the potential for alignment across political movements. Political movements are not monoliths, but rather exhibit major subsets within each movement. The progressive movement has seen gains in popularity among its populist left flank, often identified as the “democratic socialist” wing, which contributes to ongoing debate about Democrats’ ideological direction. Climate policy initiated by this wing, however, is associated with high economic tradeoffs (e.g., degrowth) and has prompted a backlash within the progressive movement. By contrast, a subset of the progressive movement, sometimes labelled “abundance progressives,” has emerged to support a more pro-market, pro-development posture. This movement is especially responsive to energy cost concerns, and is an emerging substitute for the anti-development traditions of the progressive environmental movement. Overall, variances in the progressive movement are fairly straightforward to categorize linearly on the economic policy spectrum.
The Republican electorate views capitalism far more favorably than Democrats, but with modest decline in recent years. Republicans have trended away from consistently conservative positions associated with limited government, which historically emphasized the rule of law and a strict cost-benefit justification for government intervention in the market economy. They have migrated towards right-wing populism associated with the Make America Great Again (MAGA) movement. Right-wing populism is hard to operationalize for economic policy because it is not a standalone ideology, but a movement vaguely attached to conservative ideology. Generally, the “America First” orientation of MAGA implies positions based on the self-interest of the U.S., with the Trump administration prioritizing cost reductions in energy policy.
MAGA is further to the right of conventional conservatives on environmental regulation and general government reform. For example, conservatives have noted the contrast between conservative “limited, effective government” and the Department of Government Efficiency’s “gutted, ineffective government” reform approach. On the other hand, MAGA will occasionally back leftist policy instruments, such as coal subsidies, wind restrictions, executive orders to override state policies, and emergency authorities for fossil power plants. These are often justified to counteract the leftist policies passed by progressives (e.g., renewables subsidies, fossil restrictions, emergency authorities for renewables), resulting in dueling versions of industrial policy. In other words, ostensible overlap between MAGA and progressives on policy instrument choice actually reflects the use of similar tools used for conflicting purposes (e.g., restrictive permitting or subsidies for opposing resources; i.e. picking different “winners and losers”). Nevertheless, the disciplinary agent for right-wing energy populism has been cost concerns, which have influenced the Trump administration to pursue more traditionally conservative energy policies like permitting reform and lowering electric transmission costs.
This political economy identifies the broadest cross-movement Overton Window between moderate or “abundance progressives” and traditional conservatives. Regardless, both broad movements exhibit cost sensitivity and growing prioritization of U.S. self–interest. Distinguishing the domestic SCC from global SCC is essential to determine what policies are consistent with the self-interest of the U.S. versus the world as a whole. Traditionally, the U.S. government only considers domestic effects in cost-benefit analysis, yet the vast majority of domestic climate change abatement benefits accrue globally.
The first SCC, developed under the Obama administration, relied solely on a global SCC. Leading conservative scholars, including the former regulatory leads for President George W. Bush, criticized the use of the global SCC only to set federal regulations. They argued for a “domestic duty” to refocus regulatory analysis on domestic costs and benefits. Similarly, the first Trump administration used a domestic SCC. Although the second Trump administration moved to discard the SCC outright, this appears to be part of a regulatory containment strategy, not a reflection of the conservative movement’s dismissal of the negative effects of climate change. In other words, even if the SCC is not the explicit basis for policymaking, it is a useful heuristic for policymakers.
The proper value of the SCC is the subject of intense scholarly and political debate. It has fluctuated between $42/ton under President Obama, $1-$8/ton under President Trump, and $190/ton under the Biden administration (all values for 2020). The main methodological disagreement has been over whether to use a domestic or global SCC, with the Trump administration position guided by “domestic self-interest.” This suggests the original domestic and global SCC values may approximate the Overton Window parameters the best. This underscores the following policy taxonomy that characterizes climate abatement policies by cost relative to domestic and global SCC levels:
- Class I policy: negative abatement costs. Such policies are widely viewed as “no regrets” by scholars and political actors across the spectrum because they constitute sound economic policy that happens to carry climate co-benefits. The Overton Window is most robust for Class I policy. It typically takes the form of fixing government failure, such as permitting reform.
- Class II policy: positive abatement costs below the domestic SCC. These low-cost policies often fall within the Overton Window, because they advance U.S. self-interest (i.e., positive domestic net benefits). Class II policies have a small abatement cost range (e.g., up to $8/ton). One estimate puts them at 4-14 times smaller than the global SCC.
- Class III policy: abatement costs between the domestic SCC and global SCC. These medium-cost policies improve global social welfare, but are not in the self-interest of the U.S., excluding co-benefits. Most cost-additive policies that pass a global SCC test fall in this range, underscoring why climate change is an especially challenging strategic problem; those incurring abatement costs do not accrue most abatement benefits. Class III policies face inconsistent domestic support and often require international reciprocation to be in the self-interest of the U.S.
- Class IV policy: abatement costs exceeding the global SCC. These high-cost policies fail a climate-only cost-benefit test. In other words, Class IV policies erode social welfare, excluding co-benefits. Class IV policies may be effective at reducing emissions, but often leave society worse off. Class IV policies are challenging to pass and are hardest to sustain.
Policy Applications
There are myriad policies across the abatement cost spectrum. This analysis applies to particularly popular domestic policies already pursued or readily considered. This includes policies targeting the environmental market failure via direct abatement (GHG regulation) and indirect abatement (public spending, clean technology mandates, and fuel bans). It also includes policies targeting non-climate market failure, yet hold deep climate co-benefits (innovation policy). The analysis also examines policies that correct government failure and have major climate co-benefits (permitting, siting, and electric regulation reform).
Fuel Mandates and Bans
For the last two decades, the most prevalent climate policy type in the U.S. has been state level fuel mandates and bans. Last decade, the environmental movement came to prefer policies that explicitly promote or remove fuels or technologies, not emissions. This is despite ample evidence in the economics literature that market-based policies are more effective and carry far lower abatement costs. Nevertheless, the most common domestic climate policy instrument this century has been state renewable portfolio standards (RPS). The literature notes several key findings from RPS:
- RPS has substantial but diminishing abatement efficacy. RPS compliance drove the bulk of initial renewables deployment, but declined to 35% of U.S. renewables capacity additions in 2023. This reflects the improved economics of renewable energy, which went from an infant industry in the 2000s to a mature technology and the preferred choice of voluntary markets by the 2020s. Renewables also exhibit declining marginal abatement as penetration levels grow. This underscores the environmental underperformance of policies promoting fuel, not emissions reductions.
- Binding RPS increases costs, with large state variances based on target stringency and carveouts. RPS compliance costs average 4% of retail electricity bills in RPS states and reach 11-12% of retail bills in states with solar carve-outs. Stringency is a key factor, as some RPS are not binding due to strong market forces, whereas binding RPS increases costs. Abatement cost estimates of RPS vary widely, with one prominent study placing compliance with RPS from 1990-2015 at $60-$200/ton. Within the Mid-Atlantic region alone, implied states’ RPS compliance costs in 2025 ranged from $11/tonne to $66/tonne, with solar carveout compliance clocking in at $70/tonne to $831/tonne. The future abatement cost of renewables integration is highly sensitive to RPS stringency and technology cost assumptions, with one estimate of implied abatement costs ranging from zero (nonbinding) to $63/tonne at 90% requirement in 2050. This evidence qualifies RPS as a class II to class IV policy, depending on its design.
- States with stringent RPS face challenging compliance targets, prompting calls for reforms to mitigate cost. Compliance with interim targets has generally been strong but stringent RPS states are beginning to fall behind on their targets. For example, renewable energy credit (REC) costs are nearing alternative compliance payment levels. To reduce costs, popular reform ideas have included delaying compliance timelines, adopting a clean energy standard to capture broader resource eligibility, or making RECs emissions weighted.
- Modest RPS exists in some conservative states but aggressive RPS policy has, generally, only proven popular in progressive states. As of late 2024, 15 states plus the District of Columbia had RPS targets of at least 50% retail sales, and four have 100% RPS. Sixteen (16) states have adopted a broader 100% clean electricity standard, though the broad definition of clean energy dilutes expected abatement performance in some states. Overall, renewable or clean portfolio standards do not appear to hold broad Overton Window alignment potential beyond modest applications.
Micro-mandates have also sprung up, primarily in progressive states. These have often targeted the promotion of nascent or symbolic energy sources that the market would not otherwise provide, with the costs obscured from public view (e.g., rolled into non-bypassable electric customer charges). A good example is offshore wind requirements in the Northeast, which carries a high abatement cost (over $100/ton).
Fuel bans have become increasingly popular climate policy in progressive states and municipalities. Beginning in 2016, a handful of progressive states began banning coal. However, this does not appear to have created much cost or abatement benefit, as evidenced by a lack of commercial interest in coal expansion in areas without such restrictions. In fact, neither federal nor state regulation was responsible for steep emissions declines from coal retirements. Coal retirements were mostly driven by market forces, especially breakthroughs in low-cost natural gas production and high efficiency power plants. Policy factors, like the Mercury and Air Toxics Rule, were secondary drivers of coal plant retirement.
Around 2020, California, New York, and most New England states began adopting partial natural gas bans or de facto bans on new gas infrastructure through highly restrictive permitting and siting practices. Unlike coal restrictions, these laws have markedly decreased commercial activity, namely gas pipeline and power plant development, and in some cases caused economically premature retirements. This has caused “pronounced economic costs and reliability risk.” Resulting pipeline constraints drive steep gas price premiums in these states, which translate into a core driver of elevated electricity prices.
Insufficient pipeline service in the Northeast is especially problematic, as demonstrated by a December 2022 winter storm event that nearly led to an unprecedented loss of the Con Edison gas system in New York City that would have taken weeks or months to restore. Further, preventing gas infrastructure development does not provide a clear abatement benefit, because more infrastructure is needed to meet peak conditions even if gas burn declines. A prominent study found a 130 gigawatt increase in gas generation capacity by 2050 was compatible with a 95% decarbonization scenario.
Progressive states and municipalities have also pursued natural gas consumption bans. This policy may carry exceptional cost, especially for existing buildings, with potentially well over $1 trillion in investment cost to replace gas with electric infrastructure. One estimate put the cost of natural gas bans at over $25,600 per New York City household. A Stanford study projected a 56% electric residential rate increase in California from a natural gas appliance ban. Generally, conservative thought leaders and elected officials have opposed natural gas bans for cost as well as non-pecuniary reasons, including security concerns and the erosion of consumer choice. This applies even for prominent members of the Conservative Climate Caucus. Altogether, gas bans are considered class IV policy with virtually no Overton Window alignment.
GHG Transparency
GHG regulation takes various forms. The least stringent is GHG transparency, which addresses an information deficiency and lowers transaction costs in voluntary markets. This begins with reporting and accounting requirements on emitters (Scope 1 emissions). Public policy can help resolve measurement and verification problems that have eroded confidence in voluntary carbon markets. GHG transparency policy can also standardize terminology and provide indirect emissions platforms. For example, making locational marginal emissions rates on power systems publicly available lets market participants identify the indirect power emissions of power consumption (Scope 2 emissions). Progressives have consistently favored GHG transparency policy, while conservatives have typically supported light-touch versions of it like the Growing Climate Solutions Act.
The second Trump administration recently pursued removal of basic GHG reporting requirements on ideological grounds, specifically repeal of the GHG Reporting Program (GHGRP). This appears to reflect an optical deregulatory agenda over an effective one. Conservative groups have warned of the downsides of GHGRP repeal. Pressure to course correct may prove fruitful, given that the industry the Trump administration aims to assist – oil and natural gas – maintain that the U.S. Environmental Protection Agency (EPA) should retain the GHGRP. A recent analysis found that if states replace the GHGRP, new programs will be more expensive (Figure 2).
Many regulated industry and conservative groups instead support a low compliance cost GHG reporting regime with durability across future administrations. This not only applies to direct emissions reporting but indirect emissions reporting, as in the absence of federal policy industry faces a patchwork of compliance requirements across states and foreign governments. The same economic self-interest rationale justifies a role for limited government in emissions accounting, with an emphasis on the capital market appeal of showcasing the “carbon advantage” of the U.S. in emissions-intensive industries. An example is liquified natural gas, whose export market is enhanced by showcasing its lifecycle emissions advantage over foreign gas and coal.
The abatement effectiveness of GHG transparency has grown appreciably in the 2020s, as voluntary industry initiatives have sharply increased. This policy set enables an efficient “greening of the invisible hand” with staying power, as corporate environmental sustainability efforts appear resilient regardless of political sentiment, unlike corporate social endeavors. In fact, the aggregate willingness to pay for voluntary abatement from producers, consumers, and investors suggests that well-informed domestic markets go a long way towards self-correcting the externality of GHGs (e.g., convergence of the private and social cost curves). Certain voluntary corporate behaviors may even exceed the global SCC, especially commitments to nuclear, carbon capture, and other higher cost abatement generation financed by the largest sources of power demand growth. Well-functioning voluntary carbon markets could yield roughly one billion metric tons of domestic carbon dioxide abatement by 2030. Providing locational marginal emissions data can slash abatement costs from $19-$47/ton down to $8-$9/ton while doubling abatement levels from some power generation sources.
Overall, efficient GHG transparency policy described above is a low-cost mitigation strategy consistent with class II designation. Basic, federal GHG transparency policy may even constitute class I policy, because it avoids the higher compliance cost alternative of a patchwork of state and international standards that would manifest in the absence of federal policy. However, stringent GHG transparency policy may constitute class III or IV policy. Prominent examples include a recent California climate disclosure law and a former Securities and Exchange Commission proposed rule to require emissions disclosure related to assets a firm does not own or control (Scope 3). Such efforts may obfuscate material information on climate-related risk and worsen private-sector led emission mitigation efforts.
Direct GHG Regulation
Classic environmental regulation takes the form of a command-and-control approach. These instruments include applying emissions performance standards or technology-forcing mechanisms, typically for power plants or mobile sources. These policies vary widely in stringency and cost. Overall, command-and-control is widely considered in the economics literature to be an unnecessarily costly approach to reducing GHGs relative to market-based alternatives. It can also result in freezing innovation, by discouraging adoption of new technologies.
Federal command-and-control GHG programs have not been particularly environmentally effective, cost-effective, or demonstrated legal or political durability. The first power plant program was the Clean Power Plan, which was struck down in court, and yet its emissions target was achieved a decade early from favorable market forces and subnational climate policy. The most recent federal command-and-control approaches for GHG regulation were 2024 EPA rules for vehicles and power plants. A 2025 review of these and other federal climate regulations over the last two decades of federal climate regulations found:
- EPA’s cost estimates to be “extraordinarily conservative” with suspect methodology that was prone to error and inconsistent with economic theory;
- Assessed costs of $696 billion compared to regulators’ estimate of $171 billion, or an increase in abatement cost from $122/tonne to $487/tonne; and
- EPA is too optimistic in its assumptions of benefits.
The 2025 review study implies that past federal command-and-control had very high cost – well into class IV range. It has also been a top priority of conservatives to undercut. However, it is possible for modest command-and-control policy with class II or III costs.
Some conservatives, noting EPA’s legal obligation to regulate GHGs and the cost of regulatory uncertainty from decades of EPA policy oscillations between administrations, suggested modest requirements as a better option to replace high cost rules in order to mitigate legal risk and provide industry a predictable, low-cost compliance pathway. For example, conservatives argued that replacing high cost requirements for power plants to adopt carbon capture and storage (CCS) with low cost requirements for heat rate improvements may lower compliance costs more than attempting to repeal the Biden era rule for CCS outright. Similarly, the oil and gas industry opposed stringent GHG regulations on power plants and mobile sources, but often validated alternative low cost compliance requirements.
The first Trump administration pursued modest replace-and-repeal GHG regulation. The second Trump administration has opted for repeal policies and to eliminate the endangerment finding via executive rulemaking. However, regulated industry and many conservative thought leaders believe this is a strategic blunder, given the low odds of legal success, resulting in the perpetuation of “regulatory ping-pong that has plagued Washington, D.C., for decades.” If the courts uphold Massachusetts v. EPA and the associated endangerment finding, this implies that modest command-and-control policy may have durable political alignment potential. Yet this does not hold much abatement potential. In the absence of a legal requirement to regulate GHGs, there is unlikely to be broad political alignment for even modest command-and-control policy. Conservatives tend to view this as a gateway to more costly policies that will probably not meaningfully affect global GHG trajectories.
The 2025 review study understates the full cost of U.S. climate regulations because they exclude state and local levels. Although no comprehensive study of state climate regulation is known, command-and-control state regulations often raise major cost concerns as well. The cost and environmental performance of such state programs varies immensely, often owing to differences in the accuracy of abatement technology costs that regulatory decisions are based upon (e.g., the failure of California’s zero-emission vehicle program compared to success with its low-emission vehicle program). A recent example is California’s rail locomotive mandate, which projected to impose tens of billions of dollars in costs before being withdrawn. State command-and-control regulation is commonplace in progressive states, but not beyond, implying meager Overton Window alignment.
A more economical version of GHG regulation is a system of marketable allowances, or cap-and-trade (C&T). Over three decades of experience with C&T programs reveals two things. First, C&T is environmentally effective and economically cost effective relative to command-and-control policy. Second, C&T performance depends on its design quality and interaction with other policies. Abatement costs depend on stringency and other design features, but C&T in a backstop role is generally close to the domestic SCC, rendering it class II policy. Robust C&T generally falls in the class III policy range. C&T is an example of abatement policy that can be cost-effective on a per unit basis, but given the breadth of its coverage its total costs can be substantial. Recent developments in Pennsylvania indicate a possible preference for policies with higher per-unit abatement costs than C&T, which may reflect a political preference for policies with less cost transparency and lower aggregate costs.
Some environmental C&T complaints are valid, such as emissions leakage, but C&T effectiveness concerns are generally readily fixable design flaws. C&T effectiveness complaints are often the result of interference from other government interventions like fuel mandates, relegating C&T to a backstop role and suppressing allowance prices. Such state interventions triggered anti-competitive concerns in wholesale power markets overseen by the Federal Energy Regulatory Commission (FERC). This prompted conservative state electric regulators to call for a conference to validate mechanisms like C&T as a market-compatible alternative to high cost interventions. Conservative expert testimony at that conference, invited by conservative FERC leadership, explained that interventions layered on top of C&T merely reallocate emissions reduction under a binding cap, which raises costs, creates no additional abatement, and undermines innovation. This implies that such states might increase abatement and lower aggregate costs by upgrading the role of C&T and downgrading the role of costlier interventions.
In the 2000s, bipartisan interest in federal C&T policy arose, but it failed and has not resurfaced. In its absence, states have supplanted federal policy with subnational C&T programs. However, the durability of C&T beyond progressive states is unclear. Moderate states have sometimes joined a regional C&T program under Democratic leadership, but sometimes departed them under Republican leadership. Conservative state groups typically challenge C&T adoption and seek repeal of C&T programs like the Regional Greenhouse Gas Initiative. This suggests that C&T is at the fringe, but typically outside, an Overton Window across political movements.
Permitting and Siting
Permitting policy can base decisions explicitly on GHG criteria, or they can be based on non-GHG factors but hold indirect GHG consequences. Generally, only progressive states and presidents have pursued the former. Federally, these include the Obama administration’s “coal study” and Biden administration’s “pause” on liquified natural gas (LNG). The LNG pause did not provide any apparent emissions benefit, yet carried substantial foregone economic opportunity and strategic value to U.S. allies. Pragmatic progressive thought leaders expressed concern with the pause, noting the creation of economic and security risks, and suggested lifting the pause in exchange for companies to commit to strict, third-party verified methane emissions standards. Relatedly, some conservative thought leaders have supported policy that enables voluntary participation in certified programs that provide market clarity and confidence to harness private willingness to pay for lower GHG products. This has been buttressed by support from an industry-led effort to advance a market for environmentally differentiated natural gas based on a standard, secure certification process.
Permitting constraints on clean technology supply chains can have perverse economic and emissions effects. A prime example is critical minerals, which are essential components to clean energy technologies. A net-zero emission energy transition, relative to current consumption, would increase U.S. annual mineral demand by 121% for copper, 504% for nickel, 2,007% for cobalt, and 13,267% for lithium. Market forces, unsubsidized, are poised to produce a sufficient amount of domestic copper and lithium supply to satiate a large share of domestic demand, but face undue barriers to entry that restrict production far below its potential. To meet net-zero objectives, permitting reform allowing all currently proposed projects to enter the market would lower U.S. import reliance for copper from 74% to 41%, while dropping lithium import reliance from 100% to 51%.
Expanding domestic mining no doubt carries local environmental tradeoffs. However, the U.S. has some of the most stringent and comprehensive mining safeguards in the world. Thus, foregoing development domestically is likely to push mining toward foreign countries with inferior environmental, safety, and child labor protections. It is therefore critical that domestic permitting decisions account for the unintended effects of denying permits, not merely the direct consequences of approving a project.
Permitting and siting constraints on energy infrastructure also impose major costs and foregone abatement. These entry barriers largely exist as environmental safeguards, yet almost always inhibit projects with a superior emissions profile to the legacy resources they replace. In fact, 90% of planned and in progress energy projects on the federal dashboard were clean energy related as of July 2023. In 2023, the ratio of clean energy to fossil projects requiring an environmental impact statement to comply with the National Environmental Policy Act (NEPA) was 2:1 for the Department of Energy and nearly 4:1 for the Bureau of Land Management. A 2025 study estimated that bringing down permitting timelines from 60 months to 24 months would reduce 13% of U.S. electric power emissions.
Permitting has proven to be a litmus test for the progressive environmental movement, as the movement bifurcates between anti-development symbolists and pragmatic pro-abundance progressives. While a minority of mainstream environmental groups have become amenable to permitting reform, such as The Nature Conservancy and Audubon Society, the core of progressive environmental groups have not. Instead, new progressive groups like Clean Tomorrow and the Institute for Progress filled the pro-abundance void alongside traditional market-friendly progressive groups like the Progressive Policy Institute. This progressive subset has helped influence moderate Democrats to support permitting reform in a collaborative way with conservatives.
Permitting reform has long been championed by conservatives for its economic benefits, with climate considerations typically a secondary-at-best rationale. Yet permitting reform has become a priority for the newer climate-minded conservative movement. However, permitting has also proven to be a differentiator between conservatives and right-wing populists. The latter engages in forms of government intervention that sometimes contradict conservative principles. For example, the Trump administration enacted an offshore wind energy pause that followed the same problematic blueprint as the Biden administration’s LNG pause. This elevates the importance of technology-neutral permitting reforms with an emphasis on permitting permanence safeguards.
In recent years, a coalition of Republicans, centrist Democrats, and clean energy and abundance advocates have pressed for reform to NEPA. A broad suite of federal permitting reforms with bipartisan appeal was identified in a 2024 report by the Bipartisan Policy Center. Bipartisan alignment led to the passage of the Fiscal Responsibility Act of 2023 into law and the Senate passage of the Energy Permitting Reform Act of 2024 (EPRA). Although a 2025 Supreme Court decision suggests executive actions alone may substantially reduce NEPA obstacles, plenty of NEPA and other federal statutory reforms remain of high value and hold considerable bipartisan potential.
The positions of leading progressive, conservative, and centrist thought leadership organizations highlight alignment on various federal permitting and siting reforms. These include statutory changes to NEPA, the Endangered Species Act, the Clean Water Act, the Clean Air Act and the National Historic Preservation Act. Substantive alignment includes reforms that reduce litigation risk (e.g., judicial review reform), limit executive power to stop project approvals and undermine permitting permanence, maintain technology neutrality, strengthen federal backstop siting authority for interstate infrastructure, codify the Seven County decision, and streamline agency practices while ensuring sufficient state capacity.
Despite considerable positive momentum at the federal level, the greatest permitting and siting barriers generally reside at the state and local levels and trending sharply in a more restrictive direction. Wind and solar ordinances have grown by over 1,500% since the late 2000s. Oil and gas pipelines and power plants face mounting permitting and siting restrictions in progressive states, which not only raise costs but do not necessarily reduce emissions. In fact, the New England Independent System Operator said that a lack of natural gas infrastructure in the region has raised prices and pollution by forcing reliance on higher-cost resources like oil-fired power plants. The only major power generation resource with a less restrictive trend is nuclear, as six states recently modified or repealed nuclear moratoria to ease siting.
Motivation for opposing energy infrastructure permitting has included the well-known “not in my backyard” concerns, such as noise, construction disruptions, or land use conflicts. Interestingly, much opposition appears to come from perception, as much as substantiated negative effects. Relatedly, permitting resistance rationales increasingly appear to result from ideological opposition to particular energy sources. Finally, much opposition and most litigation of energy projects comes from non-governmental organizations, not the land owners directly affected. Altogether, this underscores the importance of permitting and siting reform that improves the quality of information to agencies and parties, ties decisionmaking to specific harms not speculative claims, limits standing to affected parties, and creates appeals processes for landowners to challenge obstructive local government laws and decisions. A key tension to overcome is that technology-agnostic legislation has been more likely to advance in states with one or more Republican chamber, yet environmental advocates resist “all-of-the-above” reforms.
Policies that reduce permitting and siting burdens are class I: they boost economic output and are increasingly key to emissions reductions. Permitting and siting policies that are restrictive on fossil development are not particularly effective at reducing emissions and often add considerable cost, granted costs vary widely depending on the nature of the policies and implementation. Effective fossil restrictions can range from class II to class IV policy, while ineffective ones actually increase emissions. The political economy of permitting and siting must overcome the lobby of entrenched suppliers, who seek to maintain competitive moats. An ironic example was incumbent asset owners funding environmental groups to oppose transmission infrastructure in the Northeast that would import emissions-free hydropower.
Electric Regulation
The power industry is at the forefront of energy cost concerns and decarbonization objectives. In the early 2020s, electric rates have risen most in Democratic states. These concerns reoriented progressives towards cost containment, even at the expense of climate objectives. In the 2024 election, cost of living concerns propelled Republicans to widespread victories as President Trump vowed to halve electricity prices. A year later, voter concerns over rising electricity rates in Georgia, New Jersey, and Virginia boosted Democrats in gubernatorial and public service commission (PSC) elections.
At the same time, electricity is arguably the most important sector for climate abatement given its emissions share and the indirect effects of electrifying other sectors, namely transportation and manufacturing. Ample pathways exist to reduce electric costs and emissions simultaneously, primarily by fixing profound government failure embedded in legacy regulation. Electric industrial organization shapes economic and climate outcomes, with market liberalization an advantage for both.
Electric regulation falls into two basic formats. The first is cost-of-service (CoS) regulation, where the role of government is to substitute for the role of competition in overseeing a monopoly utility. The alternative is for regulation to facilitate competition by using the “visible hand” of market rules to enable the “invisible hand” to go to work.
CoS regulation historically applied to power generation, though about a third of states enacted restructuring to introduce competition into power generation and retail services, in response to rising rates and the recognition that these are not natural monopoly services. Nearly all transmission and distribution (T&D) historically and today remains under CoS regulation. Importantly, CoS regulation motivates a utility to expand the regulated rate base upon which it earns a state-approved return. Generally, the main sources of cost discipline problems in the power industry stem from its CoS regulation segments: transmission, distribution, and the portion of generation that remains on CoS rates.
Generally, restructured jurisdictions see greater innovation and downward pressure on the supply portion of customer bills. The economic performance of restructuring is highly sensitive to the quality of implementation. This includes the quality of wholesale energy price formation and capacity market design. It also includes various elements of retail choice implementation. They have also seen improved governance, whereas CoS utilities are prone to cronyism and corruption given the inherent incentives of their business model. Competitive wholesale and retail power markets hold cost and emissions advantages through several mechanisms:
- Markets accelerate capital stock turnover when it is economic. With the brief exception of nuclear retirements, new entry is dominated by zero emission resources or high efficiency gas plants that displace legacy plants with higher emissions rates. Markets usher in new entry and induce retirements in response to economic conditions. Last decade saw markets outperform in the coal-to-gas transition, and this decade with advances in wind, solar, and storage economics. Texas, the most thoroughly restructured state, leads the country in solar, wind, and energy storage additions while placing second in gas additions. A review of restructuring found that competition worked as intended, facilitating new, low-cost entry while “driving inefficient, high-cost generation out of the market.” A new paper evaluating generator-level data found that from 2010–2023, regulated units were 45% less likely to retire than unregulated units.
- Markets encourage power plant operating efficiencies. Competitive generators adopt technologies and practices that use fuel more efficiently and improve environmental performance. The introduction of competition caused nuclear generators to adopt innovative practices to reduce refueling outage times, boosting operating efficiency by 10%. One study found 9% higher operating efficiencies in the thermal power fleet in restructured states. By contrast, CoS utilities sometimes engage in uneconomic operations because they are financially indifferent to market signals, resulting in overoperation of the fossil fleet.
- Markets reflect customer preferences, including clean power. Footprints with retail choice have seen much higher popularity of voluntary clean power programs. Competition lowers the “green premium” and customer choice allocates it equitably. This is critical as the willingness to pay for clean power varies enormously across customers. Notably, most growing power customers are large companies with ambitious corporate emissions reductions targets, which explains their commercial interest in advancing consumer choice.
- Markets better integrate unconventional resources, namely storage, wind, solar, and demand flexibility. The central planning of monopoly utilities struggles to account for the profile of variable (e.g., wind and solar) and use-limited (e.g., storage) resources. Demand flexibility is valuable to integrate more variable supply sources. Wholesale and retail competition are the only structural pairings that have elicited substantial shifts in demand in response to price signals, because they align the incentives of retailers and end-users to reduce consumption during high price periods.
- Markets induce lower-cost environmental compliance and better environmental lobbying behavior. Restructuring reoriented the incentives to influence and comply with public policy. Notably, competitive enterprises pursue more innovative, lower-cost compliance pathways that tend to deepen abatement. Monopoly utilities have a track record of lobbying for higher cost environmental laws. For example, monopolies have a preference for command-and-control regulation that pads their rate base, and have opposed market-based policies like the 1990 Clean Air Act amendments.
Electric cost increases are multifaceted, prompting many misdiagnoses that blame markets for non-market problems. Utilities have begun pushing campaigns in restructured states to revert back to CoS regulation, whereas the growing consumer segment – namely data centers and industrials – are organizing campaigns to expand consumer choice. Independent economic assessments warn against a return to CoS regulation, and instead encourage state regulators to implement restructuring better. This includes better market design, consumer exposure to wholesale prices, and effective coordination with transmission investment.
T&D costs, generally, are the core driver of electricity cost pressures nationwide. Over the last two decades, utility capital spending on distribution has increased 2.5 times while nearly tripling for transmission. This reflects profound flaws in CoS regulation of T&D, resulting in overinvestment in inefficient infrastructure and underinvestment in cost-effective infrastructure. This projects to worsen, given T&D expansion needed to meet grid reliability criteria as a result of aging infrastructure, turnover in the generation fleet, and load growth.
T&D expansion is also central to abatement. Even partial transmission reforms can reduce carbon dioxide emissions by hundreds of million of tons per year. This explains why progressives have made reforms that expand transmission a top priority. This needs to be reconciled with the cost concerns of consumers and conservatives to result in durable policy. Consumers and conservatives have a budding transmission agenda rooted in upgrading the existing system, removing barriers to voluntary transmission development, using sound economic practices for mandatorily planned transmission, streamlined permitting and siting, and improved governance. A particularly promising frontier is reforms to enhance the existing system, given the expedience of their cost relief and consistency with a Trump administration directive.
Recent federal regulatory actions have demonstrated bipartisan willingness to improve transmission policy and the related issue of interconnection, which has emerged as a major cost and emissions issue. In 2023, FERC passed Order 2023 on a bipartisan basis to reduce barriers to new power plants trying to interconnect to regional transmission systems. Subsequent reforms were motivated by a coalition of consumer groups and the center-right R Street Institute. In 2024, FERC passed Order 1920-A on a bipartisan basis to improve economic practices in regional transmission development. EPRA, a gamechanger for interregional transmission development, passed the Senate with bipartisan support in 2024.
Demand growth has sparked reliability concerns over tight supply margins and recently put upward pressure on wholesale market prices. However, states with the greatest price decreases typically had increasing demand from 2019 to 2024 (Figure 3). This shows the importance of infrastructure utilization on electric rate pressures, as many areas had supply slack previously. The past may not be prologue. Emerging conditions show supply-constrained scenarios where marginal generation and T&D costs increase steeply to meet new load increase. The Energy Information Administration observes steady retail price increases and projects further rises to exceed inflation.
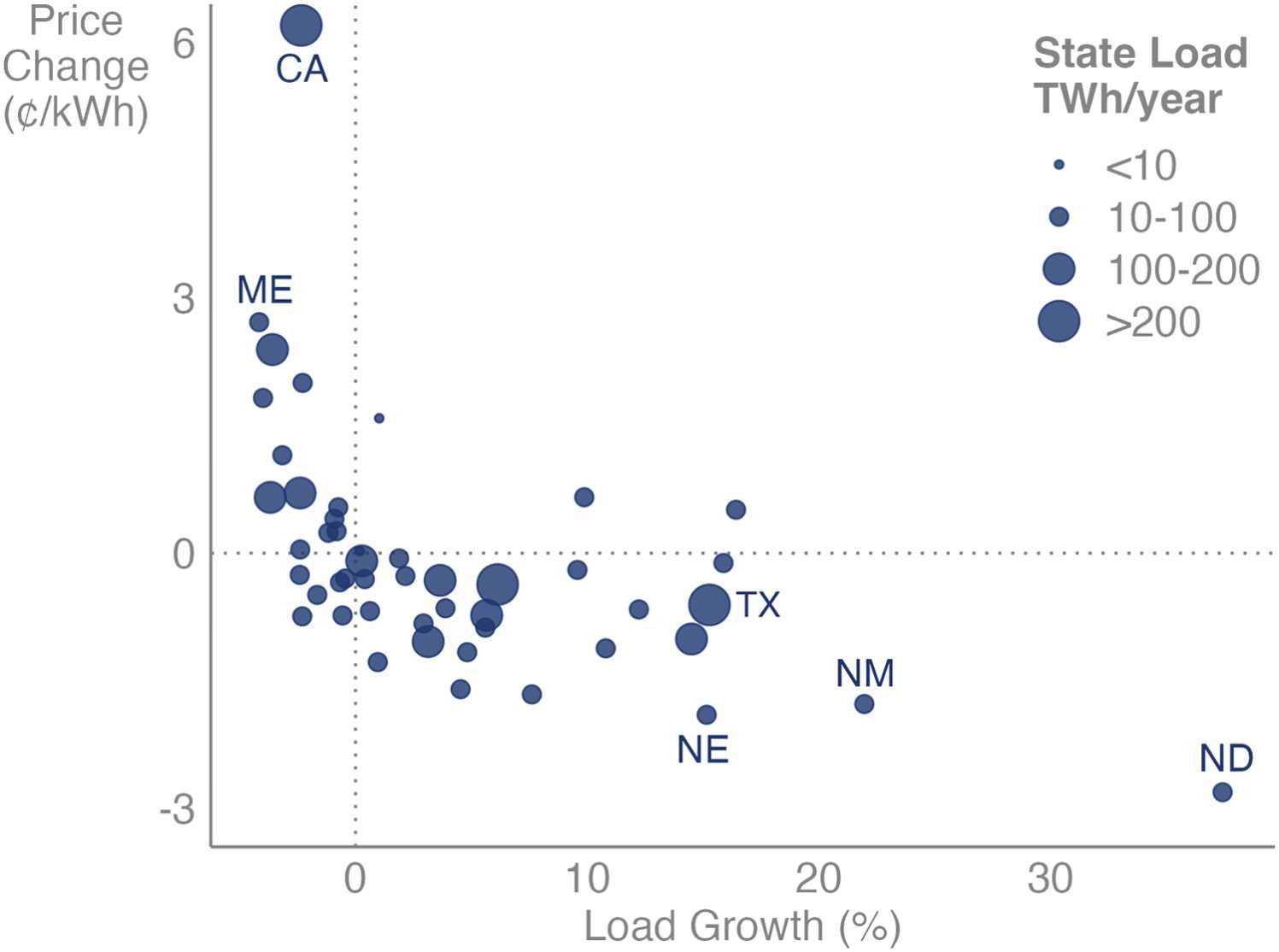
Source: Wiser et al., 2025.
In an era of resurgent power demand growth, the states poised to keep rates and emissions down have wholesale competition, retail competition, efficient generator interconnection processes, economical T&D practices, and low permitting and siting barriers. The only state that reasonably accomplishes all of these is Texas, which is experiencing the most commercial interest among competitive suppliers and growing power consumers. Texas has experienced industry-leading clean energy investment and earned the distinction of Newsweek’s “greenest state” in 2024.
All aforementioned electric reforms are considered class I policy. Despite cost-reduction appeal, power industry reforms have proven challenging for two reasons. First, reforms are highly technical in nature and face limited state capacity among legislative advisors and technocratic agencies, namely PSCs and FERC. For example, recent FERC and PSC activities reveal that these entities do not have the bandwidth or expertise to properly implement existing transmission policy, much less reform it. Secondly, reforms face strong resistance from incumbent utilities who hold concentrated interests in the status quo, creating a strong lobbying incentive. By contrast, the beneficiaries of reform, especially consumers, are dispersed interests that do not organize as effectively as a lobbying force.
Although the Texas electricity experiment and associated federal power market reforms under President George W. Bush is a conservative legacy, most restructured states are progressive. This reflects significant bipartisan historic appeal. However, traditional conservatives have sometimes conflated pro-utility positions as the “pro-business” position, while it is unclear whether right-wing populist influences will catalyze pro-market reforms by challenging the status quo or retrench monopoly utility interests based on technocratic market skepticism (e.g., Project 2025). CoS utilities also commonly oppose cost-effective T&D reform, especially vertically-integrated utilities, which is consistent with their financial incentives to expand rate base and deter lower-cost imports from third parties. Nonetheless, the political economy of bipartisan electric regulatory reform remains promising, given voters’ prioritization of reducing electricity costs.
Public Spending
Government spending occurs through direct spending outlays or indirect spending through tax expenditures. Spending takes the form of industrial policy or innovation policy. The economics literature is historically critical of industrial policy, while positive literature on industrial policy usually conflates it with innovation policy. A distinguishing element is that innovation policy selects policy instruments suited to specific market failures, namely the positive externalities of knowledge spillovers and learning-by-doing. These generally apply to research and development (R&D) and early stage technologies, including those in demonstration stage and infant industries that have not achieved economies of scale.
Predictably, progressives have been consistent backers of robust innovation policy, while conservatives typically scrutinize such expenses closely. Although differences of opinion exist on optimal funding levels, historically conservatives and progressives have agreed on a role for the government in supporting R&D. There is also a history of good governance agreement, such as a joint project between the Center for American Progress and the Heritage Foundation in 2013 on improving the performance of the national lab system. Improving outcomes-based Department of Energy program performance may have broad appeal, including better performance metrics, stronger linkages to private sector needs, and program reevaluation to determine government investment phase-out. Improvements to state capacity are paramount in this regard.
Conservatives are often critical of public spending on infant industry, where government failure can outweigh market failure. For example, policymakers often struggle to identify when to end industry support, while industry engages in rent-maintenance behavior even after it has achieved maturity. Historic evidence indicates that direct subsidies and tax exemptions for infant energy industry continue well after the targeted technologies mature. Conservative and progressive scholars have historically framed the merits over subsidies for infant industry as a debate over government versus market failure.
Since innovation policy targets non-climate market failures (e.g., knowledge spillovers) it may have a high static abatement cost. However, it is an inexpensive abatement policy when accounting for dynamic effects, because of induced innovation and learning-by-doing. Importantly, innovation policy holds massive climate benefits, because achieving abatement cost parity between clean and emitting resources is central to clean technology market adoption. Efficient R&D policy can be classified as class I policy, because the upfront cost of the policy is outweighed by long-term cost savings. Demonstration and infant industry support falls into class II-III range, depending on its implementation, and often exhibits substantial durability.
In recent years, climate-minded conservatives have shown stronger inclinations of public spending for innovation policy. However, there is a stark difference between conservatives and right-wing populism on innovation policy. Conservatives note that the adverse consequences of Department of Government Efficiency’s “gutted, ineffective government” approach to the Department of Energy is inconsistent with limited, effective government practice. The economic self-interest benefits of innovation policy may induce a course-correction with MAGA, which has not deliberately targeted innovation policy insomuch as sacrificing it amid a rash government downsizing exercise.
In contrast to innovation policy, industrial policy aims to directly promote a given industry, typically using mature technology, with interventions untethered to any underlying market failure (e.g., negative emissions externality). This generally takes the form of public spending on mature industries. For decades, traditional conservatives and climate-minded conservative scholars have been critical of green industrial policy for carrying high costs with modest emissions reductions.
The most relevant case study in climate industrial policy versus innovation policy is the Inflation Reduction Act (IRA) of 2022. IRA represented the “largest federal response to climate change to date.” It consisted mostly of subsidies for mature technologies, especially wind, solar, and electric vehicles (EVs). It also contained subsidies for infant industry. IRA was passed exclusively by Democrats, with Republicans voicing concerns over its cost. Republicans then passed the One Big Beautiful Big Act (OBBBA) in 2025, which phased-out subsidies for mature technologies, but generally retained those for infant industry. This underscores the political durability of innovation policy and the fragility of industrial policy.
A broader debrief on IRA and OBBBA reveals:
- Disregard for cost considerations preceded passage of the IRA. All known ex ante modeling of IRA’s abatement benefits before it passed ignored costs. This left Congress unequipped to weigh the merits and tradeoffs of the policy. A simplistic abatement cost technique in 2022 yielded a cost of $72/tonne for the renewable energy subsidies. A more sophisticated modeling exercise in 2023 projected an average abatement cost of $83/tonne. IRA could have been identified as a high abatement cost policy (class IV) before it passed. Before passage, R Street Institute analysis suggested meager additionality from subsidies and identified permitting and electric regulation flaws as the determining factors of energy emissions trajectories, yet Congress neglected those reforms.
- IRA abatement cost estimates escalated sharply after passage. The total abatement cost of IRA subsidies to taxpayers rose from $336/tonne in 2024 to $600/tonne in 2025. The initial 2022 IRA renewables subsidy cost estimate of $72/tonne rose to $142/tonne in 2024 and $208/tonne in 2025. The EV subsidy came in at $1,626/tonne. It is possible that this is understated, since the direction of the emissions effect of EV subsidies may depend on recipient qualifications, especially when accounting for the behavioral tendencies of EV adopters. The subsidies also undermined developer cost reduction in two ways: 1) motivated development in the least efficient areas and 2) weakened incentives for innovation that lowers costs, which translates into long-term cost increases relative to an unsubsidized baseline.
- Government failure precluded most of the anticipated climate benefits of the IRA. IRA abatement was overstated in 2022, because models understated artificial constraints on the core abatement driver: wind and solar deployment. The Energy Information Administration’s renewables projections in 2025, which reflected IRA subsidies, were close to their no-IRA estimates from 2022. Risk, not cost, has consistently been the barrier to wind and solar. A Brookings Institution analysis found that artificial barriers to entry were the leading causes of wind and solar project cancellations from 2016-2023, whereas the lowest cause was “lack of funding.” Renewables subsidies primarily constituted a wealth transfer from taxpayers to suppliers. One analysis suggested 80-90 percent of clean energy backed by the IRA would have occurred anyways. An S&P Global forecast projected OBBBA to cause a 15 percent decline in wind, solar, and battery storage capacity by 2035.
- Wind, solar, and EV tax credit phaseouts should lower costs and increase economic productivity, despite increasing electricity prices. Price and cost are related, but not the same thing. The phase-out of subsidies under OBBBA will put upward pressure on electricity prices. However, it will likely lower costs by restoring dynamic cost management incentives and removing distortions so investment reflects economic fundamentals. Electricity subsidies shift cost burdens from power generators and ratepayers to taxpayers. Because taxpayer funding is expensive – tax collection imposes considerable deadweight loss on the economy – the net effect of taxpayer subsidies tends to shrink economic output. The Tax Foundation projected that IRA would reduce U.S. gross domestic product by 0.2 percent, while OBBBA would increase long-run GDP by 1.2 percent, granted energy tax credits were only one factor in these analyses.
The takeaway from IRA and OBBBA is that subsidies for mature technologies are high cost, likely to erode social welfare, and not politically durable. Efficient public spending for RD&D, however, enhances social welfare and falls in the Overton Window due to its value for economic self-interest. Late-stage infant industry is at the fringe of the Overton Window. It is the area where conservative and progressive scholars have historically had contrasting views on whether market failure outweighs government failure, yet political outcomes have largely supported infant industry.
Generally, the literature finds strong evidence of opportunity cost neglect in public policy, which “creates artificially high demand for public spending.” The IRA was a case-in-point. Meanwhile, the opportunity cost of public spending is rapidly rising given the dire fiscal trajectory of the United States. In 2025, moderate experts emphasized a pivot away from unsustainable and ineffective “Green New Deal thinking” for clean technology subsidies in favor of an innovation-driven strategy.
Takeaways
This analysis finds chronic flaws of cost considerations in ex ante policy analysis. Many medium and high-cost policies have passed without any robust accounting of costs at all (e.g., IRA, fuel bans). Interventions with cost-benefit analysis have had a tendency to underestimate costs (e.g., regulation). These flaws contribute to public misconception and play into political economy dynamics that tend to incent policies with hidden costs over those with transparent ones.
High-cost policies have typically only been enacted by progressive governments and have come under greater scrutiny as energy costs escalate. This calls their social welfare effects and durability into question. It has cast climate action in the public eye as requiring deep economic sacrifice.
Conservatives have been hesitant to engage on climate policy outright, largely over dire economic tradeoff perceptions. Such concerns have instigated a conservative backlash to climate policy, including to policies that are compatible with U.S. economic interests. This has been exacerbated by right-wing populism, which often strays from limited government conservatism in pursuit of cultural identity objectives. For example, in a 2024 piece promoting energy affordability, the Heritage Foundation correctly attributed cost increases to renewable energy mandates, but incorrectly presumed that a broad shift towards renewable energy and away from fossil fuels would always increase costs.
High abatement cost policies not only risk reducing aggregate social welfare, but they create distributional concerns. Policies that raise energy costs tend to be regressive. This has challenged the social justice narrative of progressives, prompting a rethink by progressive leaders to take a “cost-first approach to [the] clean energy transition.” Although subsidies are a common response to lower burdens on low-income households, the most popular green subsidies pursued have exacerbated distributional concerns. Specifically, renewables subsidies favored by progressives have been challenged by conservatives as “green corporate welfare.” Progressives have also faced criticism for EV tax credits for disproportionately benefiting wealthy households.
Encouragingly, negative- and low-cost policies comprise a rising share of the abatement curve. The Overton Window for pursuing such policies has grown remarkably for “abundance progressives” and conventional conservatives. However, populist subsets within both movements challenge the potential for political alignment. Enacting negative-cost policies also faces the collection active problem of dispersed beneficiaries versus a concentrated incumbent supplier lobby favoring the status quo. Mobilizing consumer and taxpayer groups is an underappreciated strategy to enact these policies.
This analysis is far from comprehensive. A notable omission from this paper is transportation policy, the largest GHG sector in the U.S. A scan of the transportation literature underscores major abatement potential for negative and low-cost policies, including reducing government barriers to efficient heavy-duty transportation like railways, shipping, and heavier trucking. Further, the electrification of transportation requires extensive fixes to government failure, such as liberalizing markets to enable competitive charging infrastructure, which lowers costs. The merits of innovation and GHG transparency policy, previously discussed, also appear to hold promise for transportation applications such as aviation fuel. The transportation sector has also been the target of GHG regulation, mostly in progressive states, which warrants close assessment of costs. For example, one study identified a vast abatement cost range for fuel standards ($60-$2,272/tonne).
A shortcoming of this analysis is that it only characterizes costs by their efficiency (i.e., $/ton). Political decisions are highly sensitive to aggregate cost and its visibility to the public, which our taxonomy does not characterize. It is possible that efficient, transparent, and higher aggregate cost policies (e.g., C&T) fare less favorably in some political settings than inefficient, opaque, and sometimes lower aggregate cost policies (e.g., RPS solar carveouts).
Despite the limitations of this analysis, the sample of policies evaluated is sufficient to support the thesis. That is, a retooled climate policy agenda that prioritizes cost considerations should elevate social welfare and achieve greater abatement by selecting more durable policies.
Conclusion
Abatement costs have huge bearing on whether climate policies benefit society, their likelihood of passage, and whether they prove politically durable. Most abatement need not come from dedicated climate policy, per se, but rather sound economic policy that carries deep climate co-benefits. Chronic disregard for cost considerations has led to an overselection of high-cost policies and underpursuit of low- and negative-cost policies. This has undermined policy durability and exacerbated political polarization over climate change abatement.
This paper finds extensive abatement opportunities within negative-cost policies. These largely constitute fixes to government failure and include permitting, siting, and power regulation reforms. This analysis also finds considerable low-cost policies that are compatible with U.S. economic self-interests. These policies primarily spur voluntary private sector abatement through efficient innovation policy and GHG transparency.
We offer three sets of recommendations moving forward for influencers of the climate policy agenda:
- Focus on results. Climate change abatement is a function of global GHG concentrations. Too much attention pursues symbolic objectives, like preventing fossil fuel infrastructure. This tends to undermine abatement goals and impose high costs.
- Emphasize cost considerations in policy agenda setting, formulation, and maintenance. Negative abatement cost policies should take top priority, with an emphasis on mobilizing beneficiaries. Robust cost-benefit analyses should precede all cost-additive policies and be reconducted periodically to guide policy adjustments.
- Prioritize quality state capacity. The net benefits of abatement policies are sensitive to government capacity and performance. Public management is in great jeopardy in an era of institutional decay. Negative-cost policies are often highly technocratic and require sufficient staffing expertise and accountable management at public institutions like DOE, FERC, PSCs, and permitting and siting agencies.
In an era of energy affordability precedence, a reset climate agenda should anchor itself in good policy basics. That is, a sober-minded return to results-driven, net-benefits prioritized policy. This should improve the durability of climate policy and ensure it enhances social welfare. Executing reforms well requires a recommitment to improving the quality of institutions as much as the policy itself.
Introducing Digital Service Retros: Back to the (Digital) Future
On January 20, 2025, the U.S. Digital Service, 18F, and much of the Technology Transformation Service were disbanded or fundamentally reshaped. The institutions that once rebooted HealthCare.gov, expanded access to care for millions of Veterans, and launched Direct File were transformed overnight, marking a dramatic shift in how the federal government delivers critical services to the American people.
In parallel—governments at the state and local levels have made landmark investments in digital teams and innovation, which has already generated real results and cost savings.
This is not the first disruption in public-sector digital capacity. But the scale of this moment, colliding with rapid advances in AI, new procurement models, and evolving expectations of government, creates a rare opportunity. It is a moment to look back in order to build for the future. To pause, together, as a community, and ask what we’ve learned—and what comes next.
The Federation of American Scientists, in partnership with Georgetown University’s Beeck Center for Social Impact + Innovation and the Better Government Lab at Georgetown University and the University of Michigan, is launching a national series of digital service retrospectives. These convenings will capture hard-won lessons, surface what truly worked, be clear-eyed about what didn’t, and bring digital service experts together to imagine next-generation models for digital government.
How might we redesign digital service capacity—its operating models, authorities, and talent—based on over a decade of progress in civic technology? What drew you to this work? What accelerated impact, and what slowed it down? What was missing? What was overbuilt? What made partnerships and deployments succeed—or fail?
We are inviting participation from across the U.S. digital government ecosystem: current staff and alumni of USDS, 18F, and TTS, digital teams across federal agencies, states, and cities, and the lawyers, procurement and talent specialists, data leaders, congressional staff, and policy experts who worked alongside them. There are lessons here that must be captured and shared.
Through a series of virtual and in-person workshops, participants will share experiences, ideas, and aspirations. At each session, we will synthesize what we hear, ultimately building toward a public set of insights and recommendations for the future of digital capacity in government. From there, we will take these recommendations to policy makers on the Hill to inform future legislation, executive branch champions, as well as to state and local leaders across the country to see which ideas and concepts they can start piloting now. This is policy entrepreneurship—building innovative ideas and bring them to life with key partners and talent—is what FAS does well and, with Beeck and BGL, we look forward to fighting for your ideas.
We have some great partners: we’re building on work already underway through the Federal Civic Tech Exit Project, run by the Better Government Lab and the Beeck Center, which has already conducted in-depth interviews with nearly 50 former federal digital service professionals. This next phase expands the contributions of the Beeck Center and BGL, drawing on Beeck’s national network of state and local digital service leaders and BGL’s focus on identifying and putting the world’s best research into practice to improve how government functions.
The work begins soon. If you’re interested, please complete this interest form and you’ll hear from us.
Start by expressing your interest in the form. You’ll be able to choose one or more ways to engage:
- Join a virtual workshop on February 10, 12, or 25 (register online)
- Attend an in-person workshop in DC on March 3 or 4 (register online)
- Contribute through an open-ended, anonymous survey
- Refer a colleague or friend who should be part of this conversation
- Follow along for updates, insights, and announcements
This initiative is hosted by the Federation of American Scientists (FAS) and Merici Vinton, with support from the FAS Government Capacity team, led by Loren DeJonge Schulman and Leya Mohsin.
We are launching this work in partnership with Georgetown University’s Beeck Center for Social Impact + Innovation, leveraging its extensive relationships with state and local digital leaders and the 10,000+ practitioners that participate in its Digital Government Network and the Better Government Lab at Georgetown University and the University of Michigan. We are also drawing on a small group of trusted advisors from across the digital government community.
- We will protect your identity. Our goal is to surface and publish the best ideas, not attribute individual comments.
- We intend to synthesize what we learn and share it with federal leaders, congressional staff, state and local digital teams, and future candidates and appointees. Participants who are excited to help shape, champion, or implement next-generation digital service models will have clear opportunities to engage in what comes next.
- Anyone who is or has been part of a government digital service ecosystem, or a close partner to one. This includes:
- Current or former staff of the U.S. Digital Service, 18F, or Technology Transformation Services
- Members of digital teams at federal agencies, states, and cities
- Congressional staff and policy experts who worked alongside these teams
- Partners, champions, and enablers who helped this work succeed
- If you’ve built, supported, funded, or depended on modern digital government, your perspective belongs here.
Demystifying the New President’s Management Agenda
By design, the Office of Management and Budget’s (OMB) work follows a predictable, seasonal rhythm: budget guidance to agencies in the spring, strategic management reviews in the late summer, passback in the fall, shutdown saber-rattling in late September, release of the president’s budget request in the winter, and so on. A giant novelty clock in the building counts down the days until the end of the fiscal year, each year, whether Congress has done its work to appropriate money for the next one or not. Presidents, Congresses, crises, political movements – all of these come and go, but OMB’s work largely continues to cycle.
This week, OMB completed one such ritual: it released the President’s Management Agenda (PMA). The PMA–closely watched by federal employee groups, contractors, public administration academics, and the handful of general-public bureaucracy-enjoyers–is the vehicle with which each president outlines policy priorities on how the government manages itself. Each 21st-century president has had one, after George W. Bush’s Administration issued the very first one in August of 2001–and President Trump is the first to have issued two discrete ones.
Not familiar with this ritual? You’re not alone. Though not statutorily required, a PMA is meant to be a blueprint for improving how the federal government delivers policy, whether hiring, buying, designing services, listening to Americans, measuring performance, or delivering financial assistance. A PMA is also load-bearing, one of the few levers capable of coordinating action across the enormous machinery of government, aligning budgets, capacity, and accountability behind long-term modernization rather than the short-term crisis response that often drives management changes.
In a year when management issues like human capital, IT modernization, and improper payments have received greater attention from the public, examining this PMA tells us a lot about where the Administration’s policy is going to be focused through its last three years. As we did for a major policy release on hiring earlier this year, the Federation of American Scientists and the Niskanen Center are teaming up to break down and contextualize this year’s PMA.
The Structure of the PMA
As OMB noted in an accompanying memo to this PMA release, the core of the PMA has for many years, been a set of cross-cutting “priority goals” that OMB is required to establish under the Government Performance and Results Act Modernization Act (GPRAMA) of 2010, which codified much of what the Bush and Obama Administrations had done to focus on performance-based goal setting and reporting. Over the years, the PMA has grown to be the organizing principle for these priority goals, explaining how they relate to one another and are part of a broader coherent whole.
This current iteration of the PMA (reproduced below) is organized – like the Biden Administration’s was – as something of a nesting doll. It has three broad priorities, each with a few goals, and a series of objectives within each of those goals:
Unlike previous iterations of the PMA, it appears this new one won’t be accompanied by the type of long narratives and explanations typical of the Bush, Trump I, and Biden PMAs. It also differs somewhat from the Obama Administration’s approach, which focused on a series of detailed “Cross-Agency Priority (CAP) Goals that largely cohered into a formal PMA after the fact as GPRAMA was passed during the term and codified the modern process mid-stream.
Regardless of how they start, however, previous administrations have largely committed to providing ongoing reporting on their progress towards achieving each objective or goal throughout the remainder of the term. It is not yet clear whether the second Trump Administration intends to do this–Congress should inquire about their GPRAMA obligations–but in general this practice has been valuable both to keep agencies accountable for making progress and so that interested third parties can get a window into how the government is changing over time.
In the meantime, this week’s release gives us enough insight into the contours of this term’s PMA to assess how it compares with previous efforts and with what we’ve learned from observing and managing past PMAs.
What’s Promising: A Renewed Focus on Some Hard Problems
Normally, the PMA contains two types of initiatives. The first are evergreen topics —such as the perennial need to hire federal employees more quickly and efficiently—which have appeared in every PMA to date. The second category consists of more idiosyncratic or extremely timely “hard problems” that either haven’t received attention or where past reform has stalled. In the Biden PMA, for instance, this included integrating lessons from the pandemic’s disruption of work life. In the first Trump Administration, it included an ambitious overhaul of personnel vetting transformation on the heels of the massive OPM security clearance data breach in 2015.
Occasionally, these hard problems “graduate” out of the PMA once sustained focus produces results. The PMA’s emphasis on personnel vetting, for example, has largely given way to a multi-year, bipartisan Trusted Workforce 2.0 strategy that has and is making progress despite its challenges.
This year’s PMA includes several such issues, offering the second Trump Administration an opportunity to spotlight underappreciated but consequential aspects of federal management, including:
- Offloading unnecessary leases and buildings: Federal facilities and real estate have never truly been managed as a portfolio with all the transparency, tradeoffs, accountability and management that entails. Before the pandemic, many agencies had significant excess office space and struggled to offload unneeded square footage, even as the average age of federal facilities climbed north of 50 years old and many buildings are no longer suitable for modern work. Rationalizing and right-sizing this portfolio is a worthy and important initiative but it will be difficult: Congress has historically underfunded agencies that are aiming to reconfigure or move, and individual members of Congress frequently oppose specific office closures among their constituents. Any effort to responsibly modernize these real estate holdings will take a lot of patience and willingness to take on sacred cows, but has the potential to earn significant savings and efficiencies.
- Holding contractors and grantees accountable for performance: Most indirect federal spending flows through intermediaries and, too often, the outcomes agencies define for their work are unclear, don’t meet intent, cost more than they should, or aren’t set up for other stakeholders to learn from. Many agencies are captured technologically, intellectually, and psychologically by vendors, leading to a type of learned helplessness where their inability to technically manage contracts leads to an inability to hold them accountable for their performance. Fighting these entrenched forces and inertia is not easy, however, and will require arming agencies with the federal experts, tools and training necessary to change their approach to vendor and grantee management but also give them top-cover to push back on powerful, politically-connected awardees that fail to deliver again and again without consequence.
- Eliminating data silos: While data protections necessarily inhibit privacy and security violations, too much federal data sits in silos built by habit, culture, or old technology. Driving responsible interoperability could have a meaningful impact on service delivery, including for two of the thorniest issues in public service delivery: identity regulation and eligibility verification. However, prior actions and whistleblower complaints about misuse of personal citizen data put an imperative on the Administration demonstrating its commitment to data security under this PMA initiative. It presents an opportunity to right the ship and build the type of trust that will be required from Congress and the public to make good on the transformative power of better data management.
- Removing poor performers: The federal government has long struggled to swiftly remove poor-performing employees. The system we have today was never intended to be permanent or perfect—it was meant to provide incremental improvements toward processing removals quickly but fairly. Nearly every former deputy secretary, in administrations of both parties, has wished they could establish a simple, actionable, repeatable framework for performance management that includes reasonable safeguards. This Administration has an opportunity to chart that path. But proceeding without those safeguards—particularly protections against arbitrary or partisan dismissals—risks undermining good-faith reforms that are crucial for cross-partisan credibility and for helping managers manage well.
- Building the most agile and efficient procurement system: The Revolutionary FAR overhaul underway at OMB and the General Services Administration (GSA) is a concrete opportunity to modernize federal buying at its foundations by paring back the FAR to just its “statutory” requirements and allowing agencies to buy more flexibly. But the regulation update is at best only half the battle: the administration will need to dedicate time, people, and championship to making them stick in training, norms, culture, and leadership. It also needs to resist the temptation to add back its own non-statutory clauses, an impulse that led to the FAR’s bloated and unwieldy state in the first place.
Ideally, success in these areas means they will eventually fade into the background of standard management practice. Agency leaders may not earn themselves splashy press coverage or public adulation by improving procurement or tackling data silos. No agency head wants to spend time grappling with underutilized buildings. Genuine progress here, however, would allow future leaders to remain focused on mission delivery.
What’s Returning: Places to Learn from the Past
This brings us to the evergreen PMA topics. To GPRA veterans, some of the things in here are expected and represent the evolution of years of work by Republicans, Democrats, and nonpartisan civil servants to make the government run better. Many of these reflect years–or even decades–of work to address some of the core challenges of managing a large organization in any sector (how to hire the right people, how to buy effectively, how to build and secure systems, etc.)
But there’s a deeper reason these issues recur, beyond aspirations for bipartisan comity. Adding an item to the management agenda is only a starting point. Meaningful progress requires far more than a talking point, executive order, or regulatory tweak. Leadership attention and cover, technical capacity to actually understand, teach, and monitor reform, oversight partnerships that orient their activities to the new model, administrative data that’s accurate, real-time, and actionable, and central funds to resource pilots too edgy to get agency support or toolkits that no one agency wants to own.
In this PMA, some of these evergreen topics include ones this Administration can learn from its predecessors and accelerate towards success, including:
- Tackling improper payments, fraud, waste, and abuse: The Trump Administration inherits a solid foundation in this area from its predecessor, which invested serious effort into tackling the surge in improper payments in the COVID-19 era. That work included investing in upfront controls, fraud prevention, and collaboration between agencies and their oversight communities. The Government Accountability Office, Agency Inspectors General, and others have also long offered suggestions about how to continue to reduce the government’s improper payments rate. Groups like the Payment Integrity Alliance are developing new technology-powered tools to support this work from outside government. These are evidence-based solutions that are likely to work, as opposed to arbitrary, highly-partisan, and ultimately untrue declarations of fraud that marked the early days of this Administration, in addition to counterproductive efforts to cut or constrain the oversight community. As OMB looks towards 2026, it should take into account these models.
- Streamlining the federal workforce and eliminating duplicative programs: While this year’s efforts are the first in a couple decades to seek to dramatically reduce the size of the federal workforce, they are not without precedence in American history. Following both World Wars (and especially through the late 1940s), the federal government had to demobilize hundreds of thousands or millions of civilian employees in a way that both treated them with dignity and economized on taxpayer dollars. More recently, in the 1990s, the Clinton Administration also conducted large-scale downsizing, with decidedly mixed results because the cuts came before changes to agency to-do lists that never materialized. It will be important for this Administration to learn lessons from the past to avoid some of the long-term damage wrought by the Clinton years, for which agencies are still paying.
- Hiring exceptional talent for key presidential priorities based on skills and merit: All presidents have priorities and many of those involve some kind of hiring surge: following 9/11, the Bush Administration had to rapidly create and staff up the Department of Homeland Security for new mission sets–for example, like airport security. More recently, the Biden Administration conducted several surges around topics like the Bipartisan Infrastructure Law and artificial intelligence. To make this work, previous efforts have succeeded by setting up dedicated teams that focused on specific, measurable goals and bought-in mission area leadership to champion the effort. As OMB and OPM consider their efforts this time, they should explore common data standards to ID bottlenecks, interagency approaches to share resources and talent, and investing in all the accoutrement to new and updated career paths and roles – and doing their best to embed these practices in the system, not just as part of a special effort.
They might also consider reactivating networks and programs that were successful in previous eras, like Tech to Gov, which worked across sectors to hire technologists into government. On merit and skills based hiring, implementation appears to be under way with a variety of initiatives that have promising goals, but will require significant investment of resources and leadership attention to complete, as we’ve written about.
- Buy as one entity: smarter, faster, cheaper: Successive administrations, dating back several decades, have tried to strike the right balance between decentralized and centralized procurement. The Clinton team, for example, called for greater decentralization to agencies because it “allows strangers-often thousands of miles away-to make purchasing decisions.” More recently, however, administrations have gone in the other direction, including a discrete goal to drive category management in the first Trump PMA, though agencies often still complain about being forced to use government-wide vehicles that don’t meet their exact custom needs.
To avoid the pendulum swinging back and forth between centralization and decentralization, efforts to implement this PMA should learn from efforts to achieve savings by transparent use of procurement data that were pioneered in the Biden Administration like the Procurement Co-pilot, Hi-Def initiative, and the strategic acquisition data framework. Rather than mandates from above, these initiatives help drive savings and get “spend under management” by solving information asymmetries and transparently helping agencies understand “what’s in it for them” when they use best-in-class contracts.
- Consolidate and standardize systems, while eliminating duplicative ones: The federal government has long operated on a system of both shared, government-wide, and also bespoke agency systems. The Bush, Obama, and first Trump administrations had OMB focusing on consolidating duplicative systems across government through shared services. This model, while promising in many cases, is difficult to pull off in practice – of those initiatives, the Bush Administration’s payroll consolidation is far and away the most successful, while efforts to adopt standard payment system (e.g., e- and g-invoicing) and innovative payroll solution have languished, as did GSA’s NewPay program.
This PMA should take to heart the lessons of its predecessors: agencies must be resourced up front to execute their part of any migration to shared systems, and OMB must ruthlessly prioritize and rigorously validate any requests for deviations from the standard product. In most cases, it will be far easier—and considerably cheaper—to adjust policy to fit a modern, standard solution than to customize that solution to accommodate every agency’s unique requirements.
Leaders should also address the internal politics of these transitions directly. Champions of bespoke systems often have deep attachment to their legacy tools, and their resistance can be stronger and more personal than expected.
- Defend against and persistently combat cyber enemies: Reactive and proactive cybersecurity has been a central federal government focus as long as government systems have been connected to the internet. Of all the discussed areas, continuity is perhaps most crucial to cybersecurity, with the need for sustained attention to legacy system replacement, identity management, continuous monitoring, secure architectures, and the significant talent demands that come with all of those. This Administration should heed the lessons of its predecessors, which lost valuable time to bureaucratic reshuffling and inconsistent “carrot vs. stick” approaches in its engagement with the private sector.
It’s never going to be possible to truly “solve” these issues that are core parts of ongoing management in any large enterprise. However, because progress is incremental, this PMA can accelerate its own impact by learning from what has and hasn’t worked in the past.
What’s Missing: Outcomes for Americans
There is, however, one “evergreen” PMA topic that we’re surprised to see missing from this iteration: Customer Experience (CX).
The previous two PMAs featured big customer experience pushes to modernize and centralize how the government designs, delivers, and updates benefits based on customer needs. These delivered favorable results for veterans’ benefits, disaster survivors, new families, travelers and more, and fostered innovative approaches to benefits delivery like the cross-agency “life experience” program that reconceptualizes the way the government engages with people who need its support. In recent years, the bipartisan success of these initiatives has led to four straight years of improvements in the industry-standard American Consumer Satisfaction Index, with the government closing out last fiscal year at an impressive 19-year high.
While this PMA does mention “digital-first services” that are “built for real people, not bureaucracy,” that principle sits inside a technology-and-efficiency frame rather than a clear commitment to outcomes for the public. What’s missing is an explicit stance that service delivery, burden reduction, and trust-building are core measures of government performance and are not encompassed by a positive government IT experience or a more fetching website design. Plenty of core users of government services–seniors, for example–do not interface with the government in a “digital-first” way, further complicating this as a focus for customer experience.
Hopefully this absence will still allow for the bipartisan CX agenda to continue in other spaces, such as the new National Design Studio. It’s not enough to declare that the government will deliver high-quality services to the people who rely on them. Agencies need the ability to collaborate and know that the White House will back them when they need to request incremental funding to conduct user research or A/B test a new form before rolling out.
A real test of any PMA isn’t how well it modernizes, it’s whether people notice government working better on their behalf. In that way, CX is what we might call the “love language of democracy” and it’s important that OMB is attentive to building that.
What’s Concerning: The Culture War is Coming for Management
The Biden Administration received criticism for attaching progressive goals from environmental standards to equity to labor onto every possible management tool (procurement, grantmaking) until the weight of implementation is slow, diffuse, or nearly impossible. Its PMA embodied that instinct: broad, values-aligned expansive goals that had great intentions but struggled to operationalize.
The new PMA both reacts against and mirrors that instinct: it pairs standard management reforms with culture-war directives that seek single-minded discipline, accountability, and ideological alignment.
At times, it reads like two agendas stitched together: one technocratic, aimed at federal administrators, and one ideological, aimed at unofficial commissars and social media. Alongside modernization goals you might find in any PMA sit directives to:
- Eradicate woke and weaponized programs across government, which is a sweeping slogan with unclear scope at odds with the usual evidence- and performance-based mandates embedded in GPRAMA and past PMAs.
- End discrimination by government, which is a superficially unobjectionable shibboleth, but incorrectly implies that the government has been discriminating in how it carries out its management functions, despite the fact that its equity programs largely only follow the rules Congress has set out in offering employment preference to veterans or procurement preference to certain categories of small businesses.
- Defund DEI, gender ideology, K-12 indoctrination, child mutilation, and open borders, which are culture war buzzwords with no obvious relation to government performance or management issues.
And scope creeps further into territory historically outside PMA (or OMB) control, such as a set of general goals with choose-your-own-adventure interpretation and murky implementation paths, written at a strange distance from the government the Administration oversees:
- Find and annihilate government censorship of speech, which is perhaps the first time annihilate has ended up in an OMB memo and implies that there are “hidden” examples of censorship while the administration pursues overt censorship in other areas.
- Reverse malicious schemes to hide information from Americans, which gestures at a conspiratorial approach to government management that seems at odds with the Administration’s claim that it’s fully in control of the executive branch. It’s difficult to simultaneously claim that there are truths hidden from the public while also deprecating transparency, as in Federal data sets.
- Abolish abusive intelligence activity targeting unwitting Americans, which is certainly a laudable goal for any civil libertarian in a democracy but doesn’t necessarily have any resonance with normally much-duller management functions like HR and finance, which have struggled to accomplish even their overt functions in recent years, nevermind anything more nefarious.
As we’ve written before, hijacking these normally low-temperature operational processes to fight the culture war not only raises the partisan pressure on normally bipartisan issues, but it also “needlessly politicizes our institutions, snarls our civil servants in red tape, and usually fails to achieve even those unrelated objectives.”
Nowhere is this danger greater than in implementation of the PMA’s objective to “[p]ut political appointees in control of grant process to deliver results,” which supposes that political control and, by implication, alignment with the President’s partisan priorities is a main factor in how Congressionally-authorized grants are executed. The President certainly gets to set some overall parameters for grantmaking across the federal government, and politically-appointed agency heads are ultimately accountable for the money they spend.
But this priority implicates a much more arbitrary and politically-motivated process for determining how public funds are spent that strikes at the heart of what makes government action legitimate: the fair application of rules that are defined ahead of time and apply equally to all. Like a similar requirement in the Merit Hiring Plan, this also creates an obvious bottleneck in agency processes as recommendations stack up for political review, reducing efficiency and elongating the path to “results.”
Perhaps including these initiatives–which largely fall outside of the normal OMB management purview–was the price OMB had to pay to get the rest of the PMA through the hyper-partisan (even in normal order) communications processes of the White House. If that’s the case, agencies should be able to largely proceed with the rest of the agenda unbothered by also having to separately organize around these initiatives. But if not, it will be critical to ensure that directing agencies into partisan goose chases does not pull time and attention away from the harder—and ultimately more rewarding—work of genuine management reform.
Declaration is not Implementation
Publicly releasing the PMA is the easy part. The real work goes into changing government. As the Bush Administration’s first PMA noted: “Government likes to begin things—to declare grand new programs and causes. But good beginnings are not the measure of success. What matters in the end is completion. Performance. Results. Not just making promises, but making good on promises.”
Many of the objectives outlined in the PMA are sound ideas with long track records across different administrations. We largely agree with many of them and they echo our policy priorities and those of partner organizations. But their appearances on multiple PMAs underscores how hard these problems are to solve. Category management,real property portfolio rationalization, and cybersecurity, were problems for many years because of the inherent difficulty of tackling them.. This is doubly true for the ideas that are fresh from the front lines of the culture war, which lack both a track record of successes and failures to learn from and the bipartisan support that more established issues—like improper payments or IT modernization—typically receive in Congress.
To actually impact the entire government – one of the largest and most complex enterprises in human history – it’s not enough to just declare that it’s the policy of the Administration that X or Y happens, or even convene regular gatherings of deputies. We’ve seen that approach fail repeatedly: agencies cannot and will not implement a PMA just because OMB issues it.
Real success requires disciplined implementation. That means selecting strategies that genuinely move the needle; setting aggressive but achievable measures and timelines; incentivizing leaders to invest time, attention, and talent in relentless follow-through; maintaining up-to-date metrics and feedback loops to know what’s working and what isn’t; and sustaining clarity of focus all the way to the finish.Without that, it becomes all too easy for OMB and agencies to skate by on superficial changes that check boxes but result in no real systems change–a PMA of performance art, where everyone claps but nothing changes. Amid all the swirl of any White House, this work of sticking the landing is the hardest part.
That’s because the PMA – like any strategy – itself isn’t really valuable on its own. It can, however, cut through the noise, clarify what the priorities are, and provide a framework for holding agencies and leaders accountable as they do their work. Any PMA will rise and fall based on how well it manages to do this. The way this term’s PMA is structured at the outset makes this task supremely difficult because it’s pulling in several directions all at once: it’s trying to simultaneously pass as a deeply partisan political document, a check-list for agencies of recent EOs, and a sober management policy agenda.
The real danger is that this lack of clarity and flurry of culture war buzzwords means nothing changes. That the same broken systems of human capital, procurement, IT modernization, security clearances, and user feedback, that have contributed to what OMB refers to as “accumulating perils” persist for yet another presidential term because OMB’s own management approach mistook a policy memo for progress and failed to chart a path forward. “Declare success and move on” is how these hard problems survive for decades.
This failure mode is easy to imagine: as humbling as it is to admit when you sit at OMB, reform requires changing the habits of work in agencies, sub-agencies, offices, and teams for whom policy memos about HR and procurement are the last thing on their mind (or even in their inbox). This is the hardest work of governance – rewiring workflows, seeding change in budgets, resetting culture – and demands management be treated as a core, can’t-fail function rather than a sideshow of dashboards and Powerpoint.
As they should be, agency implementers are more focused on the day-to-day administration of their programs: achieving their particular program objectives, responding to requests from Congress, serving the public, tracking their own budgets, and managing their own chaotic work lives. If the PMA can’t provide them with clarity, a limited number of clearly articulated goals, and a simple on/off ramp for change, it will be hard to change the direction of travel – not because of some deep state conspiracy, but because they don’t know what to focus on or how they’re going to be measured. What gets implemented, and what people experience, is what counts; everything else is decoration.
What We’re Watching
As with all broad, whole-of-government strategies like this, it will only be obvious in retrospect whether this administration is successful at achieving those goals. However, there are some things to watch out for that will clue close-watchers in about how things are going:
- First, will OMB continue the type of detailed, quarterly status reports that were the hallmarks of previous PMAs and allowed the public to see how things were progressing?
- Second, are there key metrics that OMB and its partner agencies will commit to tracking, reacting to, and publishing to measure their success?
- Third, are agencies resourced to actually accomplish many of these ambitious goals and what do they prioritize (and indeed, since agencies are not mentioned in the PMA itself, what ownership do agencies feel over it)?
Finally, and more abstractly, we’re also going to be looking out for how OMB and others engage with the rest of the PMA-interested community, including career federal employees, good government groups, congressional staffers, think tanks, academics, and others who have trod this same path. The permanent institutions of the federal government don’t serve any one president exclusively; instead, they represent a deep and important investment that the American people have made in themselves as a bedrock of our democracy. While reasonable disagreements about how to do so will certainly always exist, this community can, should, and will embrace a government asking for help. OMB would do well to welcome them in.
A Digital Public Infrastructure Act Should Be America’s Next Public Works Project
The U.S. once led the world in building railroads, highways, and the internet. Today, America lags in building the digital infrastructure foundation that underpins identity, payments, and data. Public Digital systems should be as essential to daily life as roads and bridges, yet America’s digital foundation is fractured and incomplete.
Digital public infrastructure (DPI) refers to a set of core and foundational digital systems like identity, payments, and data exchange that makes it easier for people, businesses, and governments to securely connect, transact, and access services.
DPI consists of interoperable, open, and secure digital systems that enable identity verification, digital payments, and data exchange across sectors. Its foundational pillars are Digital Identity, Digital Payments, and Data Exchange, which together provide the building blocks for inclusive digital governance and service delivery. DPI acts as the digital backbone of an economy, allowing citizens, governments, and businesses to interact seamlessly and securely.
America’s current digital landscape is a patchwork of systems across states, agencies and private companies, and misses an interoperability layer. This means fragmented identity verification, uneven instant payment networks, and siloed data exchange rules and mechanisms. This fragmentation not only frustrates citizens but also costs taxpayers billions, leads to inefficiency and fraud. This memo makes the case that the United States needs sweeping legislation– a Digital Public Infrastructure Act— to ensure that the nation develops a coherent, secure, and interoperable foundation for digital governance.
Challenges and Opportunities
Around the world, governments are investing in digital public infrastructure to deliver trusted, inclusive, and efficient digital services. In contrast, the United States faces a fragmented ecosystem of systems and standards. This section examines each pillar of digital public infrastructure, digital identity, digital payments, and data exchange, highlighting leading international models and what institutional and policy challenges the U.S. must address to achieve a similarly integrated approach.
Fragmented and non-interoperable Digital Identities
Digital Identity. The U.S. has no universal digital identification system. Proving who you are online often relies on a jumble of methods like scanning driver’s licenses, giving your social security number, or one-off logins. Unlike many countries with national e-ID schemes, the U.S. relies on the REAL ID law which sets higher standards for physical driver’s licenses, but it provides no digital ID or consent mechanism for online use. Just under half of U.S. states have rolled out some form of mobile driver’s license (mDL) or digital ID, and each implementation is largely unique.
Federal agencies have tried to streamline login with services like Login.gov, yet many agencies still contract separate solutions (Experian, ID.me, LexisNexis, Okta, etc.), leading to duplication. The Government Accountability Office recently found that two dozen major agencies use a mix of at least five different identity-proofing providers. The result is an identity verification landscape that is inconsistent and costly, both for users and the government.
Fragmented Digital Payment Infrastructure
Digital Payments. The United States still lags in offering universal, real-time payments accessible to all. The payments landscape is highly fragmented, with multiple systems operated by both public and private entities, each governed by distinct rule sets. The Automated Clearing House (ACH) network is the batch-based system that processes routine bank-to-bank transfers such as salaries, bill payments, and account debits or credits. It is co-run by the Federal Reserve (FedACH) and The Clearing House (EPN) under Nacha rules and settles with delay. The Real-Time Payments (RTP) network is an instant 24/7 credit-push system that moves money within seconds through a prefunded joint account at the Federal Reserve Bank of New York. It was launched by The Clearing House in 2017 and is governed by its private bank owners.
In 2023, the Federal Reserve launched FedNow, the first publicly operated real-time payment rail in the United States, offering instant settlement through banks’ Federal Reserve master accounts. Card networks such as Visa, Mastercard, Amex, and Discover continue to operate proprietary systems, while peer-to-peer platforms like Zelle, Venmo, and CashApp run closed-loop schemes that often rely on RTP for back-end settlement. Because these systems differ in ownership, governance, settlement models, and liability frameworks, they remain largely non-interoperable. A payment sent through RTP cannot be received on FedNow, and card or wallet systems do not seamlessly connect to ACH or instant payment rails.
FedNow operates as a real-time gross settlement (RTGS) infrastructure, enabling participating banks and credit unions to send and receive instant payments around the clock. Its design is infrastructure-centric: the Federal Reserve provides the back-end rail, while banks must opt in, build their own consumer interfaces, and set transaction fees and rules. The system does not define standardized public APIs, merchant QR systems, or interoperable consumer applications. These layers are left to the market. Its policy intent centers on efficiency and resilience in interbank payments rather than universal inclusion or open access.
Examples of Complete Public Payment Ecosystems
By contrast, India’s Unified Payments Interface (UPI) and Brazil’s Pix were designed as full digital public infrastructures that combine settlement, switching, and retail layers within a single public framework. Both are centrally governed, with UPI managed by the National Payments Corporation of India under Reserve Bank of India oversight and Pix managed by the Central Bank of Brazil. They enforce mandatory interoperability across all banks, wallets, and payment apps through open API standards. Their architecture integrates digital identity, authentication, and consent layers, allowing individuals and merchants to transact instantly at zero or near-zero cost.
While FedNow provides the plumbing for real-time settlement among banks, UPI and Pix function as complete public payment ecosystems built on open standards, public governance, and inclusion by design. Real-time payment systems in India (UPI), Brazil (Pix), and the United Kingdom (Faster Payments) now process far higher transaction volumes than their U.S. counterparts, reflecting how deeply these infrastructures have become embedded in daily economic activity.

Credit: fxcintel.com
This fragmented payment ecosystem became painfully apparent during COVID-19: some people waited weeks or months for stimulus and unemployment checks, while fraudsters exploited the delays. Only in 2025 did the Treasury Department finally announce it will stop issuing paper checks for most federal payments, to reduce delays, fraud, and theft.
Clearly, the U.S. needs a more cohesive approach to instant, secure payments, from Government-to-Person (G2P) benefits to Person-to-Government (P2G) tax payments and everyday Person-to-Person (P2P) transactions.
Data Exchange. Americans routinely encounter data silos and repetitive paperwork when interacting with different sectors and agencies. Each domain follows its own regulatory and technical standards. Health records are governed by the Health Insurance Portability and Accountability Act of 1996 (HIPAA) and the Trusted Exchange Framework and Common Agreement (TEFCA) established under the 21st Century Cures Act of 2016. Financial data are protected by the Gramm–Leach–Bliley Act of 1999 (GLBA) and will soon fall under the Consumer Financial Protection Bureau’s proposed Personal Financial Data Rights Rule (Section 1033, Dodd–Frank Act). Tax and education data are separately governed by the Internal Revenue Code and the Family Educational Rights and Privacy Act of 1974 (FERPA).
There is no unified, citizen-centric protocol for individuals to consentingly share their data across sectors. For example, verifying income for a mortgage, student loan, or benefits application might require three separate data pulls from the IRS or employer, each with its own process. In healthcare, TEFCA is creating a nationwide data-sharing framework but remains voluntary and limited to medical providers. In finance, Europe’s PSD2 Open Banking Directive (2018) forced banks to open consumer data via APIs, while the United States is only beginning similar steps through the CFPB’s data portability rulemaking. Overall, data-sharing rules remain sector-specific rather than citizen-centric, making it difficult to “connect the dots” across domains.
Data Protection. The United States follows a fragmented, sectoral approach to data protection rather than a single, unified framework. Health information is covered by HIPAA (1996), financial data by GLBA (1999), student records by FERPA (1974), and children’s online data by the Children’s Online Privacy Protection Act (COPPA, 1998).
States have layered on their own privacy laws, most notably the California Consumer Privacy Act (CCPA, 2018) and the California Privacy Rights Act (CPRA, 2020). At the federal level, the Federal Trade Commission (FTC) fills gaps using its authority to regulate “unfair or deceptive practices” under Section 5 of the FTC Act (15 U.S.C. §45). However, there remains no nationwide baseline for consent, portability, or deletion rights that applies uniformly across all sectors.
An illustration from 2021 by the New York Times shows the picture very well.
Credit: Dana Davis
Recent efforts in Congress, including the proposed American Data Privacy and Protection Act (ADPPA, 2022) and the American Privacy Rights Act (APRA, 2024), sought to create a comprehensive federal framework for data privacy and user rights. APRA built on ADPPA’s foundations by refining provisions related to state preemption, enforcement, and individual rights, proposing national standards for access, correction, deletion, and portability, and stronger obligations for large data holders and brokers. It also envisioned expanded enforcement powers for the FTC and state attorneys general, along with a limited private right of action.
Despite initial bipartisan attention, APRA has not secured sustained bipartisan support and remains stalled in Congress. The bill was jointly introduced in 2024 by the Republican Chair of the House Energy and Commerce Committee and the Democratic Chair of the Senate Commerce Committee, reflecting early cross-party interest. However, Democratic support weakened after language addressing civil-rights protections and algorithmic discrimination was removed, prompting several members to withdraw backing (Wired, 2024). As a result, the legislation has not advanced beyond committee referral, leaving the United States reliant on a patchwork of sector-specific and state-based privacy laws.
The outcome is a system where Americans face both fragmented data exchange and fragmented data protection, undermining trust in digital public services and complicating any transition toward a citizen-centric digital infrastructure.
The High Cost of Fragmentation
This patchwork system isn’t just inconvenient; it also bleeds billions of dollars. When agencies can’t reliably identify people, deliver payments quickly, or cross-check data, waste and fraud increase. Here are just a few examples:
Improper Payments. In FY2023 the federal government reported an estimated $236 billion in improper payments. That astronomical sum (almost a quarter-trillion dollars) stemmed from issues like payments to deceased or ineligible individuals and clerical errors. In fact, over 74% of the improper payments were overpayments The largest drivers included Medicare/Medicaid billing mistakes and identity-verification failures in pandemic relief programs. For example, the Pandemic Unemployment Assistance program alone saw an increase of $44 billion in erroneous payments, as identity thieves and imposter claims slipped through weak verification checks. While not all improper payments can be eliminated, a significant portion, GAO notes, can be eliminated. The biggest share of improper payments results from documentation and eligibility verification weaknesses, not intentional fraud. All errors could be reduced with better digital identity and data sharing systems.
Identity Theft and Fraud. American consumers are suffering a wave of identity-related fraud. In 2023, the Federal Trade Commission received over 1 million reports of identity theft such as credit cards opened in another person’s name or fraudsters hijacking unemployment benefits. Identity theft now accounts for about 17% of all consumer fraud reports. The surge during the pandemic (when government aid became a target) showed how criminals exploit weak ID verification. State unemployment systems, for instance, paid out a significant sum to fraudsters who used stolen identities. Strengthening the digital ID infrastructure in U.S. could curb these losses by catching imposters before payments go out.
Administrative Overhead. Fragmentation forces each agency and company to reinvent the wheel, at great expense. Consider identity proofing: federal agencies spent over $240 million from 2020–2023 on contracts for login and ID verification solutions, much of it to third-party vendors, despite overlapping functionality. States and private institutions likewise pour resources into redundant systems for onboarding and verifying users. Processing paper documents and manual checks adds further costs and an indirect cost of time and frustration for citizens. A GAO report noted that agencies have widely varying systems and that a coordinated digital identity approach could improve security and save money. In short, the lack of shared public digital infrastructure means higher costs and slower service across the board.
Plan of Action
What would a Digital Public Infrastructure Act do?
It’s clear that the status quo isn’t working. The U.S. needs a Digital Public Infrastructure (DPI) Act, a comprehensive federal law that would build the rails and rules for secure, efficient digital interactions nationwide. Just as past Congresses invested in highways and the internet itself, Congress today should invest in core digital systems to serve as public goods. A DPI Act could establish three pillars in particular:
Federated, Privacy-preserving Digital Identity
A secure digital ID that Americans can use (voluntarily) to prove who they are online, without creating a centralized “Big Brother” database. This would be a federated system, meaning you could choose from multiple trusted identity providers. For example, you could share your identification with your state DMV, the U.S. Postal Service, or a certified private entity, all adhering to common standards. The federated system must follow the latest NIST digital identity guidelines for security and privacy (e.g. NIST SP 800-63) to ensure high Identity Assurance Levels.
Crucially, it should be privacy-preserving by design: using techniques like encrypted credentials and pairwise pseudonymous identifiers so that each service you log into only sees a unique code, not your entire identity profile. A federated approach would leverage existing ID infrastructures (state IDs, passports, social security records) without replacing them. Instead, it links and elevates them to a digital plane.
Under a DPI Act, an American citizen might verify their identity once through a trusted provider and then use that digital credential to access any federal or state service, open a bank account, or consent to a background check, with one login. This approach can dramatically reduce fraud (no more 5 different logins for 5 agencies) while protecting civil liberties by avoiding any single centralized ID database. The Act could establish a national trust framework (operating under agreed standards and audits) so that a digital ID issued in, say, Colorado is trusted by a bank in New York or a federal portal, just as state driver’s licenses are mutually recognized today. Done right, a digital ID saves time and protects privacy: imagine applying for benefits or a loan online by simply confirming a verified ID attribute (e.g. “I am Alice, over 18 and a U.S. citizen”) rather than scanning and emailing your driver’s license to unknown clerks.
Universal, Real-time Payments (G2P, P2G, P2P)
The DPI Act should ensure that instant payment capability becomes as ubiquitous as email. This likely means leveraging FedNow, the Federal Reserve’s new instant payment rail, and expanding its use. For Government-to-Person (G2P) payments, Congress could mandate that federal disbursements (tax refunds, Social Security, veterans’ benefits, emergency relief, etc.) use a real-time option by default, with an ACH or card fallback only if a recipient opts out.
No citizen should wait days or weeks for funds that could be sent in seconds. The same goes for Person-to-Government (P2G) payments: taxes, fees, and fines should be payable instantly online, with immediate confirmation. This reduces float and uncertainty for both citizens and agencies. Finally, Person-to-Person (P2P): while the government doesn’t run private payment apps, a robust public instant payments infrastructure can connect banks of all sizes, enabling truly universal P2P transfers. This way, someone at Bank A can instantly pay someone at Credit Union B without needing both to join the same private app.
FedNow, as a public utility, is an important player, but the Act could incentivize or require banks to join so no institution is left behind. The result would be a seamless national payments system where money moves as fast as email, enabling things like on-demand wage payments, rapid disaster aid, and easier commerce.
Cross-sector, Consent-based Data Exchange
The third pillar is perhaps the most forward-looking: creating standard protocols for data sharing that put individuals in control. Imagine a secure digital pipeline that lets you, the citizen, pull or push your personal data from one place to another with a click – for instance, authorizing the IRS to share your income info directly with a state college financial aid office, or allowing your bank to verify your identity by querying a DMV record (with your consent) instead of asking you to upload photos or scans.
A DPI Act can establish an open-data exchange framework inspired by efforts like open banking and TEFCA, but broader. This framework would include technical standards (APIs, encryption, logging of data requests) and legal rules (what consents are needed, liability for misuse, etc.) to enable “tell us once” convenience for the public.
Importantly, it must be consent-based: your data doesn’t move unless you approve and authorize it.It can let you carry digital attestations i.e. driver’s license, vaccination, veteran status, etc. on an e-wallet and share just the necessary bits with whoever needs to know. Some building blocks already exist: the federal Office of the National Coordinator for Health IT (ONC) is working on health data interoperability through TEFCA (so hospitals can query each other’s records), and the Consumer Financial Protection Bureau has begun rulemaking to give bank customers the right to share their financial data with third-party apps.
A DPI Act could unify these efforts under one umbrella, extend them to other domains, and fill in the gaps (for instance, enabling portable eligibility, if you qualify for one program, easily prove it for another). It could establish a governance entity or standards board to oversee the trust frameworks needed. Crucially, this must be accompanied by strong privacy and security measures like audit trails, encryption, and an emphasis that individuals can see and control who accesses their data. An example of this is how the EU wallet provides a dashboard for users to review and revoke data sharing.
The Digital Public Infrastructure Act would not necessarily build each piece from scratch but set national standards and provide funding to knit them together. It could, for example, direct NIST and a multi-agency task force to implement a federated ID by a certain date (building on Login.gov’s lessons), require the Treasury and Federal Reserve to ensure every American has a route to instant payments across platforms (leveraging FedNow), and authorize pilot programs for cross-sector data exchange in key areas like social services.
Precedent for such an approach already exists in bipartisan efforts:
Navigating Roadblocks: Federalism, Privacy, and Tech Contractors
Enacting a U.S. Digital Public Infrastructure Act will face several real challenges. It’s important to acknowledge these roadblocks and consider strategies to overcome them:
Federalism and Decentralized Authority
Unlike many countries where a central government can launch a national ID or payments platform by decree, the U.S. must coordinate federal, state, and local authorities. Identity in the U.S. is traditionally a state domain (driver’s licenses, birth certificates), while federal agencies also issue identifiers (Social Security numbers, passports). A DPI solution must respect these layers. States may fear a federal takeover of their DMV role, and agencies might guard their IT turf. Solution: design the system as a federation of trust. The Act could explicitly empower states by providing grants for states to upgrade to digital driver’s licenses (the Improving Digital Identity Act proposed in 2022 did exactly this, offering grants for state DMV mobile IDs). It could also create a governance council with state CIOs and federal officials to jointly set standards.
Civil Liberties and Privacy Concerns
Any mention of a “digital ID” in America raises eyebrows about Big Brother. Civil liberties advocates will rightly question how to prevent government overreach or mass surveillance. The Act should incorporate privacy by design provisions e.g., require minimal data collection, mandate independent audits for security, and give users legal rights over their data. One promising approach is using decentralized identity technologies, where your personal data (like credentials) stay mostly on your device under your control, and only verification proofs are shared. Also, the law can explicitly forbid certain uses, for instance, prohibit law enforcement from fishing through the digital ID system without a warrant, or forbid using the digital ID for profiling citizens. Including groups like the ACLU and EFF in the drafting process could help address concerns early. It’s worth noting that privacy and security can actually be enhanced by a good digital ID: today, Americans hand over copious personal details to random companies for ID checks (e.g. scan of your driver’s license to rent an apartment, which might sit in a landlord’s email forever). A federated ID could reduce exposure by only transmitting a yes/no verification or a single attribute, rather than a photocopy of your entire ID. Conveying that narrative, that this can protect people from identity theft and data breaches, will be key to overcoming knee-jerk opposition. Still, robust safeguards and perhaps a pilot phase to prove the concept will be needed to convince skeptics that a U.S. digital identity won’t become a surveillance tool.
Incumbent Resistance (Big tech and Contractors)
There are vested interests in the current disjointed system. Large federal IT contractors and identity verification vendors profit from selling agencies one-off solutions; big tech companies dominate payments and data silos in the status quo. A unified public infrastructure could be seen as competition or a threat to some business models. For example, if a free government-backed digital ID becomes widely accepted, companies like credit bureaus (which sell ID verification services) or ID.me might lose market share. If open-data sharing is mandated, banks that monetize data might push back. The solution is to engage industry so they can find new opportunities within the ecosystem. Many banks, for instance, actually support digital ID because it would cut fraud costs for them. The banking industry has been calling for better ID verification to fight account takeover and synthetic identities. In fact, a coalition of financial institutions endorsed the earlier Improving Digital Identity legislation.
Fintechs will favor Digital Public Infrastructure (DPI) because it transforms customer acquisition from a slow, expensive manual process into an instant, low-cost digital utility. By plugging into standardized government layers for identity (e-KYC) and data sharing (Account Aggregators), fintechs can instantly verify and underwrite users who lack traditional credit histories. This allows them to scale rapidly and profitably serve millions of previously “unbanked” customers by making lending decisions based on real-time data rather than rigid credit scores.. The Act can create a public-private task force (as earlier bills proposed) to hash out implementation. For government contractors, the reality is that building DPI will still require significant IT work, just more standardized. Contractors who adapt can win contracts to build the new infrastructure.
Political Will and Public Perception
DPI can be a bipartisan win if framed correctly.
For conservatives and fiscal hawks: emphasize the anti-fraud, waste-cutting angle. Stopping improper payments (recall that $236B figure!) and preventing identity theft aligns with the goal of efficient government. The Act essentially plugs leaky buckets, something everyone can get behind.
For liberals and tech-progressives: emphasize equity and empowerment. How digital infrastructure can help the unbanked access financial services, ensure eligible people aren’t left out of benefits, and give individuals control of their own data (a pro-consumer, anti-monopoly stance). Indeed, digital public goods are often framed as a way to ensure big tech doesn’t exclusively control our digital lives.
The key will be avoiding hot button mis-framings: this is not a surveillance program, not a national social credit system, etc. It’s an upgrade to basic government digital infrastructure. One strategy is to start with pilot programs and voluntary adoption to build trust. For example, the Act could fund a pilot in a few states to link a state’s digital driver’s license with federal Login.gov accounts, showing a working federated ID in action. Or pilot using FedNow for a chunk of tax refunds in one region. Early successes will create momentum and help refine the approach. Champions in the Congress will need to communicate that this is infrastructure in the truest sense: just as U.S. needed electrification and interstate highways, it now needs the digital equivalent to keep America competitive and secure.
Conclusion
A Digital Public Infrastructure Act represents more than a technical upgrade; it is an investment in America’s institutional capacity. The challenges the U.S. faces today like identity theft, improper payments, slow benefit delivery, and fragmented data governance are the predictable consequences of an outdated public digital foundation that has never been treated as national infrastructure. Just as the interstate highway system knit together the physical economy, and just as the early internet created the backbone for the digital economy, the United States now needs a unified, secure, and interoperable set of digital rails to support the next era of public service delivery and economic growth.
Unlike centralized systems elsewhere in the world, the American version of DPI would be federated, privacy-preserving, and deeply respectful of federalism. States would remain primary issuers of identity credentials. Private innovators would continue to build consumer-facing services. Federal agencies would govern standards rather than run monolithic platforms. This hybrid model plays to America’s institutional strengths such as distributed authority, competitive innovation, and strong civil liberties protections.
Congress must enact a Digital Public Infrastructure Act, a recognition that the government’s most fundamental responsibility in the digital era is to provide a solid, trustworthy foundation upon which people, businesses, and communities can build. America has done this before when it built the railroads, electrified the nation, and invested in the early internet. The next great public works project must be digital.
Increasing the Value of Federal Investigator-Initiated Research through Agency Impact Goals
American investment in science is incredibly productive. Yet, it is losing trust with the public, being seen as misaligned with American priorities and very expensive. To increase the real and perceived benefit of research funding, funding agencies should develop challenge goals for their extramural research programs focused on the impact portion of their mission. For example, the NIH could adopt one goal per institute or center “to enhance health, lengthen life, and reduce illness and disability”; NSF could adopt one goal per directorate “to advance the national health, prosperity and welfare; [or] to secure the national defense”. Asking research agencies to consider person-level or economic impacts in advance helps the American people see the value of federal research funding, and encourages funders to approach the problem holistically, from basic to applied research. For almost every problem there are different scientific questions that will yield benefit over multiple time scales and insight from multiple disciplines.
This plan has three elements:
- Focus some agency funding on measurable mission impacts
- Fund multiple timescales as part of a single plan
- Institutionalize the impact funding process across science funders
For example, if NIH wanted to reduce the burden of Major Depression, it could invest in a shorter time frame to learn how to better deliver evidence-based care to everyone who needs it. At the same time, it can invest in midrange work to develop and test new models and medications, and in the decades-long work required to understand how the exosome influences mood disorders. A simple way to implement this approach would be to build on the processes developed by the Government Performance Results Act (GPRA), which already requires goal setting and reporting, though proposals could be worked into any strategic planning process through a variety of administrative mechanisms.
Challenge and Opportunity
In 1945, Vannevar Bush called science the ‘endless frontier’, and argued funding scientific research is fundamental to the obligations of American government. He wrote “without scientific progress no amount of achievement in other directions can insure our health, prosperity, and security as a nation in the modern world”. The legacy of this report is that health, prosperity, and security feature prominently in the missions of most federal research agencies (see Table 1). However, in this century we have begun to drift from his focus on the impacts of science. We have the strange situation where our enterprise is both incredibly productive, and losing trust with the public, viewed as out of touch or misaligned with American priorities. This memo proposes a simple solution to address this issue for federal funding agencies like NIH and NSF that largely focus on extramural investigator-initiated research. These are research programs where the funding agency signals interest in specific topics and teams of scientists submit their research plans addressing those topics. The agency then funds a subset of those plans with input from external scientific reviewers.
This funding approach is incredibly productive. For example, NIH funds most of the pipeline for the emerging bioeconomy, which accounts for 5.1% of our GDP. From 2010 to 2016, every one of the 210 new entities approved by the FDA had some NIH funding. And yet, there appears to be a disconnect between our funding strategy and the public interest focus of the Endless Frontier operationalized through our federal science agency missions for investigator initiated research.
A fundamental driver of this disconnect might be a slight misalignment of the incentives of academic scientists, who are rewarded for novelty and scientific impact, with the broader public interest. Our federal agencies are highly attuned to scientific leaders, and place equal or even greater weight on innovation (novelty plus scientific impact) than real world impact. For example, NSF review criteria place equal weight on intellectual merit (‘advance knowledge’) and broader impacts (‘benefit society and contribute to the achievement of specific, desired societal outcomes’). NIH’s impact score of new applications is an ‘assessment of the likelihood for the project to exert a sustained, powerful influence on the research field(s) involved’ [emphasis mine], which is only part of the agency’s mission. The practical implications of this sustained focus away from the impact portion of agencies missions become apparent in figure 1, showing tremendous spending in health research unrelated to a key public interest measure like lifespan, especially when compared to other nations’ health research spending.
Perhaps the realization that the federal research investment is not strongly linked to their mission impact is one reason why American science has been slowly losing public trust over time. Among the people of 68 nations ranking the integrity of scientists, Americans ranked scientists 7th highest, whereas we ranked scientists 16th highest in our estimation of them acting in the public interest. And this is despite the fact that the American investment in science is many times higher than the 15 nations who rated scientists more highly on public interest. A more accurate description of our 21st century federal science enterprise might be the ‘timeless frontier’, where our science agencies pursue cycles of funding year in and year out, with their functional goal being scientific changes and their primary measure of success being projects funded. Advancing the economy, health, national defense, etc., are almost incidental benefits to our process measures.
We can do better. In 2024, the National Academy of Medicine called out the lack of high level coordination in research funding. In 2025, the administration has been making drastic cuts and dramatic changes to goals and processes of federal research funding, and the ultimate outcome of these changes is unclear. In the face of this change, Drs. Victor Dzau and Keith Yamamoto, staunch champions of our federal science programs, are calling for “a coherent strategy […] to sustain and coordinate the unrivaled strengths of government-funded research and ensure that its benefits reach all Americans”.
We can build on the incredible success of the federal science enterprise – inarguably the most productive science enterprise in all history. The primary source of American scientific strength is scale. American funding agencies are usually the largest funders in their space. I will highlight some challenges of the current approach and suggest improvements to yield even more impactful approaches more closely aligned with the public interest.
The primary federal funding strategy is broad diversification, where our agencies fund every high scoring application in a topic space (see FAQs). Further, federal science agencies pay little attention to when they expect to see a fundamental impact arising from their research portfolio. For example, a centrally directed program like the Human Genome Project can lead to breakthrough treatments decades later, but in the meantime, other research that generates improvements on faster timescales could have been coordinated, such as developing conventional drug treatments, or research to optimize quality and delivery of existing treatment.
And yet, the breadth and complexity of broad diversification makes it easy to cherry pick successes. This is a strategic issue, and is bigger than the project selection issues highlighted in the earlier discussion about review criteria. When research funding agencies make their pitch for federal dollars they highlight a handful of successes over tens of thousands of projects funded over many years. They ignore failures, the time when investments were made, and time to benefit. With the goals and metrics we have in place, it is simply too hard to summarize progress in any other way.
Overly diversified science funding supports both good Congressional testimony and bad strategy. If your problem happens to fall into a unicorn space of success, there is a lot to celebrate. But most problems do not, and we experience inconsistent returns. We need to define the success of research funding more precisely, in advance, and in ways that more obviously align with the public interest.
Plan of Action
If we tweak our funding strategy to focus on societal impacts, we can move to a more impactful science enterprise, and help regain public support for science funding. We can focus federal research funding on effective answers to difficult problems demanding both urgency and short term improvements, and fundamental discoveries that may take decades to realize. My solution and implementation actions for agencies, and potentially Congress, are described below.
Recommendation 1. Focus some agency funding on measurable mission impacts.
We should empower our science agencies to step away from broad diversification as the predominant funding strategy, and pursue measurable mission impacts with specific time horizons. It can be a challenge for funders to step away from process measures (e.g. projects or consortia funded) and focus on actual changes in mission impact.
Ideally, these specific impacts would be broken into measurable goals that would be selected through a participatory process that includes scientific experts, people with lived experience of the issue, and potential partner agencies. I recommend each agency division (e.g. an NSF Directorate) allocate a percentage of their budget to these mission impact strategies. Further, to avoid strategic errors that can arise from overwhelming power of federal funding to shape the direction of scientific fields, these high level funding plans should be as impact focused as possible, and avoid steering funding to one scientific theory or discipline over another.
Recommendation 2. Fund multiple timescales as part of a single plan.
Research funders need to balance their investment portfolios not only across problem areas, but over time. Complex challenges will often require funding different aspects of the solution on different timelines in parallel as part of a larger plan. Balancing time as well as spending allows for a more robust portfolio of funding that draws from a broader array of scientific disciplines and institutions.
Note, this approach means starting lines of research that may not lead to ultimate impact for decades. This approach might seem strange given our relatively short budget cycles, but is very common in science, where projects like the Human Genome initiative, the Brain Initiative, or the National Nanotechnology Initiative, have all exceeded a single budget cycle and will take years to realize their full impact. These kinds of efforts require milestones to ensure they stay on track over time.
Recommendation 3. Institutionalize the impact funding process across science funders.
Our research enterprise has become oriented around investigator-initiated, project-based awards. Alternative funding strategies, such as the DARPA model, are viewed as anomalies that must require completely different governance and procedures. These differences in goals are unnecessary. A consistent focus on impacts and strategy in funding across agencies will help the scientific community become more aware of the time to benefit of research, help underscore the value of research investment to the American public, and help research agencies collaborate among themselves and with their partner agencies (e.g. NIH collaborates more closely with CMS, FDA, etc.).
In short, institutionalizing this process can lead to greater accountability and recognition for our science enterprise. This structure allows our funders to report to the public progress on specific goals on predetermined and preannounced timelines, rather than having to comb through tens of thousands of independent funding decisions and competing strategies to find case studies to highlight. In this way, expected and unexpected scientific results, and even operational challenges, can be discussed within an impact framework that clearly ties to the agency mission and public interest.
Example of Planning using an Impact Focus
Here is an example of a mission impact goal Reducing the Burden of Major Depressive Disorder that could be put forth by the National Institute of Mental Health (NIMH), and the process to develop it.
Commence Inclusive Planning: NIMH brings together experts from academia, clinical care, industry, people impacted by depression, and FDA and CMS to develop measures, timelines and funding strategies.
Develop Specific Impact Measures: These should reflect the agency’s impact portion of their mission. For example, NIH’s mission impact of “enhance health, lengthen life, and reduce illness and disability” requires measuring impact on human beings. Example measurement targets could include:
- Reduced incidence of Major Depressive Disorder
- Increased productivity (e.g. days worked) of people living with Major Depressive Disorder
- Reduced suicide rates
Fund Multiple Time Scales: Designate time scales in parallel as part of a comprehensive strategy. These different plans would involve different disciplines, funding mechanisms, and private sector and government partners. Examples of plans working at different timescales to support the same goal and measures could include:
- 10 year plan: Increase utilization of evidence based care
- 15 year plan: Develop and implement new treatments
- 30 year plan: Determine how the exposome causes and prevents depression, and how can be changed
- It is likely that NIMH has already obligated funds to projects that support one of these plans, though they may need additional work to ensure that those projects can directly tie to the specific plan measures.
Implementation Strategies for Impact Goals
Each federal funding agency could allocate a percentage of their budget to these and other impact goals. The exact amount would depend on the current funding approach of each agency. As this proposal calls for more direct focus on agency mission, and not a change in mission, it is likely that a significant percentage of the agency’s current budget already supports an impact goal on one or more of its time scales.
For an agency heavily weighted towards project based funding of small investigator teams, like NIH, I would recommend starting with a goal of 20% of their budgets set towards impact spending and consider increases over time. Other agencies with different funding models may want to start in a different place. Further, I would recommend different goals and targeted funds for each major administrative unit, such as an institute or directorate.
All federal funders already engage in some form of strategic and budget planning, and most also have formal structures for engaging stakeholders into those planning decisions. Therefore, each agency already has sufficient authorities and structures to implement this proposal. However, it is likely that these impact goals will require collaboration across agencies, and that could be difficult for agencies to efficiently conduct by themselves.
Additional support to make this change could come from Congressional Report language as part of the budget process, through interagency leadership from the White House Office of Science and Technology, or through the Office of Management and Budget. For example, the Government Performance Results Act (GPRA) already requires agency goal setting, reporting and supports cross agency priority goals. That planning process could easily be adapted to this more specific impact focus for research funding agencies, and reporting on those goals could be incorporated into routine reporting of agency activities.
Conclusion
We are living through a massive disruption in federal research funding, and as of the fall of 2025, it is not clear what future federal research funding will look like. We have an opportunity to focus the incredibly productive federal research enterprise around the central reasons why Americans invest in it. We can meet Bush’s challenge of the Endless Frontier simply by clearly defining the benefits the American people want to see, and explicitly setting plans, timing and money to make that happen.
We can call our shots and focus our science funding around impacts, not spending. And we can set our goals with enough emotional resonance and depth to capture both the interests of the average American, and the needs of scientists from different disciplines and types of institutions. We already have the legal authorities in place to adopt these techniques, we just need the will.
Inadvertently, the huge scale of federal funding could lead to a monopsonistic effect. In other words, NIH’s buying power is so large, if NIH does not fund a specific type of research, people may stop studying it. This risk is highest within a narrow scientific field if there is a bias in grant selection. A well publicized example being NIH’s strong funding preference to one theory of Alzheimer’s Disease to the diminishment of competing theories, which in turn influenced careers and publication patterns to contribute to that bias.
Tax Filing as Easy as Mobile Banking: Creating Product-Driven Government
Americans trade stocks instantly, but spend 13 hours on tax forms. They send cash by text, but wait weeks for IRS responses. The nation’s revenue collector ranks dead last in citizen satisfaction. The problem isn’t just paperwork — it’s how the government builds.
The fix: build for users, not compliance. Ship daily, not yearly. Cultivate talent, don’t rent it. Apple doesn’t outsource the creation of its products; the IRS shouldn’t outsource taxpayer experience. Why?
The goal: make taxes as easy as mobile banking.
The IRS, backed by a Congress and an administration that truly wants real improvements and efficiencies, must invest in building its tax products in house. Start with establishing a Chief Digital Officer (CDO) at the IRS directly reporting to the Commissioner. This CDO must have the authority to oversee digital and business transformation across the organization. This requires hiring hundreds of senior engineers, product managers, and designers—all deeply embedded with IRS accountants, lawyers, and customer service agents to rebuild taxpayer services. This represents true government efficiency: redirecting contractor spending to fund internal teams that build what American taxpayers should own rather than rent.
This is about more than broken technology. This is a roadmap for building modern, user-centric government organizations. The IRS touches every American, making it the perfect lab for proving the government can work.
Transform the IRS first, then apply these principles across every agency where citizens expect digital experiences that actually work.
Challenge & Opportunity
It’s April 15th. For the first time, you’re not fretting.
You finished filing your taxes on a free app. It took 15 minutes. Your income? Already there. Your credits? Pre-calculated and ready to claim. Your refund? Hitting your bank account tomorrow.
For millions around the world, swift, painless tax filing isn’t a dream. It’s the norm. It should be for Americans, too.
But in the U.S., the IRS experience is still slow, opaque, process-heavy, and frustrating. Tax filing is one of the few universal interactions Americans have with their government—and it’s not one that earns much trust.
It doesn’t have to be this way. We were on the path to delivering that with IRS Direct File and needed to recommit. To deliver wildly easier taxes for Americans, we can, and must, build an IRS that meets high modern expectations: fast, transparent, digital-first, and relentlessly taxpayer-focused.
The Diagnosis
Each year, the IRS collects more than 96% of the revenue that funds the federal government—$5.1 trillion supporting everything from Social Security, defense, infrastructure, veterans’ services, and investing in America’s future.
The quote from Justice Oliver Wendell Holmes, carved into the limestone face of the IRS headquarters in D.C., captures the spirit well:
“Taxes are what we pay for civilized society.”
It is not only essential to the functioning of government—it is also a major way most Americans interact with it. And that experience? Frustrating, costly, and confusing. According to a recent Pew survey, Americans rate the IRS less favorably than any other federal agency. The average taxpayer spends 13 hours and $270 out of pocket just to file their return.
The core problem: The IRS needs to be user-focused.
Despite the stakes, the IRS operates far behind what Americans expect. We live in a world where people can tap to pay, split bills by text, or trade stocks in slick apps. But that world does not include the IRS.
A staggering 63% of the 10.4 billion hours Americans spend dealing with the federal government are consumed by IRS paperwork. But much of the source of that pain isn’t the IRS, but Congress with the crushing complexity of decades long tax code changes, sedimented on top of each other. This year was no different. The “One Big Beautiful Bill” runs 331 pages, with large swaths devoted to new, intricate tax changes.
Dealing with the IRS still often involves paper forms, long phone waits, chasing down documents, and confusing processes.
If you’ve dealt with the IRS for anything beyond filing, it feels impossible to get a task finished. Will someone pick up the phone? Can I get an answer to my questions and resolve my situation? Would I expect the same answer if I talked to someone else? Last year the IRS answered just 49% of the 100 million calls it received, including automated answering.
This underperformance is beyond outdated technology—it’s structural and institutional. The IRS’s core systems are brittle and fragmented. Ancient procurement rules and funding constraints have made sustained modernization nearly impossible. Siloed organizations sit within siloes. In place of long-term investment, the agency leans heavily on short-term contractor fixes, band-aids applied to legacy wounds.
This complexity has stymied scaled change.
The root cause: The IRS has never treated world-class technology and product development as mission-critical capabilities core to its identity, to be hired, owned, and continually improved by internal teams focused on user outcomes.
A modern service agency builds end-to-end experiences for users—from pre-populating data through to filing and refunds. Empowered teams building these features have a holistic viewpoint and control over their service to ensure taxpayers are able to repeatedly and reliably complete their task.
Today’s reality is different: federal agencies like the IRS treat technical and product expertise as afterthoughts—all nice-to-haves that serve bureaucratic processes rather than core capabilities essential to their mission. Strategy and execution get outsourced by default. This creates a growing divide between “business” and “IT” teams, each lacking a deep understanding of the other’s work, despite both being critical to delivering services that actually function for taxpayers.
This outsourcing has hollowed out the agency’s internal technical capacity. Rather than building technical competency in-house, and paying that talent a salary approaching private companies, the IRS grows more dependent on vendors. It no longer knows what it needs technically, what questions to ask or which paths to pursue. Instead they must trust the vendors–companies financially incentivised towards ballooning scopes, lock-in, and complexity.
The result: a siloed experience that mirrors a siloed organization, one that is risk-averse, paper-heavy IRS, too slow to meet modern expectations.
The agency approaches service delivery as a compliance and bureaucratic process to digitize, rather than a product to design. “Never ship your org-chart” is a common refrain you’ll hear at tech companies, to explain how products tend to take on the communication style of their builders. Yet IRS product faultlines visibly follow its org structure and thus fail to deliver a holistic experience.
There were bright spots. Direct File showed what’s possible when empowered teams build for users. A dead simple idea: let Americans file taxes directly on the IRS site was a reality. It worked. It was well regarded. In surveys, users beamed about Direct File: 9 out of 10 gave it an “excellent” or “above average” rating, 74% said they preferred it over what they used before, and 86% said it increased their trust in the IRS.
The government actually delivered for its citizens, and they felt it.
But it didn’t last. The project was abruptly dismantled due to political ideology, not taxpayer experience or feedback.
Many of the people with the technical skills and vision to modernize the IRS have left, often without a choice. The agency will likely slide further backward—into deeper dependence on systems built by the lowest bidder or those currying political favor, with poorer service and diminished public trust in return.
We’ve seen this up close.
Both of us worked at The White House’s technology arm; the U.S. Digital Service. One of us helped lead Direct File into existence and built the Consumer Financial Protection Bureau’s digital team. The other previously led Google’s first large language model products and prototyped AI tools at the IRS to streamline internal knowledge work.
In our work at the IRS, we witnessed how far the agency must go. Inside the IRS Commissioner’s office, with leaders across the agency, we built a collaborative digital strategic plan. This memo details those proposals since left by the wayside after seven different IRS commissioners rotated in the seat, just this year.
The IRS needs more than modernization. It will need a systemic rebuild from:
- compliance, to user-centered design and product thinking
- vendor dependence to empowered internal product teams
- once-a-year panic to real-time, year-round services
- fragile mainframes to composable platforms and APIs
- waterfall contracting to iterative, continuous delivery
We’re sharing these recommendations for a future Day One—when there’s a refocus on rebuilding the government. When that day comes, the blueprint will be here: drawn from inside experience, built on hard lessons, and focused on what it will take to deliver a digital IRS that truly works for the American people.
What we need is the mandate to build a tax system that makes Americans think: “That was it? That was easy.”
Plan of Action
The IRS must rebuild taxpayer services around citizen needs rather than compliance and bureaucratic processes. This requires in-housing the talent to strategically build it. We propose establishing a Chief Digital Officer directly reporting to the Commissioner, with the authority to oversee digital and business transformation across the organization, hire hundreds of senior engineers, product managers, and designers. The goal, a team empowered to deliver a tax-filling product experience that meets modern expectations.
The Products
Build for Users, Not Internal Compliance
We’ve become accustomed to a user-focused fit-and-finish in the app era. Let’s deliver that same level for taxpayers.
It all starts around building a digital platform that empowers taxpayers, businesses, and preparers with the information, tools and services to handle taxes accurately and confidently. A fully-featured online account becomes the one-stop, self-service hub for all tasks. Taxpayers access their complete tax profile, updated in real-time, with current data across income sources, financial institutions, and full tax history. The system proactively recommends tax breaks, credits, and withholding adjustments they’re eligible for.
Critically, this can’t be built in a vacuum. It requires rapid iteration with users as part of a constant feedback loop. This digital platform runs on robust APIs that power internal tools, IRS public sites, and third-party software. Building this way ensures alignment across IRS teams, eliminates duplicate efforts, and lifts the entire tax software ecosystem.
This is what we need to build for Americans:
Online tax filing: From annual panic to year-round readiness
Reboot Direct File. Stop forcing everything into tax season. Let taxpayers update information year-round—add a child, change addresses, adjust withholdings, upload documents. When April arrives, their return is already 90% complete.
This is a natural evolution of Direct File and the existing non-editable online account dashboard into a living, breathing system taxpayers optimize throughout the year. And not just for individuals—this should be extended to businesses—reducing this burden for as many filer types as possible.
Pre-populated returns: Stop making people provide what the IRS already knows
The IRS already has W-2s, 1099s, and financial data. Use it. Pre-populate returns to cut filing time from hours to minutes. Deliver secure APIs so any tax software can access IRS data (with taxpayer permission), and use machine learning to flag issues including fraud before submission. This increases accuracy, reduces errors, and spurs competition by making it easy to switch between tax-filing programs.
Income verification as a service: Turn tax data into financial opportunity
The IRS sits on verified income data that could help Americans access government services, credit, mortgages, and benefits like student aid. Instead of weeks-long transcript requests, offer instant verification through secure APIs. This creates a government-backed source alongside credit bureaus, increases financial access, and reduces paperwork across all government services.
Tax calculator as a platform: One source of truth
Every tax software company recreates the same calculations, each slightly different. Across the organization, the IRS itself uses multiple third-party tax calculators in audits. This should be a core, integral service the IRS offers—build a definitive tax calculator as an API, the single source of truth that internal audits and checks use, and external software can access or run on their own. Make it transparent, auditable, and open source. Put up cash “bounties” to encourage the public to find bugs and errors and invite taxation-critics to review the code. Use generative AI to aid IRS accountants, lawyers and engineers translate tax law changes into code–speeding the roll out of Congressional tax changes.
When everyone calculates taxes the same way the IRS does, errors vanish. When everyone can see how the IRS does it, trust grows.
Modern MeF: From submission pipe to intelligent platform
Today’s Modernized e-File (MeF) is barely modern—it’s a dumb pipe that accepts tax returns and hopes for the best. Transform it into intelligent infrastructure that validates in real-time, catches errors immediately (not weeks later in confusing notices), and stops fraud before refunds are deposited. Build it like a real API, not XML dumps. Enable multi-part submissions so taxpayers can fix mistakes without starting over. This isn’t just a technical upgrade—it’s the foundation that makes every other improvement possible.
The Process
Ship Daily, Not Yearly
Taxpayer-first product development
The IRS is the single largest interaction point between Americans and their government. Every improvement saves millions of hours and builds trust. This requires abandoning bureaucratic processes for product thinking.
Build with taxpayers from day one through constant user testing and feedback loops. Organize around taxpayer journeys—”I need to update my withholdings” or “I’m checking my refund”—not org charts.
Measure what matters: time-to-file, satisfaction scores, error rates, not only compliance metrics. Internal Objectives and Key Results planning makes priorities clear and syncs the organization towards focused goals. Publish Service Level Objectives on external products to ensure we target creating systems that others can confidently rely and build on.
Give full-stack product teams the authority to make integrated technical, design, policy and legal decisions together. Staff these teams with internal technologists embedded alongside accountants and lawyers in functional organizations, building IRS competency while reducing contractor dependence. Today’s IRS is highly siloed across functions with authority so fragmented it’s unclear who “owns” what. Yet go to any top tech organization and you’ll see what we’re pushing for: aligned and cross-functional teams whose job is delivering with clear ownership. Inherently we’re pushing for more than a new team, we’re factoring out unclear ownership in general away from IT and Business Divisions.
When teams own outcomes, we can better ensure taxpayer experience transforms from painful to painless.
API-first architecture
The IRS is fundamentally a data organization, yet information flows through siloed systems that can’t talk to each other. Amazon solved this with a simple mandate: all teams must expose their data and communicate through APIs. (This mindset set in motion the seeds of Amazon Web Services, the company’s most profitable division).
The IRS needs the same revolution.
Every team exposes data and functionality through standardized REST APIs—no direct database access, no per-department clones of the data, no exceptions. Design every API to be externalizable (with strong access controls) from day one, unlocking government APIs to become platforms for innovation. When systems communicate through versioned APIs instead of tangled dependencies, teams can ship improvements daily without compromising everything else. This isn’t just technical architecture—it’s how modern organizations move fast without breaking things.
The People
Cultivate it, Don’t Outsource It; Build a Delivery Culture
A digital IRS that delivers for Americans cannot be built by the lowest bidder. Its core capability isn’t digitized forms–it’s people who can understand taxpayers’ needs, imagine solutions, design thoughtfully, ship them fast, listen to users, and keep improving based on feedback.
Silicon Valley understands this instinctively on two fronts. The fight for great engineers is the fight to build teams that can deliver great products. And two, no leading tech company outsources its own R&D. Delivering well-functioning and beloved products requires tight ownership of the product iteration loop.
Businesses long learned to never outsource a core competency. OpenAI would never outsource the training of its models, Apple its industrial design, Google its search algorithm, or Facebook its social graph. The same should be true for the IRS.
Yet, despite accepting 93% of its tax returns digitally, it still does not consider itself to be a digital-first agency. Building great teams is inseparable from building great taxpayer experiences. For decades, the agency has outsourced its technical mission and vision.
What we witnessed at the IRS was often vendor theater. Consultants transformed routine meetings into sales presentations that should have been dedicated to improving the products. Solutions specialists added layers of proprietary middleware, despite readily available enterprise-grade open source solutions running on commodity servers could easily meet the objectives. All of this unfolded within an organizational culture where securing contracts took precedence over delivering meaningful outcomes. Contracts that, of course, cost multiples more than the price of a competent internal team.
Commodities like cloud infrastructure or off-the-shelf software that serve broad, generic needs should absolutely be acquired externally. But the IRS’s critical, taxpayer-facing products—the systems at the heart of filing, payments, and taxpayer accounts—must be built and owned internally. There is only one agency that collects taxes for the United States of America.
When everything is handed to vendors, the IRS sends more than money out the door; it loses institutional memory, technical craft, quality systems, and the ability to move quickly. A modern IRS cannot be built on rented skills.
Talent: Build a Permanent Product Core
This transformation starts with the people: build and keep an in-house corps of top-tier technologists—engineers, product managers, designers, user experience researchers—working in small, empowered, cross-functional teams hand in hand with fellow IRS accountants, auditors, customer service representatives and lawyers. Not a handful of digital specialists scattered in a bureaucracy as it was, but several hundred people whose full-time job is delivering and evolving the IRS’s core taxpayer experiences and services.
- Create a dedicated Digital Profession inside the IRS, led by a Chief Digital Officer with the authority to hire, fire, and shape teams and technology stacks.
- Break the straitjacket of outdated civil service rules by creating specialist pay bands to compete for top talent like the CFPB has done.
- Empower cross-functional teams to ship without endless escalation. Start small, test early, iterate quickly, and make product decisions by those close to the work.
Funding: Invest in Teams, Not Projects
Current funding locks the IRS into one-off projects that end when the money runs out, leaving no path for iteration. A product-centered IRS needs enduring funding for enduring teams. Long-lived services, not short-lived milestones. This should be no surprise for a tax organization. There are two certainties in life; death and taxes. We should properly set ourselves up to manage the latter.
- Fund continuous development rather than one-and-done “delivery.”
- Tie funding to taxpayer outcomes like faster filing, fewer errors, higher satisfaction, instead of compliance checklists.
- Secure multi-year budgets for core product teams so they can improve services year-round, not scramble for appropriations each cycle.
This shift will reduce long-term capital costs and ensure that every dollar invested keeps improving the taxpayer experience.
Quality & Standards: Build Once, Build Right
Owning our products means owning their quality. That requires clear, enforceable service standards, like performance, usability, scalability, and accessibility, that every IRS product must meet.
- Establish service performance benchmarks and hold teams accountable to them. These should be highly taxpayer centric; time to file, support response time, ease of use.
- Create communities of practice inside the organization to share patterns, tooling, and lessons learned across the agency.
- Apply spend controls that tie contract renewals to measurable outcomes and prevent redundant vendor builds.
Culture Eats Strategy: Time to Invest in a Delivery Culture
“Culture eats strategy for breakfast,” as Peter Drucker famously said. Yet government agencies too often treat culture-building as off-limits or irrelevant. This is backwards. Creating a shared, collaborative culture centered on delivery isn’t just important; it’s the foundation that makes everything else possible. The hardest and most critical step is investing in people. Give employees space to collaborate meaningfully, contribute their expertise, and take ownership of outcomes. Leadership must empower teams with real authority, establish clear performance standards, and hold everyone accountable for meeting—or exceeding—those benchmarks. Without this cultural shift, even the best strategy becomes just another plan gathering dust.
When every product meets the same high standard, trust in the IRS will grow—because taxpayers will feel it in every interaction.
A template for all agencies
The IRS touches more Americans than any other federal agency–making it the perfect proof point that the government can deliver digital products that work seamlessly. The principles–build for users, not compliance, shipping daily, not yearly, and keeping the talent in house is not unique to the IRS.
We believe these goals and strategies apply to nearly every agency and level of government. Imagine Social Security retirement planning tools that lead to easy withholding adjustments, a Medicare/Medicaid that is easy to enroll in, or a FEMA with easy to file disaster relief disbursement.
Transform the IRS this towards this path, and then use these lessons to reset and lift up expectations between Americans and their government. One so easy citizens say: “That was it? That was easy.”